Pseudorandom Number Generator (PRNG)
Summary
TLDRThis presentation delves into the concept of pseudo random number generators (PRNGs), emphasizing their importance in generating sequences that appear random but are deterministic. It explains that true randomness can only be found in the physical world, whereas PRNGs produce predictable, repeatable sequences. The session covers how PRNGs are used in stream ciphers for secure communication, with Alice and Bob exemplifying the process of encryption and decryption using a shared key or seed. The lecture also touches on the theoretical aspects of stream ciphers and the Shannon notion of perfect secrecy, highlighting the practical challenges of achieving true randomness and the role of pseudo randomness in enhancing security.
Takeaways
- 🔑 The presentation discusses the concept of Pseudo Random Number Generators (PRNGs) and their importance in generating random sequences.
- 📚 By the end of the session, learners will understand the necessity of pseudo random sequences and how they are generated using PRNGs.
- 🌱 A keystream generator is introduced as a device that takes a seed or key to produce a sequence of bits, which are expected to be random in nature.
- 🎲 The script clarifies that true randomness can only be achieved through physical phenomena, such as natural fluctuations or noise, which are unpredictable and non-deterministic.
- 💻 In contrast, PRNGs generate numbers that are deterministic and predictable, hence they produce pseudo-randomness rather than true randomness.
- 🔄 Pseudo-randomness is characterized by repeating patterns after a certain period, which distinguishes it from true randomness.
- 🔑 The size of the key or seed used in the keystream generator affects the length and quality of the pseudo-random sequence generated.
- 🔐 The script uses the example of a stream cipher to illustrate how Alice and Bob can use a PRNG to securely exchange messages, with the key being the output from the keystream generator.
- 🔒 For secure communication, both sender and receiver must use the same seed or key to ensure they generate the same pseudo-random sequence.
- 🎯 The script emphasizes the theoretical aspects of stream ciphers and the conditions under which a sequence can be considered truly random, highlighting the impracticality of generating truly random sequences with machines.
- 📈 The concept of perfect secrecy, as per Shannon's notion, is tied to the use of one-time pads, which rely on truly random sequences for maximum security.
Q & A
What is the main focus of the presentation?
-The presentation focuses on the concept of the Pseudo Random Number Generator (PRNG), explaining its necessity and how it generates pseudo random numbers.
What are the two main outcomes the learner is expected to achieve after the session?
-The learner will understand the need for having a pseudo random sequence and will know how pseudo random numbers can be generated using a PRNG.
What is a keystream generator and what role does it play in generating pseudo random numbers?
-A keystream generator is an algorithm that takes a seed or key as input and generates a sequence of bits that are expected to be random in nature, which are used as a keystream.
Why are the numbers generated by a keystream generator not truly random?
-The numbers generated by a keystream generator are not truly random because they are predictable and deterministic, unlike the non-deterministic randomness found in the physical world.
How can truly random numbers be generated?
-Truly random numbers can be generated by measuring random fluctuations or noise in the physical world, such as from a tree, forest, sky, or the universe.
What is the difference between truly random and pseudo random numbers?
-Truly random numbers are unpredictable and non-deterministic, generated by natural phenomena, while pseudo random numbers are generated by algorithms and are deterministic and repeatable.
Why is the size of the key or seed important in PRNGs?
-The size of the key or seed is important because it affects the length and quality of the pseudo random sequence generated. A larger key size results in a longer and more complex sequence.
What is a stream cipher and how does it relate to PRNGs?
-A stream cipher is a method of encryption where a pseudo random binary sequence (generated by a PRNG) is combined with plaintext to produce ciphertext, ensuring security in communication.
Can you explain the process of encryption and decryption using a stream cipher?
-In encryption, plaintext bits are XORed with pseudo random keystream bits to produce ciphertext. In decryption, the ciphertext is XORed with the same keystream to retrieve the original plaintext.
What is the significance of the one-time pad in the context of PRNGs?
-The one-time pad is a theoretical encryption technique where a truly random key is used only once. It is considered to provide perfect secrecy, but in practice, PRNGs are used to approximate this level of security.
How can the randomness of a sequence generated by a PRNG be measured?
-The randomness of a sequence can be measured by assessing its unpredictability, lack of pattern, and the equal probability of zeros and ones. This will be covered in more detail in a subsequent lecture.
What is the practical implication of using pseudo random numbers in security?
-Pseudo random numbers are used to achieve security by creating a level of unpredictability that is close to true randomness. This helps protect against certain types of attacks and ensures the confidentiality of communications.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

