Session Vs JWT: The Differences You May Not Know!
Summary
TLDRThis video explores two prevalent web authentication methods: session-based and JWT (Json Web Tokens). It outlines the process flow for each, highlighting their pros and cons. Session-based authentication is server-centric, storing data and issuing session IDs, which are easy to revoke but may add latency in distributed systems. JWTs, on the other hand, embed user data within tokens, offering a stateless solution suitable for microservices and third-party services, with refresh tokens enhancing security. The choice between them hinges on specific application needs and architecture.
Takeaways
- 🔒 **Session-Based Authentication**: The server creates and stores session data, using a unique session ID to authenticate requests.
- 🍪 **Session ID in Cookies**: A session ID is sent back to the client, usually in the form of a cookie, which is then sent with subsequent requests.
- 🗃️ **Centralized Session Store**: In distributed systems, a centralized session store like Redis or a distributed SQL database is used for session data access by multiple servers.
- 🚫 **Session Revocation**: Sessions can be easily revoked by the server, which is advantageous for security in case of account compromise.
- 🔄 **Complexity in Distributed Systems**: Using a centralized session store adds complexity and latency due to the need for server requests to the session store.
- 🔐 **JWT Authentication**: JSON Web Tokens (JWTs) are generated and signed by the server with a secret key to ensure token integrity.
- 🔑 **Token Storage**: Clients store JWTs, typically in local storage or cookies, and send them in request headers for authentication.
- 📈 **Stateless Nature of JWTs**: Unlike sessions, JWTs do not require the server to store any session state, as all necessary data is contained within the token.
- 🛡️ **Signing Algorithms**: JWTs can be signed using HMAC, RSA, or ECDSA, with the choice depending on security requirements and system architecture.
- ⏱️ **Token Expiration Handling**: JWTs can be vulnerable to misuse if stolen, but this can be mitigated using short-lived access tokens and refresh tokens.
- 🔄 **Refresh Tokens**: Refresh tokens allow for the issuance of new access tokens without requiring user re-authentication, balancing security and user experience.
- 🏢 **Use Case for Sessions**: Session-based authentication is suitable for applications needing instant session revocation or already using a centralized data store.
- 🌐 **Use Case for JWTs**: JWTs are ideal for stateless architectures, microservices, and scenarios where authentication data needs to be shared with other services.
Q & A
What are the two most common approaches to web authentication discussed in the script?
-The two most common approaches to web authentication discussed in the script are session-based authentication and JSON Web Tokens (JWTs).
How does session-based authentication work?
-In session-based authentication, the server verifies the user's login credentials, creates a new session if they're valid, stores session data, and sends back a unique session ID to the client, usually in a cookie. The client sends this session ID with each subsequent request, and the server uses it to look up session data for authentication.
What is the advantage of revoking a session in session-based authentication?
-Revoking a session in session-based authentication is straightforward because the session data is stored on the server. The server can simply delete or invalidate the session at any time.
What challenges arise when using a centralized session store in a distributed system?
-In a distributed system, all servers need access to the same session data, which typically requires a centralized session store like Redis or a distributed SQL database. This adds complexity and potential latency to each request as the server needs to make a separate trip to the session store.
How does JWT-based authentication differ from session-based authentication?
-JWT-based authentication involves the server generating a token with a secret key after verifying the user's credentials. The client stores this token and sends it in the request headers for subsequent requests. The server verifies the token's signature and uses the data in the token for authentication, without storing any session state.
What are the common signing algorithms used for JWTs?
-The common signing algorithms used for JWTs include HMAC, RSA, and ECDSA. HMAC is a symmetric signing method, while RSA and ECDSA are asymmetric methods offering more security by keeping the private key secret.
Why might HMAC be a concern from a security perspective?
-HMAC might be a security concern because it requires sharing the secret key with any service that needs to verify the token. This can be a risk if the key is exposed or if the services are not trusted.
What is the purpose of refresh tokens in JWT-based authentication?
-Refresh tokens are used in combination with short-lived access tokens to handle token expiration. When the access token expires, the client can send a refresh token to obtain a new access token without requiring the user to log in again, balancing security and user experience.
How does using JWTs benefit a microservices architecture?
-JWTs are beneficial in a microservices architecture because they store all necessary data within the token itself, allowing services to verify and trust the token without needing to contact the authentication service on each request.
When should you choose session-based authentication over JWTs?
-Session-based authentication is a better choice when you need the ability to revoke sessions instantly, if a user reports an account compromise, or when you already have a centralized data store for other purposes and can leverage it for session storage.
What considerations should be made when deciding between session-based and JWT-based authentication?
-The decision between session-based and JWT-based authentication should consider the specific needs and architecture of your application, including the need for instant session revocation, the presence of a centralized data store, the requirement for a stateless architecture, and the need to share authentication data with other services.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

