Cybersecurity Project | Wireshark Packet Analysis
Summary
TLDRIn this educational lab video, the presenter guides viewers through the process of capturing usernames and passwords using Wi-Fi tools like Wireshark and Putty. They demonstrate setting up a virtual environment with VMware or VirtualBox, installing Windows 10 and Ubuntu, and configuring network settings for internal communication. The video serves as a practical tutorial for beginners in cybersecurity, illustrating the importance of secure communication protocols like SSH over Telnet, which transmits data in plain text.
Takeaways
- 💻 The lab demonstrates how to capture username and password using Wireshark.
- 🛠️ Essential tools for the lab include VMware, VirtualBox, or Oracle VM, along with Wireshark and PuTTY.
- 📡 The setup involves creating a virtual environment with Windows 10 and Ubuntu to simulate network traffic.
- 🔒 The tutorial walks through the process of installing and configuring Windows 10 and Ubuntu for network communication.
- 🌐 Network configuration is crucial, with a focus on setting up internal network adapters for VM-to-VM communication.
- 🔄 The lab shows how to assign static IP addresses to VMs for controlled network traffic.
- 🔍 Wireshark is used to capture TCP packets, which can reveal sensitive information like usernames and passwords if not encrypted.
- 🔒 The video highlights the insecurity of Telnet, which transmits data in plain text, making it susceptible to packet sniffing.
- 🔑 The demonstration captures and analyzes Telnet traffic to show how easily credentials can be intercepted.
- 💼 The lab can be documented and added to a portfolio or GitHub as a practical project in cybersecurity.
Q & A
What is the main objective of the lab demonstrated in the video?
-The main objective of the lab is to demonstrate how to capture username and password using Wireshark and putty, and to set up a network between a Windows 10 and an Ubuntu VM for this purpose.
Which hypervisor tools are mentioned in the script for setting up the lab?
-The script mentions VMware Workstation, VM Player, and Oracle VirtualBox as the hypervisor tools needed for setting up the lab.
What operating systems are installed in the lab for the demonstration?
-The operating systems installed for the lab demonstration are Windows 10 Enterprise and Ubuntu 22.04.
How can the lab setup be beneficial for an individual's portfolio or resume?
-The lab setup can be documented and added to an individual's portfolio or GitHub, showcasing their practical experience in cybersecurity, specifically in network security and penetration testing.
What is the source for downloading Windows 10 Enterprise mentioned in the script?
-The source for downloading Windows 10 Enterprise is the Microsoft Evaluation Center, which can be found by searching for 'Microsoft Evaluation Center' on Google.
What network configuration is set up between the Windows 10 and Ubuntu VMs for the lab?
-An internal network adapter is configured to allow communication between the Windows 10 and Ubuntu VMs, using IP addresses in the 192.168.50.x range.
Why is it necessary to install VMware Tools or VirtualBox Guest Additions in the video?
-Installing VMware Tools or VirtualBox Guest Additions is necessary to improve the performance and usability of the VMs, including better mouse integration and screen resizing.
What is the purpose of using Wireshark in the lab?
-Wireshark is used in the lab to capture network packets, specifically to demonstrate how usernames and passwords can be intercepted during a Telnet session.
Why is putty used in conjunction with Wireshark in the demonstration?
-PuTTY is used to establish a Telnet connection to the Ubuntu VM, which then generates network traffic that can be captured and analyzed by Wireshark to show the transmission of plain text credentials.
What security risk is highlighted by the use of Telnet in the lab?
-The lab highlights the security risk of using Telnet, which transmits data, including usernames and passwords, in plain text, making it susceptible to interception and unauthorized access.
How can one connect with the presenter for questions or further discussion after the video?
-One can connect with the presenter by joining the Discord server mentioned in the video or by leaving comments in the comment section for questions or further discussion.
Outlines

此内容仅限付费用户访问。 请升级后访问。
立即升级Mindmap

此内容仅限付费用户访问。 请升级后访问。
立即升级Keywords

此内容仅限付费用户访问。 请升级后访问。
立即升级Highlights

此内容仅限付费用户访问。 请升级后访问。
立即升级Transcripts

此内容仅限付费用户访问。 请升级后访问。
立即升级浏览更多相关视频

WiFi Password Cracking in 6 Minutes and 4 Seconds
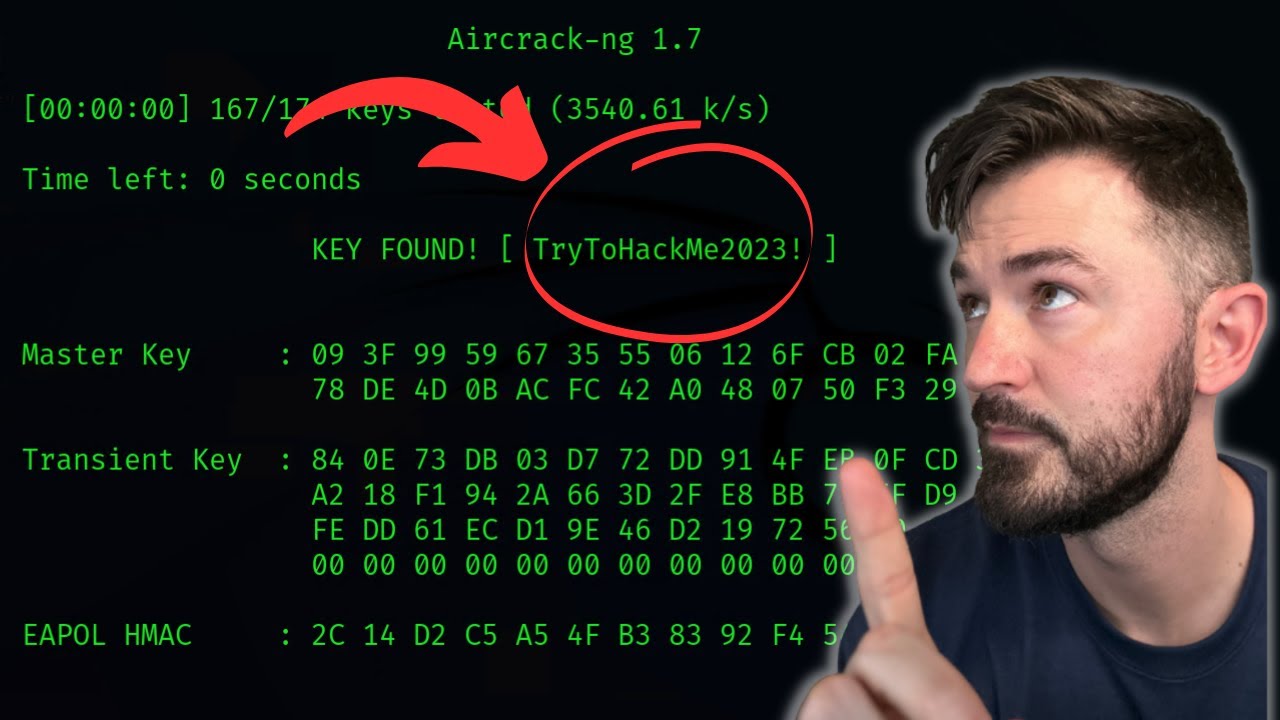
How To Crack WPA2 WiFi Password With AirCrack-NG - WiFi Pentesting Video 2024

Cara Melihat Password Wifi Yang Sudah Terhubung Ke Laptop/PC

3 Levels of WiFi Hacking

How to hack Wi-Fi networks ( Educational )
Cara Menampilkan dan Melihat Kode QR WiFi di HP Android
5.0 / 5 (0 votes)
