Interface Configurations - N10-008 CompTIA Network+ : 2.3
Summary
TLDRThis video covers essential configurations for switch interfaces, including speed, duplex settings, and Layer 3 IP configurations. It explains VLAN assignments, link aggregation, and port mirroring for troubleshooting. Key concepts like jumbo frames, flow control using pause frames, and 802.3x are also discussed. Additionally, it highlights the importance of port security, which restricts network access based on MAC addresses to prevent unauthorized connections. The video provides practical insights into optimizing network performance and securing switches in a professional environment.
Takeaways
- 🔌 Speed and Duplex settings are crucial for switch interfaces, and can be set to automatic or manually configured.
- ⚡ Speed options include 10-megabit, 100-megabit, 1-gigabit, and 10-gigabit Ethernet connections.
- 🔄 Duplex settings define how data is sent (half or full), and must match on both sides of the connection.
- 🌐 Layer 3 settings such as IP addresses, subnet masks, and default gateways are essential for switch interfaces.
- 🖥 VLAN assignments need to be set for each port on a switch, ensuring proper network segmentation.
- 🔗 Link Aggregation (LAG) or port bonding combines multiple connections for increased bandwidth between switches.
- 🛡 Port mirroring (SPAN) allows copying of traffic for packet analysis, either locally or across multiple switches.
- 📦 Jumbo frames increase Ethernet payload sizes, improving efficiency for large data transfers, but must be supported by all devices in the path.
- ⏸ 802.3x pause frames help manage traffic flow by signaling devices to slow down when overwhelmed.
- 🔒 Port security restricts access to the network based on MAC addresses, preventing unauthorized devices from connecting.
Q & A
What is the importance of matching speed and duplex settings on both sides of the wire?
-If the speed and duplex settings do not match on both sides of the wire, the network devices may experience communication issues, such as collisions or reduced performance. Matching the settings ensures smooth communication at the optimal speed and duplex mode.
What is a VLAN and why is it important to assign each port on a switch to a particular VLAN?
-A VLAN (Virtual Local Area Network) is a logical grouping of devices on a network that behave as if they are on the same physical LAN. Assigning each port to a VLAN ensures that devices on the same VLAN can communicate while maintaining separation between devices on different VLANs.
What is trunking, and how does it relate to VLANs?
-Trunking allows multiple VLANs to be transmitted over a single physical link between switches. It is used to maintain communication between the same VLANs across different switches while carrying traffic for multiple VLANs using VLAN tags.
What is link aggregation, and why is it used?
-Link aggregation, also known as LAG (Link Aggregation Group), allows multiple physical connections between switches to be combined into a single logical connection. This increases bandwidth and provides redundancy, ensuring better network performance and fault tolerance.
What is port mirroring and how is it useful for network administrators?
-Port mirroring, or SPAN (Switched Port Analyzer), copies traffic from one or more switch ports to another port where a network analyzer can capture and inspect the data. This is useful for monitoring network traffic and troubleshooting network issues.
What are jumbo frames, and when would they be used in a network?
-Jumbo frames are Ethernet frames with a payload larger than the standard 1,500 bytes, typically up to 9,216 bytes. They are used in networks where large file transfers or backups are common, improving efficiency by reducing the number of frames sent.
How does the 802.3x flow control standard help manage network traffic?
-The 802.3x flow control standard uses pause frames to temporarily stop data transmission when a device's buffer is full. This prevents buffer overflow and helps maintain efficient communication between devices.
What is port security, and how does it protect a network?
-Port security limits the number of MAC addresses that can connect to a switch port. It prevents unauthorized devices from accessing the network by either disabling the port or alerting the administrator when a violation occurs.
What is the difference between native VLANs and tagged VLANs?
-Native VLANs refer to untagged VLAN traffic that passes through a trunk port, while tagged VLANs have a VLAN tag added to their Ethernet header. The tag helps identify the VLAN to which the traffic belongs.
What happens if network devices are not configured to support jumbo frames?
-If network devices are not configured to support jumbo frames, they will either drop the oversized frames or fragment them, leading to inefficiency and possible communication problems between devices that expect to use jumbo frames.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes

Free CCNA | Configuring Interfaces | Day 9 Lab | CCNA 200-301 Complete Course

PPPoE Server & Client Configuration - MIKROTIK TUTORIAL [ENG SUB]
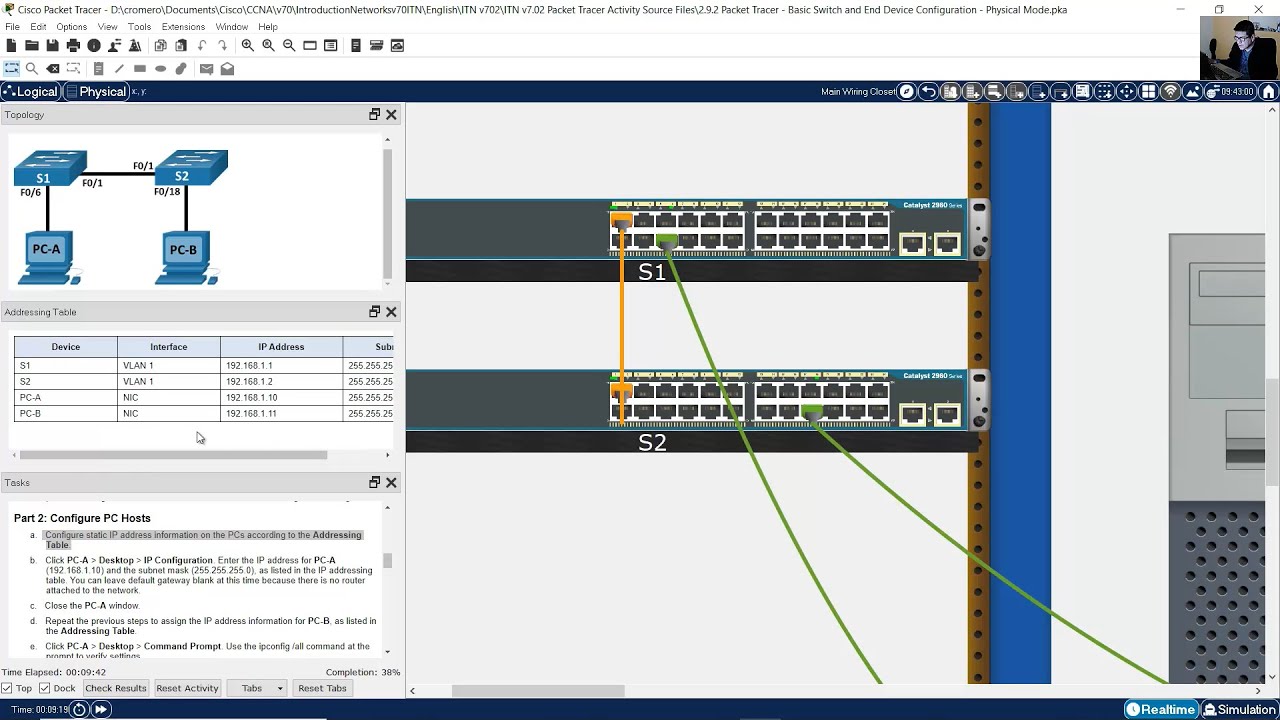
2.9.2 Packet Tracer - Basic Switch and End Device Configuration - Physical Mode
KONFIGURASI DASAR MIKROTIK (UNTUK PEMULA)

How to Configure VoIP Phones in Cisco Packet Tracer | Configure IP Phones Telephony Service
How to set up a WiFi router (wireless router) - Cisco Packet Tracer
5.0 / 5 (0 votes)
