Validating System Executions with the TLA+ Tools Markus A Kuppe, Microsoft
Summary
TLDRThe speaker from Inria and Microsoft discusses the use of TLA+ and its tool, TLC, for validating system executions, specifically in distributed systems. The talk revolves around the concept of Trace Validation, a technique that involves logging local events from each node of a distributed system, then combining these logs into a global log to maintain causal order. By comparing the behaviors derived from these logs to a high-level specification, developers can identify discrepancies between the system's intended and actual behaviors. The speaker shares experiences of applying Trace Validation to various systems, including etcd and CCF, where it has uncovered several bugs and improved system specifications. The process not only helps in validating existing systems but also guides the development of new features based on the refined specifications. The talk emphasizes the importance of TLA+ expertise and the effectiveness of Trace Validation in narrowing the gap between specifications and code, ultimately enhancing system reliability.
Takeaways
- 📚 The speaker discusses the use of TLA+ and Trace Validation for validating system executions, emphasizing its effectiveness in narrowing the spec-to-code gap.
- 🔍 Trace Validation is a technique that involves collecting log files from a distributed system and comparing them against a high-level specification to ensure correctness.
- 🌐 The process begins with logging local events, which are then combined into a global log to maintain causal order, essential for validating system behaviors.
- 📈 The speaker shares experiences with seven different systems, highlighting how Trace Validation has uncovered discrepancies and bugs in real-world applications.
- ⚙️ The implementation of logging was straightforward in the discussed systems, requiring minimal changes to the existing codebase.
- 🕒 The validation process is efficient, with the model checker exploring all possible combinations of actions due to the concurrent nature of TLA+.
- 🔧 The speaker suggests that TLA+ expertise is necessary for effective use, but the回报 (return on investment) is high, given the bugs and issues identified.
- 🔗 The use of logical distributed clocks, like vector clocks or Lamport clocks, is recommended for ordering log files, which can also aid in visualization and understanding of system interactions.
- 📉 The speaker addresses challenges in applying Trace Validation, such as the need to refine high-level specifications to align with implementation details.
- 🛠️ Trace Validation serves as a complementary tool to other verification methods like fuzzing and chaos engineering, potentially guiding these processes by providing a notion of coverage.
- ⏪ The technique is not limited to new systems; it's also highly effective for verifying existing or 'brownfield' systems with pre-existing implementations.
- 🔬 The future work includes generalizing Trace Validation for broader application, integrating it with model-based testing, and automating the translation of counterexamples into system tests.
Q & A
What is the main focus of the talk?
-The talk focuses on validating system executions with TLA+ (Temporal Logic of Actions) and how it can be used to close the spec-to-code gap in distributed systems.
What is the significance of maintaining a log file in each node of a distributed system?
-Log files in each node help in recording local events. They are crucial for debugging incidents in production and for creating a global log to maintain causal order during testing.
How does Trace validation work in TLA+?
-Trace validation in TLA+ involves creating a trace specification that reads the log file and generates a set of behaviors conforming to what is observed in the log file. The validation part then compares this set of behaviors to the set of behaviors defined by a high-level specification to check for intersections, indicating acceptance of the execution by the specification.
What is the role of the high-level specification in the validation process?
-The high-level specification serves as a reference model that is compared against the behaviors derived from the log file. It helps in identifying whether the actual system execution conforms to the intended behavior as defined by the specification.
How does the speaker describe the experience with applying Trace validation to seven different systems?
-The speaker describes the experience as effective, with Trace validation finding spec-to-code divergences in all seven systems and uncovering non-trivial bugs in real-world systems.
What is the importance of logging in the context of Trace validation?
-Logging is essential for Trace validation as it provides the necessary data to create the global log file. The speaker suggests logging when messages are sent and received, and any observable node local state changes to ensure accurate validation.
What are the benefits of using a distributed clock for ordering log files?
-A distributed clock, such as a vector clock or a Lamport clock, helps in causally ordering the log files from different nodes, which is necessary for maintaining the correct sequence of events during Trace validation.
What is the role of the TLA+ tools in narrowing the spec-to-code gap?
-TLA+ tools, particularly Trace validation, are shown to be mature enough to help bridge the gap between high-level specifications and actual code implementations by providing a method to validate system executions against their specifications.
How does the speaker suggest improving the Trace validation process?
-The speaker suggests refining the high-level specifications to bring them closer to the implementation, using model-based testing to generate diverse sets of behaviors, and possibly automating the translation of counterexamples into system tests.
What are the challenges faced when applying Trace validation to existing systems?
-The challenges include the need for TLA+ expertise, the effort to map the specific system to the model, and the time spent on updating the TLA+ tools for better integration with existing systems.
How does the speaker view the future of Trace validation?
-The speaker is optimistic about the future of Trace validation, believing it to be a valuable tool for narrowing the spec-to-code gap and improving the reliability of distributed systems.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes

