Basic Searching in Splunk Enterprise
Summary
TLDRIn this Splunk Education video, Alex guides viewers through the basics of running searches in Splunk's Search & Reporting app. The tutorial covers navigating the app, using the search bar and time range picker, and exploring data through Table Views. The focus is on analyzing Apache server data from Buttercup Games to identify 503 errors. The video demonstrates how to refine searches with field-value pairs, wildcards, Boolean operators, and comparison operators. It also shows how to interact with events and fields to enhance searches and introduces commands for data visualization, such as stats and timechart. The video concludes with a call to action for further learning through Splunk's documentation and courses.
Takeaways
- 🔍 **Basic Searches in Splunk**: The video demonstrates how to perform basic searches in Splunk's Search & Reporting app.
- 📊 **Search Bar and Time Range Picker**: It introduces the search bar for entering queries and the time range picker to refine search results.
- 🕒 **Time Range Efficiency**: Emphasizes the importance of limiting searches by time for efficiency, highlighting 'Last 7 days' as an example.
- 🔎 **Search Assistant Features**: The script mentions the contextual matches, keyword completion, and syntax documentation provided by Splunk's search assistant.
- 📈 **Data Exploration with SPL**: It showcases using Splunk's Search Processing Language (SPL) to explore Apache server data from a fictional company.
- 🚫 **Filtering 503 Errors**: The video explains how to filter for specific HTTP status codes like 503 to identify server errors.
- 🔗 **Field-Value Pairs**: It teaches how to use field-value pairs to narrow down search results to specific events, such as HTTP status codes.
- 🌐 **Wildcards for Error Ranges**: Introduces the use of wildcards to search for a range of HTTP errors, like using '50*' to find errors in the 500 range.
- 🔄 **Boolean Operators**: The script covers the use of Boolean operators (AND, OR, NOT) to combine search terms and refine results.
- ✅ **Comparison Operators**: It explains the use of comparison operators (=, !=, <, <=, >, >=) to filter events based on specific conditions.
- 📝 **Phrase Searches**: Demonstrates searching for phrases by using quotes, ensuring that events contain the exact specified phrase.
- 🛠️ **Interactive Search Modification**: The video shows how to modify searches by interacting with event terms and fields directly within the interface.
- 📊 **Visualization Commands**: It introduces commands like 'stats' and 'timechart' for data transformation and visualization in Splunk.
- 📚 **Further Learning Resources**: The script concludes with suggestions for further learning, including Splunk documentation, videos, and educational courses.
Q & A
What is the purpose of Splunk's 'Search & Reporting' app?
-The 'Search & Reporting' app in Splunk is used to run searches on indexed data, view search results, and create reports or visualizations to explore and analyze data efficiently.
What does the Splunk search assistant provide when typing in the search bar?
-The search assistant offers contextual matches, keyword completions, and syntax documentation as you type in the search bar, helping users refine and understand their searches.
Why is limiting the time range in searches considered a best practice?
-Limiting the time range helps make searches more efficient by focusing on relevant data and reducing the amount of data Splunk needs to process, which speeds up results.
How can you narrow search results to HTTP status code 503 errors?
-You can narrow the results by specifying a field-value pair, such as `status=503`, to ensure only events with a status code of 503 are returned.
How do wildcards help in searches involving HTTP status codes?
-Wildcards, like replacing the last digit with an asterisk (e.g., `status=50*`), allow you to search for any status code that begins with '50', returning results for any server errors in the 500 range.
What happens if no Boolean operator is used between search terms?
-If no Boolean operator (like AND, OR) is used between search terms, Splunk automatically implies 'AND', meaning it searches for events containing both terms.
How can comparison operators be used in a Splunk search?
-Comparison operators such as `>`, `<`, `>=`, `!=` can be used to filter results based on conditions, such as finding events with a status greater than 400 (`status>400`).
What is the correct way to search for specific phrases in Splunk?
-To search for exact phrases, enclose the phrase in quotes. For example, to find events with the product name 'Dream Crusher', use `product_name="Dream Crusher"`.
What are the different ways you can interact with search results in Splunk?
-You can interact with search results by hovering over and clicking terms to add or remove them from your search, or by using the fields sidebar to add field-value pairs to refine the search.
How can you visualize search results in Splunk?
-You can visualize search results using commands like `stats` or `timechart`, and then select from different visualization styles such as column charts, with further formatting options available in the 'Format' and 'Trellis' menus.
Outlines

