5G Network Security Threat: Performing a DDOS Attack with UERANSIM
Summary
TLDRThis video tutorial demonstrates how to use UV9 sim to simulate a DDoS attack on an open 5G core network. It explains two potential attack vectors: disrupting the control plane with a signaling storm or choking the user plane after authentication. The presenter uses a single VM setup to illustrate the attack on the control plane, showing how to generate traffic to overwhelm the system, resulting in service disruption. The video concludes with a reminder of the importance of DDoS mitigation strategies in network development.
Takeaways
- 🚩 The video discusses using UV9 SIM to create a DDoS attack on a 5G core network.
- 📚 It explains two main ways to disrupt a 5G core network: attacking the control plane or choking the user plane.
- 🔐 To attack the user plane, an attacker must first be authenticated with the network.
- 📊 The video uses a diagram to illustrate how a DDoS attack can be implemented.
- 💻 Due to time constraints, a single VM setup is used, which limits the ability to use ping for data traffic.
- 📈 The presenter shows how to create a signaling storm by sending a large number of signaling messages.
- 🔄 The script demonstrates spinning up multiple instances of UEs to simulate a DDoS attack.
- 📉 The video highlights the impact of the attack on system resources, such as memory and CPU usage.
- 🚨 It warns that such attacks can cause network components like eNodeB to fail.
- 🛡️ The presenter emphasizes the importance of having DDoS mitigation capabilities for networks exposed to such attacks.
Q & A
What is the main topic of the video?
-The video discusses how to use UV9 Sim to create a DDoS attack, focusing on the technical aspects and potential scenarios.
What is UV9 Sim?
-UV9 Sim is a tool that can be used to simulate user equipment (UE) in a 5G network, which the video uses to demonstrate how DDoS attacks can be conducted.
Why does the presenter use a single VM setup for the demonstration?
-The presenter uses a single VM setup due to time constraints, but notes that it limits the ability to use ping for data traffic.
What are the two components of an open 5G core network mentioned in the video?
-The two components are the control plane, which handles signaling, and the user plane, which handles user data or UE traffic.
How can an attacker disrupt a 5G core network?
-An attacker can disrupt a 5G core network by either creating a packet storm to overwhelm the control plane or by choking the user plane after authenticating with the network.
What is a signaling storm in the context of the video?
-A signaling storm is a type of DDoS attack where a large number of signaling messages are sent to the network, overwhelming its ability to process signals.
What does the presenter mean by 'disruption of the user plane'?
-Disruption of the user plane refers to flooding the network with data traffic after authentication, which can overwhelm the network's capacity to handle user data.
How does the presenter demonstrate the creation of a signaling storm?
-The presenter demonstrates creating a signaling storm by using UV9 Sim to connect multiple UE instances to the network, causing a high volume of signaling traffic.
What is the impact of reducing the VM's memory and CPU on the demonstration?
-Reducing the VM's memory and CPU shows the limitations of the system when it has reduced capabilities, making it easier to demonstrate the effects of a DDoS attack on the network.
What is the presenter's advice for developers regarding network security?
-The presenter advises developers to implement DDoS mitigation capabilities when creating networks that could be exposed to such attacks.
How does the presenter show the effects of a DDoS attack on the eNodeB?
-The presenter shows the effects by simulating a large number of UE connections, causing the eNodeB to fail due to high CPU usage and memory consumption.
Outlines

此内容仅限付费用户访问。 请升级后访问。
立即升级Mindmap

此内容仅限付费用户访问。 请升级后访问。
立即升级Keywords

此内容仅限付费用户访问。 请升级后访问。
立即升级Highlights

此内容仅限付费用户访问。 请升级后访问。
立即升级Transcripts

此内容仅限付费用户访问。 请升级后访问。
立即升级浏览更多相关视频

DDoS Attack Explained | How to Perform DOS Attack | Ethical Hacking and Penetration Testing

5G Security Architecture in 28 minutes

Tutup DDOS attack dan port scaning dengan mikrotik firewall

When BSNL 5G is Coming?

hping3 Tutorial - TCP SYN Flood Attacks - DoS and DDoS Attacks using Kali Linux 2022 and Windows XP
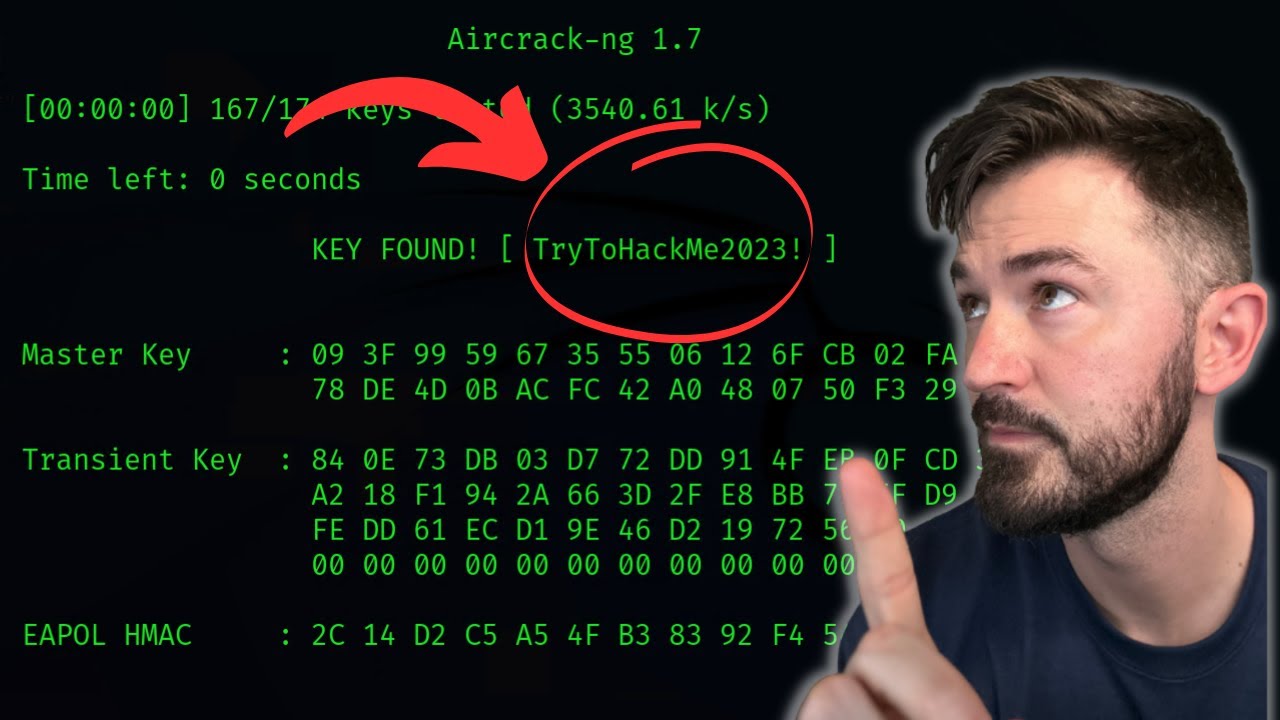
How To Crack WPA2 WiFi Password With AirCrack-NG - WiFi Pentesting Video 2024
5.0 / 5 (0 votes)