TLA+ Conf 24 - Daniel Stachnik - Tackling State Space Explosion In TLA+ Visualizations

Distributed Computing KTU 2019 Scheme | Termination Detection in distributed Systems |

Google SWE teaches systems design | EP26: Redis and Memcached Explained (While Drunk?)
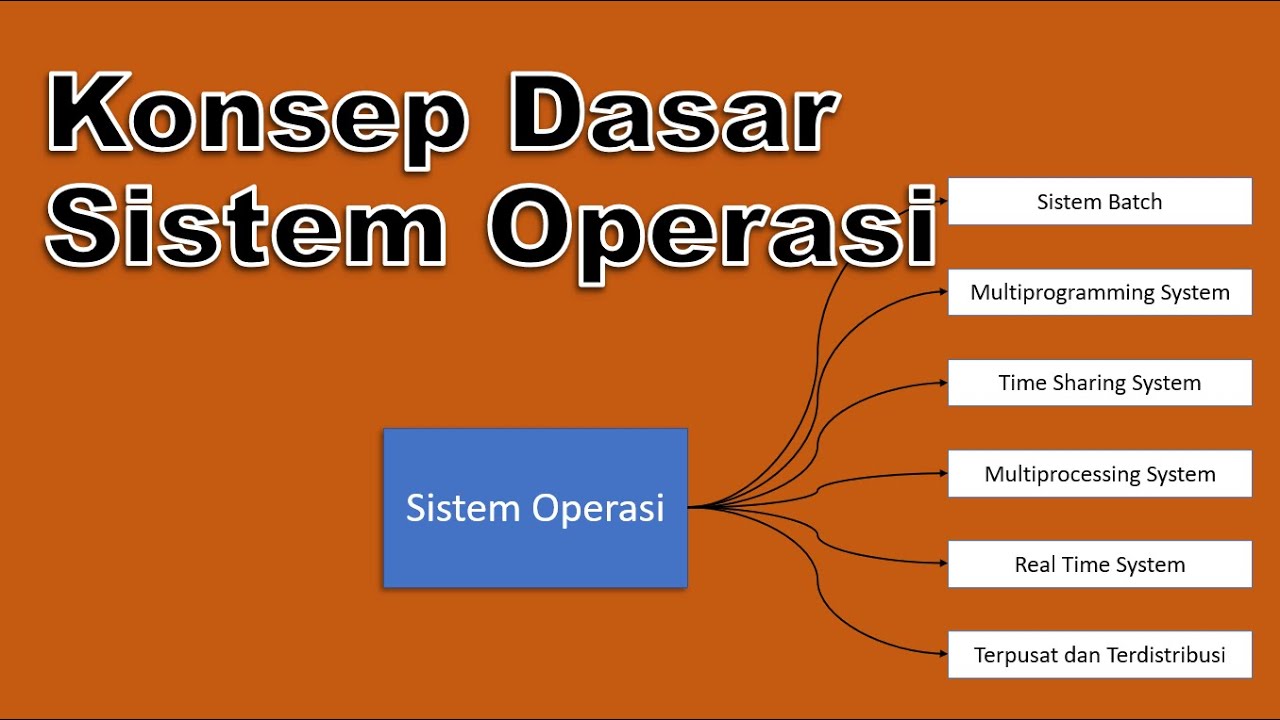
Konsep Dasar Sistem Operasi

Blockchain: The Foundation of the Future

How Distributed Lock works | ft Redis | System Design
5.0 / 5 (0 votes)