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифMindmap

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифKeywords

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифHighlights

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифTranscripts

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифПосмотреть больше похожих видео

How Can I Become a Splunk Certified Cybersecurity Defense Analyst for Free?

[3] React Native make your first program| Build your first program in React Native tutorials

Active Directory Project (Home Lab) | Troubleshooting
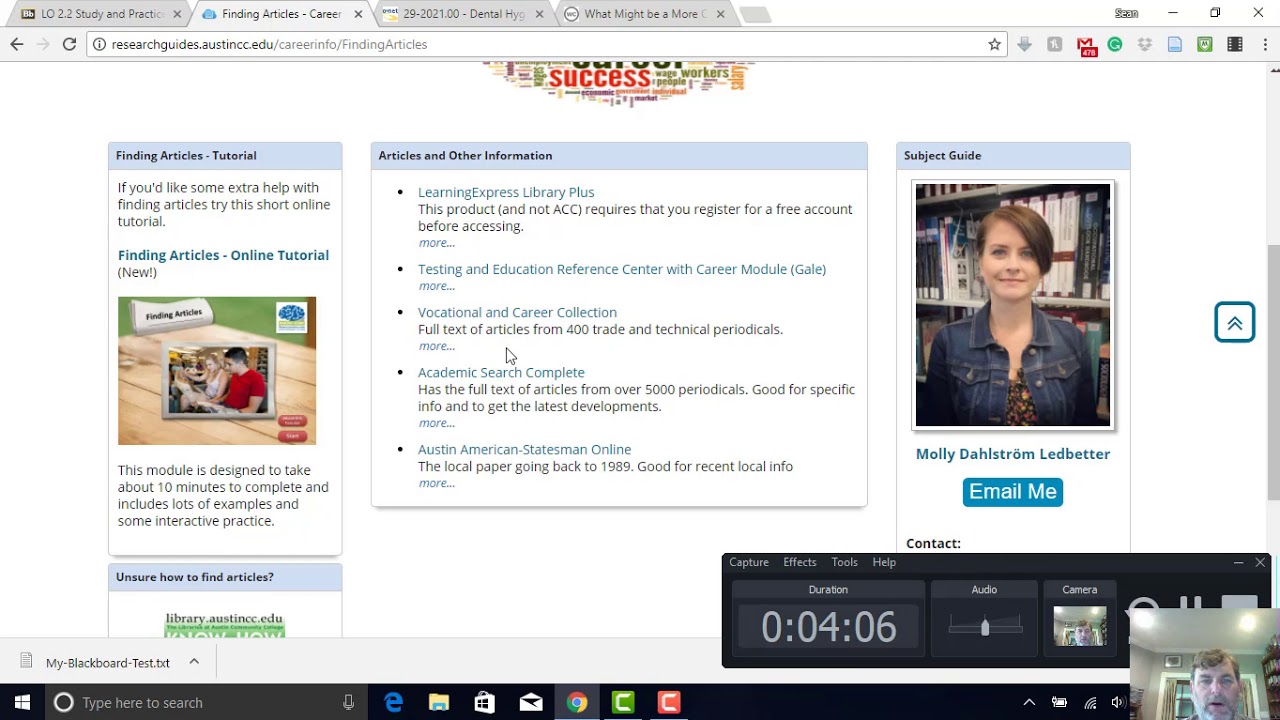
Using Research Guides at ACC

Introduction to Research: Searching for Materials in the Libraries' Catalog

Go from $0 to $15k/mo SaaS App in a weekend using AI (Steal This)
5.0 / 5 (0 votes)
