The CIA Triad
Summary
TLDRIn this cybersecurity tutorial, instructor Rosie introduces the CIA triad: Confidentiality, Integrity, and Availability, as the foundational principles of information security. The video emphasizes the importance of protecting an organization's valuable information assets from unauthorized access, ensuring data reliability, and maintaining system accessibility to authorized users. It also encourages viewers to join the online community for further learning and to subscribe to the YouTube channel for more educational content.
Takeaways
- 👋 Introduction: Rosie is a cybersecurity instructor and welcomes students to MCSI.
- 🏢 Organizational Assets: Organizations have valuable information assets such as intellectual property and customer data.
- 🛡️ Risks: These assets are at risk of attacks by malicious entities, necessitating security measures.
- 🔒 Information Security Goal: The primary goal is to protect assets from various internal and external threats.
- 🔑 CIA Triad: The core principles of information security are Confidentiality, Integrity, and Availability.
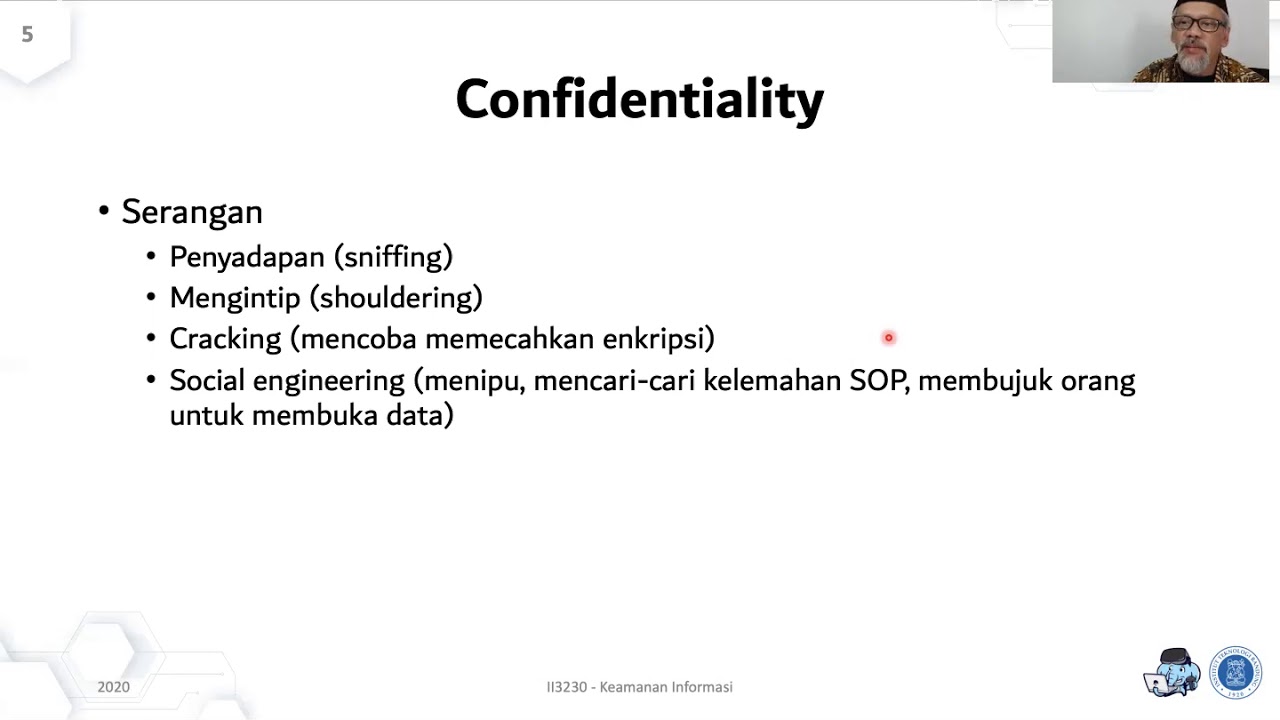
- 🔒 Confidentiality: It restricts access to information assets to authorized individuals to maintain privacy.
- 📝 Integrity: Ensures the reliability, accuracy, and completeness of data, preventing unauthorized modifications.
- 🚀 Availability: Guarantees timely access to data and resources for authorized users when needed.
- 👍 Engagement: Encourages viewers to like, share, and subscribe to the YouTube channel for more content.
- 🌐 Community: Invites students to join an online community to learn useful cybersecurity skills.
- 📚 Registration: Offers a free account registration on the website for interested students.
Q & A
What is the main focus of the video presented by Rosie?
-The main focus of the video is to introduce the CIA triad of information security and its importance in protecting an organization's information assets from various threats.
What does CIA stand for in the context of information security?
-In the context of information security, CIA stands for Confidentiality, Integrity, and Availability.
Why is it important for organizations to manage and secure their information assets?
-It is important for organizations to manage and secure their information assets to protect them from being attacked by malicious entities, ensuring they can effectively help the organization fulfill its business objectives.
What is the definition of Confidentiality in information security?
-Confidentiality in information security refers to restricting access to information assets to only those individuals who are allowed to access them, protecting the assets from unauthorized disclosure and maintaining their privacy.
How is Integrity defined in the context of information security?
-Integrity in information security is the assurance that the information or data stored on the system is reliable, accurate, and complete, ensuring that information assets cannot be modified by unauthorized individuals.
What does Availability in information security entail?
-Availability in information security means ensuring reliable and timely access to data and resources on a system to authorized individuals, ensuring that information systems and resources are accessible whenever needed.
What are some of the threats that information security aims to protect against?
-Information security aims to protect against threats such as data theft, disclosure of trade secrets, malware attacks, and other unauthorized access or modifications to information assets.
Why should viewers subscribe to the YouTube channel mentioned in the video?
-Viewers should subscribe to the YouTube channel to receive more videos with useful information on cyber security, enhancing their understanding and skills in the field.
What is the purpose of joining the online community of students mentioned in the video?
-Joining the online community of students allows individuals to learn useful cyber security skills, interact with peers, and share knowledge in a collaborative environment.
How can one register for a free account to access the online community and resources?
-To register for a free account, one can visit the website mentioned in the video and follow the registration process.
What is the final message Rosie conveys to the viewers of the video?
-Rosie's final message is to encourage happy learning and expresses her anticipation to see the viewers again, emphasizing the importance of continuous learning in cyber security.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

CIA Triad: Confidentiality, Integrity & Availability | Cybersecurity

Fundamentals of Information Security

Cybersecurity Architecture: Fundamentals of Confidentiality, Integrity, and Availability
Keamanan Informasi: Prinsip keamanan - confidentiality (section 3)

What is the Principle Of Least Privilege (POLP)?

SMT 2-4 Plaintext Communication Vulnerability
5.0 / 5 (0 votes)