How to Generate Pseudorandom Numbers | Infinite Series

Pseudo Random Linier Congruential (LC) dan Blum Blum Sub Generator (BBSG) serta Stream Cipher

Linear Congruential Generator Method | Random Numbers
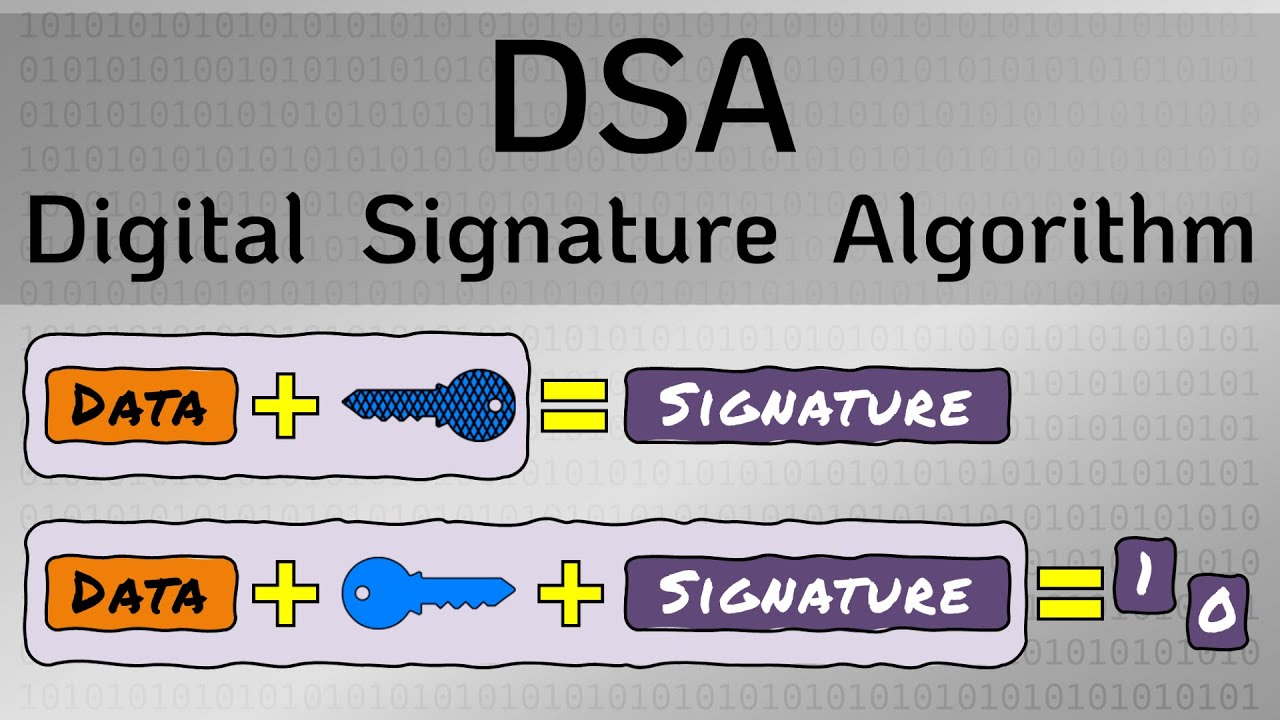
Digital Signature Algorithm (DSA) - Cryptography - Practical TLS
VARIABEL ACAK DISKRIT: Pengertian dan Distribusi Peluang-nya!

Strategi Menang J*di Onlin3 dari Jerome Polin
5.0 / 5 (0 votes)