Self-Hosting Security Guide for your HomeLab
Summary
TLDRThis video script delves into best practices for securely self-hosting services at home. It emphasizes the importance of foundational security, starting from hardware and firmware updates to network segmentation and firewall configurations. The guide explores using VPNs for secure access, leveraging cloud services like Cloudflare for protection, and setting up reverse proxies and authentication for enhanced security. The script also touches on the use of intrusion detection systems and the principle of least privilege, offering a comprehensive approach to home lab security.
Takeaways
- 🛡️ The importance of securing the foundation of your home lab, not just the last mile, is emphasized for self-hosting services.
- 🏗️ A well-architected home lab should consider various components including hardware, network configuration, and security measures.
- 🛍️ Microcenter is recommended for great deals on hardware and technology needs for building and maintaining a home lab.
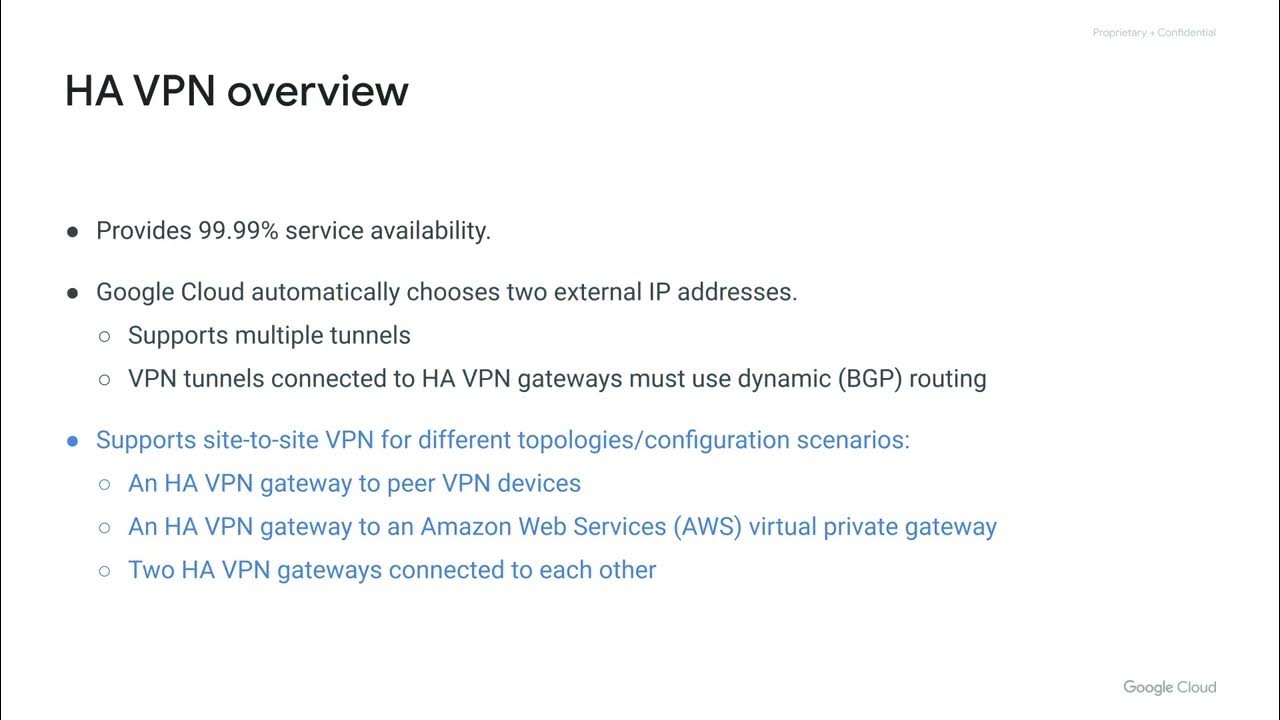
- 🔒 Self-hosting VPNs are suggested as a secure method to expose services without public exposure, limiting access to only those with VPN credentials.
- 🌐 Public cloud hosting is an alternative to self-hosting that mitigates some risks by isolating compromised machines from the local network.
- 🔩 The necessity of keeping server hardware and firmware up-to-date to maintain security in a home lab environment is highlighted.
- 🖥️ Choosing a secure and supported operating system for your applications and avoiding running services as root or admin is recommended.
- 🔁 The benefits of using minimal container images to reduce attack surfaces and the importance of containerization engine updates are discussed.
- 🌐 Network segmentation is crucial for security, allowing control over network traffic and mitigating risks from compromised devices.
- 🚧 External networking should only forward necessary ports and utilize a reverse proxy for added security and performance benefits.
- 🛡️ Utilizing services like Cloudflare can provide external protection, including DDoS attack mitigation, TLS encryption, and performance enhancements.
Q & A
What is meant by the 'last mile' in the context of self-hosting services?
-The 'last mile' refers to the final hop or connection point before a user accesses the self-hosted services. It often involves using certificates or a reverse proxy for security.
Why is it important to consider the foundation of a home lab for self-hosting services?
-Security and architecture of a home lab are crucial because they form the basis for the entire setup. A strong foundation ensures that the system is secure from the ground up, not just at the last mile.
What are some of the best practices in architecture for self-hosting services within a home lab?
-Best practices include individual systems and hardware configuration, application hosting considerations, network configuration and segmentation, reverse proxies, certificates, two-factor authentication, firewall configuration, and internet security settings.
Why should one consider using a VPN for self-hosting services?
-A VPN creates a secure tunnel from outside to inside the network, allowing for controlled access and mitigating the risks associated with exposing services directly to the internet.
What is the significance of keeping hardware patched with the latest firmware in a self-hosted environment?
-Keeping hardware patched ensures that the server and all connected devices are up to date with the latest security fixes, reducing the risk of vulnerabilities being exploited.
What are the considerations for choosing a secure operating system for self-hosting?
-One should choose an operating system that is still supported, regularly patched, and follows the principle of least privilege, ensuring minimal access levels for users and avoiding running services as root or admin.
Why is network segmentation important for self-hosting applications?
-Network segmentation divides the network into multiple segments or subnets, controlling the flow of traffic and improving both performance and security by isolating trusted devices from those exposed to the internet.
What role does a reverse proxy play in self-hosting services?
-A reverse proxy directs traffic from clients to servers, simplifies certificate management, and can integrate with other systems using middleware, enhancing both security and maintenance efficiency.
How can using an auth proxy like Authelia enhance security for self-hosted services?
-Authelia provides an additional layer of authentication and authorization for services, even if they don't have their own authentication mechanisms, including support for two-factor authentication.
What is the purpose of using an intrusion detection system (IDS) and intrusion prevention system (IPS) in self-hosting?
-IDS and IPS analyze traffic for signatures of known attacks and either alert the user (in the case of IDS) or block the traffic (in the case of IPS), providing an extra layer of security against threats.
Why is it recommended to use a public reverse proxy like Cloudflare along with a private one?
-Using Cloudflare improves performance, provides some protection against attacks, caching, TLS encryption, and can block malicious traffic before it reaches the private reverse proxy or server.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

Apa itu hosting? Pengertian dan Jenis Layanan Hosting

AWS Cloud Practitioner Exam Questions | CLF - C02 | Tutorial - 08 | Tech India |
Connecting Networks
Advanced Networking - #1 Overview [EN]

Afinal o que é AWS Secrets Manager? Confira na prática!

Shared Hosting vs VPS vs Cloud Hosting - What's The Difference?
5.0 / 5 (0 votes)