Role Based Access | Endpoint Privilege Manager Nugget Series
Summary
TLDRThis nugget explains the importance of role-based access in building and maintaining EPM policies. It contrasts individual policies, where each user gets unique permissions, with role-based access, which assigns permissions to roles. Role-based access is favored for its scalability, reducing administrative effort, and preventing privilege creep. The video discusses methods to identify roles, such as using group memberships or conditions, and emphasizes combining these methods to tailor policies effectively while managing risks and handling exceptions.
Takeaways
- 🔑 Role-based access is crucial for building and maintaining EPM policies.
- ⚖️ Two methodologies for building EPM policies: individual policies and role-based access.
- 👤 Individual policies assign unique sets of policies to each user.
- 🧑🤝🧑 Role-based access assigns policies to identified roles, allowing all users in that role to execute associated tasks.
- 📈 Role-based access is preferred for scalability and reduces administrative effort.
- 🗂️ Managing access on a file-by-file basis is unmanageable; role-based access simplifies this process.
- 🚪 Role-based access supports the joiners, movers, and leavers process, preventing privilege creep.
- 🔄 If no pre-existing roles exist, start with a binary option (admin rights vs. no admin rights) and tailor roles from there.
- 👥 Use pre-existing group memberships to identify and target roles.
- 🔧 If a specific role cannot be established from a single group, combine groups or use conditions to match policies.
- 🖥️ Conditions can target users based on network resources, connection type, or other characteristics.
- 🏡 Policies can be combined for different scenarios, such as remote work, while maintaining risk reduction.
Q & A
What are the two competing methodologies used to build EPM policies?
-The two competing methodologies are individual policies and role-based access.
What is the main difference between individual policies and role-based access?
-Individual policies assign a unique set of policies to each user, while role-based access assigns policies to identified roles that all users in that role can execute.
Why might individual policies seem like a better choice initially?
-Individual policies might seem better initially because they more closely follow the principle of least privilege.
What makes role-based access a better choice for building and maintaining EPM policies?
-Role-based access is better for scalability, reduces administrative effort, minimizes the number of policies, and supports the joiners, movers, and leavers process to avoid privilege creep.
What is an example given in the script to illustrate the unmanageability of individual policies?
-Managing access to a file server on a file-by-file basis for each individual would quickly become unmanageable.
How does role-based access help manage administrative effort?
-Role-based access reduces administrative effort by assigning access to roles rather than individuals, which simplifies management.
What is the first step suggested if there are no pre-existing roles in an organization?
-Start with a binary option, such as users with admin rights and those without, and tailor the rights required for each role.
How can roles be identified if they cannot be established based on a single group?
-Roles can be identified by using a collection to combine groups, such as dynamically creating the role of DevOps if the user is a member of both developers and operations groups.
What conditions can be used to target roles if group membership is not sufficient?
-Conditions such as the availability of network resources or connection type can be used, allowing policies to be matched based on any characteristic that resolves to true or false.
How can multiple conditions be managed in policies according to the script?
-Multiple conditions can be combined in groups within a single policy or across different policies, allowing for flexible discovery and exception handling.
Outlines

此内容仅限付费用户访问。 请升级后访问。
立即升级Mindmap

此内容仅限付费用户访问。 请升级后访问。
立即升级Keywords

此内容仅限付费用户访问。 请升级后访问。
立即升级Highlights

此内容仅限付费用户访问。 请升级后访问。
立即升级Transcripts

此内容仅限付费用户访问。 请升级后访问。
立即升级浏览更多相关视频

QuickStart Phase 1 | Endpoint Privilege Manager Nugget Series
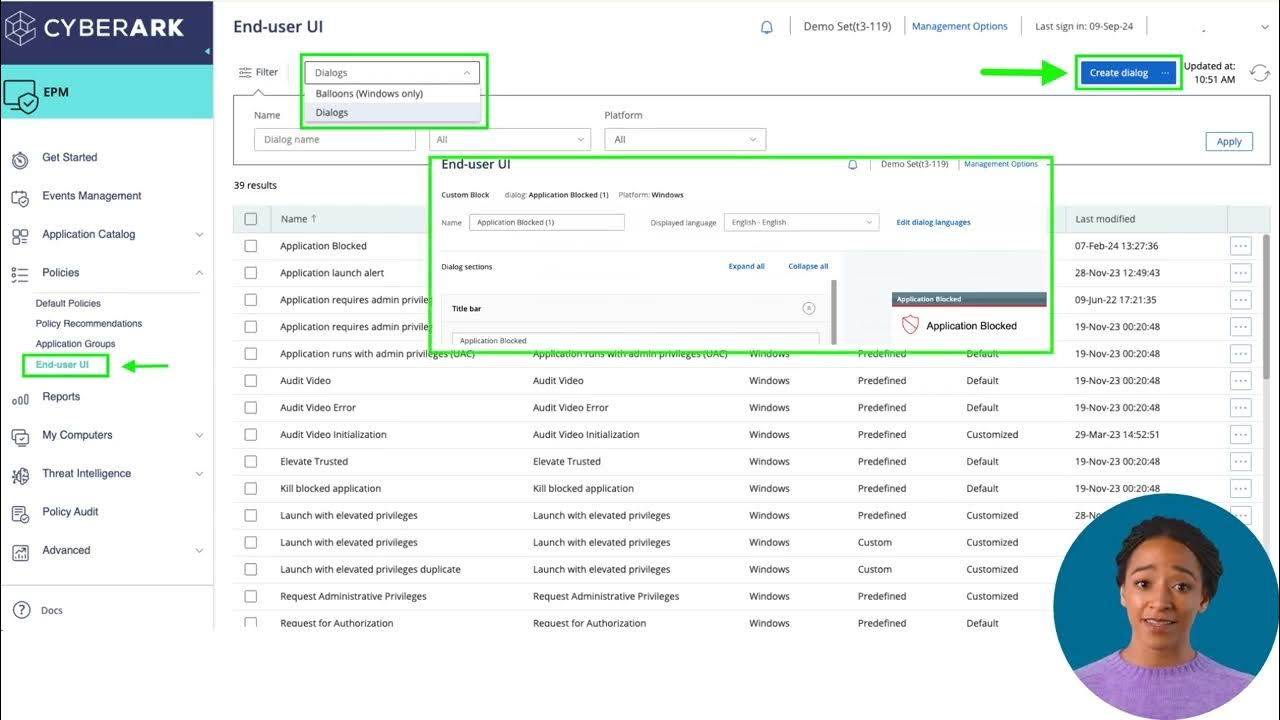
EPM Console Overview | CyberArk University

Security Policies - CompTIA Security+ SY0-701 - 5.1

Access Controls - CompTIA Security+ SY0-701 - 4.6

Komitmen untuk menjaga keutuhan wilayah NKRI//bab 5//kelas 9//kurmer//buku terbaru//semester 2

CLF C02 - Module 07 : AWS Identity and Access Management
5.0 / 5 (0 votes)
