CRYPTOGRAPHY | Encrypting & Decrypting | Caesar Cipher | Modulo Operator | TAGALOG-ENGLISH
Summary
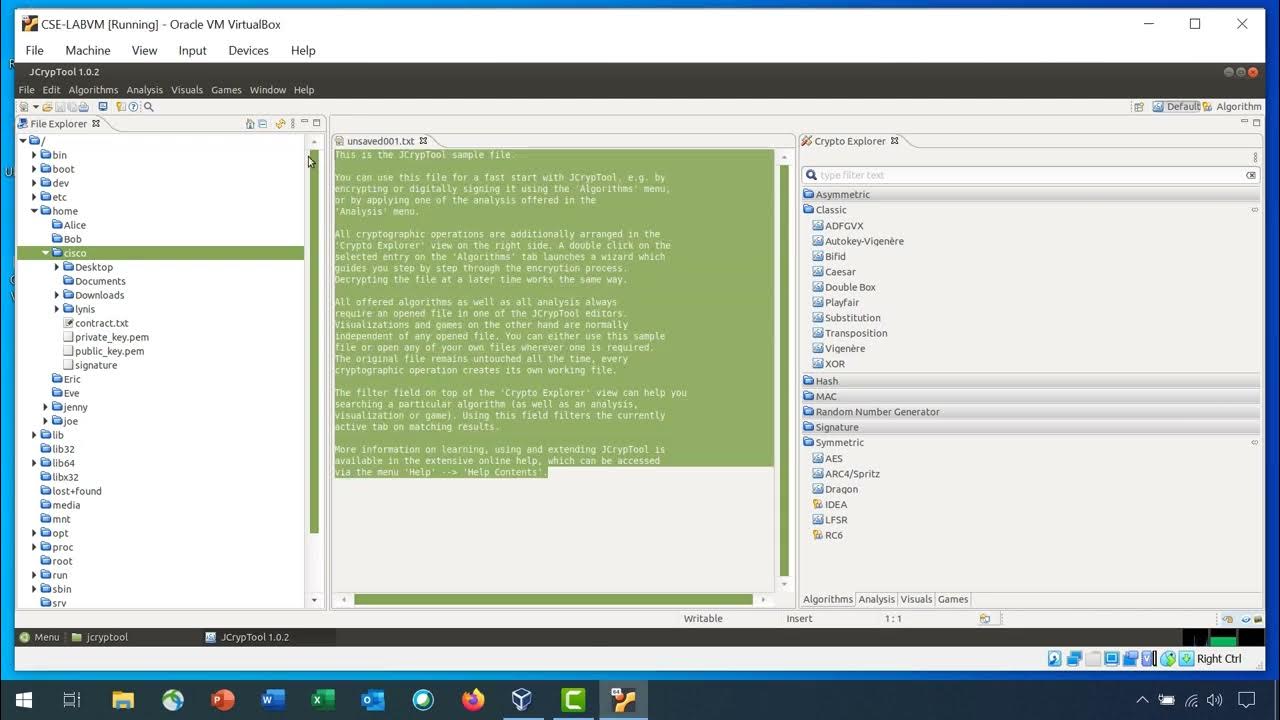
TLDRThis video delves into cryptography, focusing on encrypting and decrypting messages using Caesar cipher and modulo operator. It explains the roots of 'cryptography' and its role in creating secret codes. The Caesar cipher shifts letters by a set number, either to the left or right, for encryption and decryption. The modulo operator uses a key to encrypt by adding it to letter positions and then taking modulo 26 to wrap around the alphabet. The video provides step-by-step examples of both encryption and decryption processes, illustrating how to convert plain text into coded messages and vice versa.
Takeaways
- 🔐 Cryptography is the practice of secure communication, involving the use of codes to encrypt and decrypt messages.
- 📜 The term 'cryptography' comes from 'crypto' meaning hidden and 'graphene' meaning writing, indicating its purpose of hidden writing or secret messages.
- 🔄 Encryption is the process of transforming plain text into code using an algorithm, while decryption is the reverse process.
