EKS Pod Identity vs IRSA | Securely Connect Kubernetes Pods to AWS Services
Summary
TLDRThis video introduces EKS Pod Identity, a feature that simplifies connecting Amazon EKS workloads to AWS services like S3 using IAM roles. The speaker explains how Kubernetes manages user authorization through service accounts and RBAC, and compares EKS Pod Identity to IAM Roles for Service Accounts (IRSA). EKS Pod Identity reduces operational overhead by removing the need for OIDC providers for each cluster, and supports attribute-based access control. The video also outlines the steps required to configure Pod Identity, emphasizing its advantages in securely accessing external services from Kubernetes workloads.
Takeaways
- 🔒 EKS Pod Identity allows secure connection between Amazon EKS clusters and AWS services like S3.
- 🆔 EKS Pod Identity simplifies the use of IAM roles with Kubernetes pods, reducing operational overhead compared to IRSA.
- 🔄 Pod Identity is backward compatible with IAM Roles for Service Accounts (IRSA).
- 🔑 Kubernetes authorizes users using RBAC with cluster roles and namespace roles.
- ⚙️ Service accounts within Kubernetes are used to authorize workloads accessing the Kubernetes API.
- 📦 Pod Identity allows Kubernetes workloads to access AWS services by associating IAM roles with pods.
- 🛠️ With EKS Pod Identity, there's no need to create OIDC providers for each cluster, unlike IRSA.
- 🔧 Pod Identity uses attribute-based access control (ABAC) for more flexible role management.
- 🧩 The Pod Identity agent, deployable as an EKS add-on, handles pod identity management with minimal operational overhead.
- 🛡️ Pod Identity ensures that Kubernetes workloads running in EKS securely access external AWS services like S3 using the right IAM roles.
Q & A
What is Amazon EKS Pod Identity?
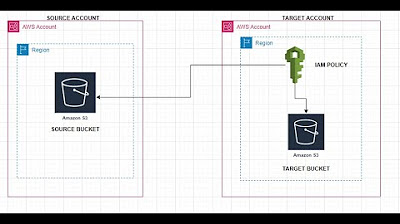
-Amazon EKS Pod Identity is a feature that allows you to connect IAM roles to pods and workloads running in Amazon EKS clusters, enabling secure access to other AWS services like S3.
How does EKS Pod Identity differ from IAM Roles for Service Accounts (IRSA)?
-EKS Pod Identity streamlines the operational overhead associated with IRSA, eliminates the need to create an OIDC provider for each cluster, and is backwards compatible with IRSA.
How is authorization typically handled in Kubernetes for users?
-Kubernetes authorizes users using RBAC (Role-Based Access Control), with permissions granted through roles. These can be cluster roles (scoped to the cluster) or roles scoped to a namespace.
What are service accounts in Kubernetes, and how do they interact with workloads?
-Service accounts in Kubernetes are used to grant permissions to workloads within the cluster. They are bound to roles (cluster roles or namespace-specific roles) via role bindings, allowing the workload to interact with the Kubernetes API.
How does EKS Pod Identity allow workloads to access services like S3?
-EKS Pod Identity allows workloads in EKS to securely access services like S3 by associating IAM roles with pods. When a pod tries to access S3, the Pod Identity Agent ensures it has the correct IAM role credentials for authentication.
What is the role of the Pod Identity Agent in EKS Pod Identity?
-The Pod Identity Agent manages the association between the pod, the IAM role, and the namespace. It ensures that the pod’s credentials are updated so the AWS SDK can access the appropriate services securely.
Why is it beneficial that EKS Pod Identity doesn’t require an OIDC provider for every cluster?
-By not requiring an OIDC provider for each cluster, EKS Pod Identity simplifies setup and allows roles to be scoped across multiple clusters, reducing operational complexity.
What is attribute-based access control (ABAC) in the context of EKS Pod Identity?
-Attribute-Based Access Control (ABAC) in EKS Pod Identity allows more granular permissions management, enabling roles to be scoped more effectively based on attributes such as namespaces and service accounts.
What steps are required to configure EKS Pod Identity for accessing an AWS service like S3?
-To configure EKS Pod Identity, you need to create an IAM role with the required permissions, deploy the Pod Identity Agent in the cluster, and then associate the IAM role with the pod’s namespace and service account.
Is EKS Pod Identity compatible with existing IAM Roles for Service Accounts (IRSA)?
-Yes, EKS Pod Identity is fully backwards compatible with IAM Roles for Service Accounts (IRSA), meaning both can coexist, and existing IRSA configurations will continue to work.
Outlines

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraMindmap

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraKeywords

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraHighlights

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraTranscripts

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraVer Más Videos Relacionados
5.0 / 5 (0 votes)