Session vs Token Authentication in 100 Seconds

#35 What is JWT and Why

What Is JWT and Why Should You Use JWT
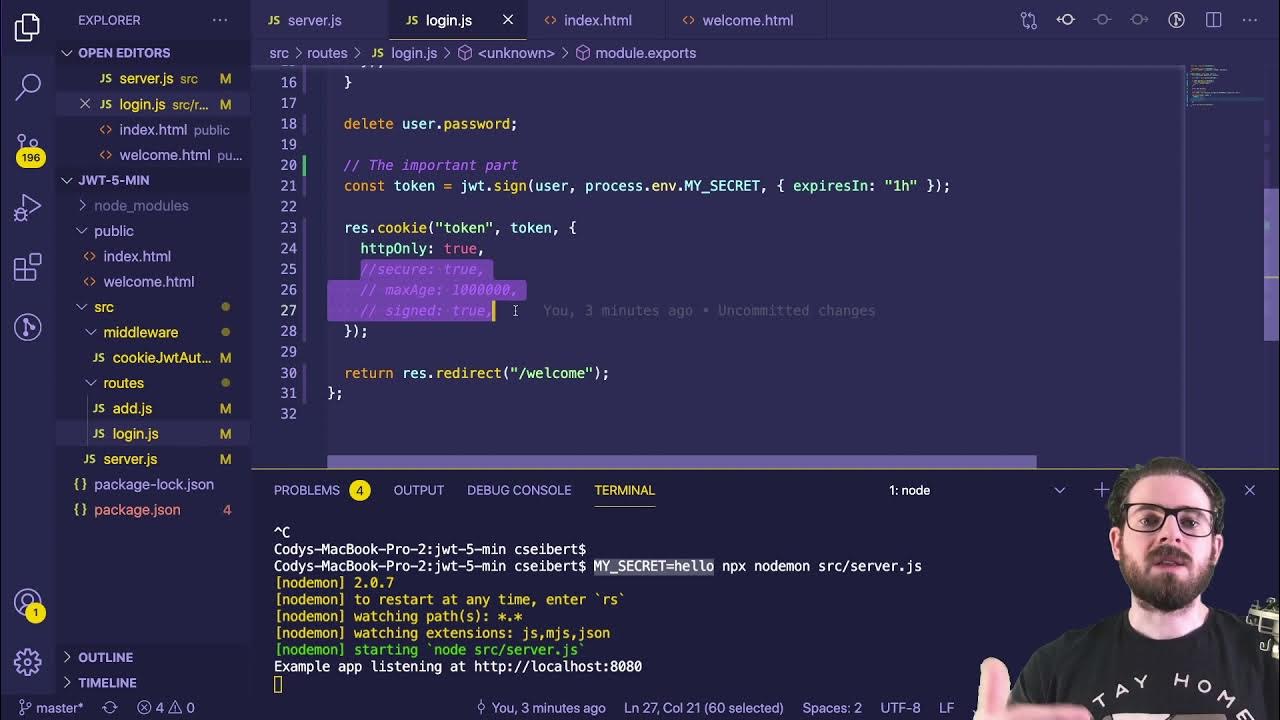
Learn JWT in 10 Minutes with Express, Node, and Cookie Parser

#37 Spring Security | Generating JWT Token
JWT Authentication with Node.js, React, MySQL | Node JS Authentication With JSON Web Token
5.0 / 5 (0 votes)