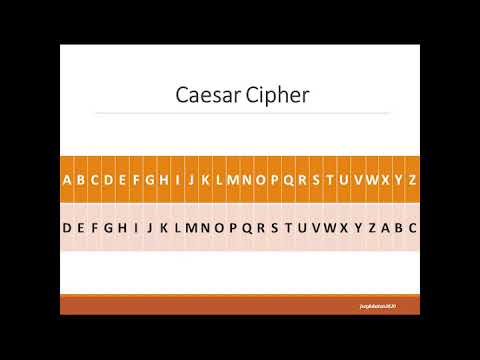
- 🔄 Caesar Cipher is a type of shift cipher where each letter in the plaintext is shifted a certain number of places down the alphabet.
- 🔢 The modulo operator is used in cryptography to encrypt and decrypt messages by adding or subtracting a key to each letter's position in the alphabet.
- 🔑 A key in cryptography is a crucial piece of information used to encrypt or decrypt a message, often shared between the sender and receiver.
- 🔄 For Caesar Cipher, the direction of shifting can be to the left or right, and decryption involves shifting in the opposite direction.
- 🔄 When using the modulo operator, if the result of the encryption exceeds the alphabet size, it wraps around using the modulo operation.
- 🔢 The modulo operator in encryption is represented as ( c = (p * k) % 26 ), where c is the encrypted letter, p is the original letter's position, k is the key, and 26 is the number of letters in the alphabet.
- 🔄 Decryption using the modulo operator involves reversing the encryption process by subtracting the key from the encrypted letter's position and applying the modulo operation.
Q & A
What does the word 'cryptography' mean?
-The word 'cryptography' originates from the two Greek words 'crypto', which means hidden, and 'graphene', which means writing. Therefore, the meaning of cryptography is hidden writing or the practice of creating and breaking secret codes.
What are the two main processes in cryptography?
-The two main processes in cryptography are encryption and decryption. Encryption is the process of transforming plain text into code form using a certain algorithm, while decryption is the process of converting the coded message back into plain text.
What is a key in the context of cryptography?
-In cryptography, a key is a string of information that is used to reveal the encrypted message into a readable form.
What is the Caesar Cipher method?
-The Caesar Cipher method is a type of shift cipher where each letter in the plain text is shifted a certain number of places down or up the alphabet. The key in this method is the number of positions each letter is shifted.
How does the Caesar Cipher method work for encryption?
-In the Caesar Cipher method for encryption, each letter of the plain text is shifted to the right by a certain number of positions determined by the key. For example, with a key of 3, 'A' becomes 'D', 'B' becomes 'E', and so on.
How is decryption performed in the Caesar Cipher method?
-Decryption in the Caesar Cipher method is performed by shifting the encrypted letters in the opposite direction of the encryption. If the encryption used a shift to the right, decryption shifts to the left by the same number of positions.
What is the role of the modulo operator in cryptography?
-The modulo operator in cryptography is used to encrypt and decrypt messages by adding or subtracting a key to the numerical position of each letter in the alphabet and then finding the remainder when divided by 26 (the number of letters in the alphabet).
How does the modulo operator help in encrypting a message?
-When encrypting a message using the modulo operator, each letter of the plain text is converted to its corresponding numerical position, a key is added to it, and then the result is taken modulo 26 to ensure it falls within the range of the alphabet. The resulting number is then converted back to a letter.
Can you provide an example of how the modulo operator is used for decryption?
-For decryption using the modulo operator, each numerical position of the encrypted letter is reduced by the key and then taken modulo 26. For example, if 'E' (which is 4) is encrypted with a key of 3 to become 'H' (which is 7), decryption would involve 7 - 3 mod 26, resulting in 4, which corresponds back to 'E'.
What happens if the result of the modulo operation goes beyond the alphabet range during encryption?
-If the result of the modulo operation goes beyond the alphabet range during encryption, it wraps around to the beginning of the alphabet. For instance, if the result is 27, it would be taken as 1 (since 27 mod 26 is 1), which corresponds to 'A'.
How does the Caesar Cipher differ from using the modulo operator for encryption?
-The Caesar Cipher is a specific type of shift cipher with a fixed number of positions for shifting letters, while the modulo operator can use any integer value as a key, providing a wider range of possible encryptions. The modulo operator also ensures that the result always stays within the bounds of the alphabet.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen
5.0 / 5 (0 votes)