Understanding the Wild Pointers
Summary
TLDRThis presentation delves into the concept of wild pointers, which are uninitialized and can point to arbitrary memory locations, potentially causing program crashes or misbehavior. It explains the risks of dereferencing an uninitialized pointer and demonstrates how it might lead to segmentation faults. The video offers best practices to avoid wild pointers, such as initializing pointers with the address of a known variable or explicitly allocating memory before use. These methods ensure pointers are properly managed, preventing unexpected program behavior.
Takeaways
- 🔍 Wild pointers are also known as uninitialized pointers, which can cause a program to crash or misbehave.
- 📍 These pointers point to arbitrary memory locations, potentially leading to segmentation faults or other errors.
- 🚫 Wild pointers do not contain the address of a valid memory location, making them unpredictable and risky.
- 💡 An example of a wild pointer is when a pointer is dereferenced without being initialized, which can lead to illegal memory access.
- 🛠️ To avoid wild pointers, initialize them with the address of a known variable or object.
- 🗂️ Explicitly allocating memory and initializing pointers with the address of the allocated memory is a recommended practice.
- 🔑 Using malloc to allocate memory and then initializing the pointer with the address of the first byte is a safe approach.
- 📝 It's crucial to ensure that pointers are either assigned to a variable's address or to allocated memory to prevent wild behavior.
- 🛑 Dereferencing an uninitialized pointer can result in writing to illegal memory, which is a common cause of program crashes.
- 🔄 Understanding and avoiding wild pointers is essential for maintaining the stability and reliability of software applications.
- 👍 The presentation concludes with thanks to the viewers, emphasizing the importance of following best practices to prevent wild pointers.
Q & A
What are wild pointers in programming?
-Wild pointers, also known as uninitialized pointers, are pointers that have not been assigned a specific memory address and can point to arbitrary memory locations, potentially causing a program to crash or misbehave.
What is the primary risk associated with using wild pointers?
-The primary risk of using wild pointers is that they may point to unknown or illegal memory locations, which can lead to program crashes, segmentation faults, or other unexpected behaviors.
Why might a program crash when dereferencing a wild pointer?
-A program might crash when dereferencing a wild pointer because it could be attempting to access or write to an illegal or undefined memory location, which is not intended for such operations.
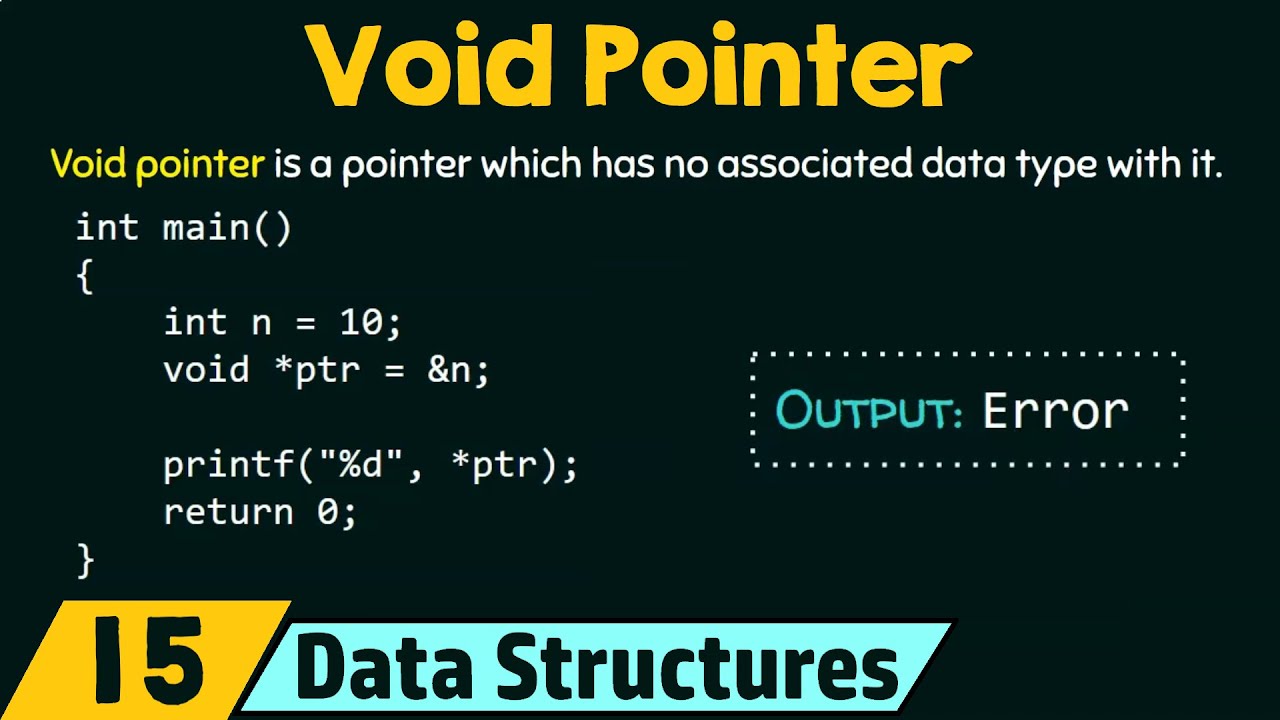
Can you provide an example of how a wild pointer is typically used in the script?
-In the script, an example is given where a pointer is used without being initialized, and an attempt is made to access and store a value at the location it points to, which can result in a crash or segmentation fault.
What is the best practice to avoid using wild pointers?
-The best practice to avoid wild pointers is to initialize them with the address of a known variable or explicitly allocate memory for them using functions like malloc, and then assign the address of the allocated memory to the pointer.
How does initializing a pointer with the address of a variable prevent it from being a wild pointer?
-Initializing a pointer with the address of a variable ensures that the pointer is no longer uninitialized and points to a valid memory location associated with that variable, thus preventing it from being a wild pointer.
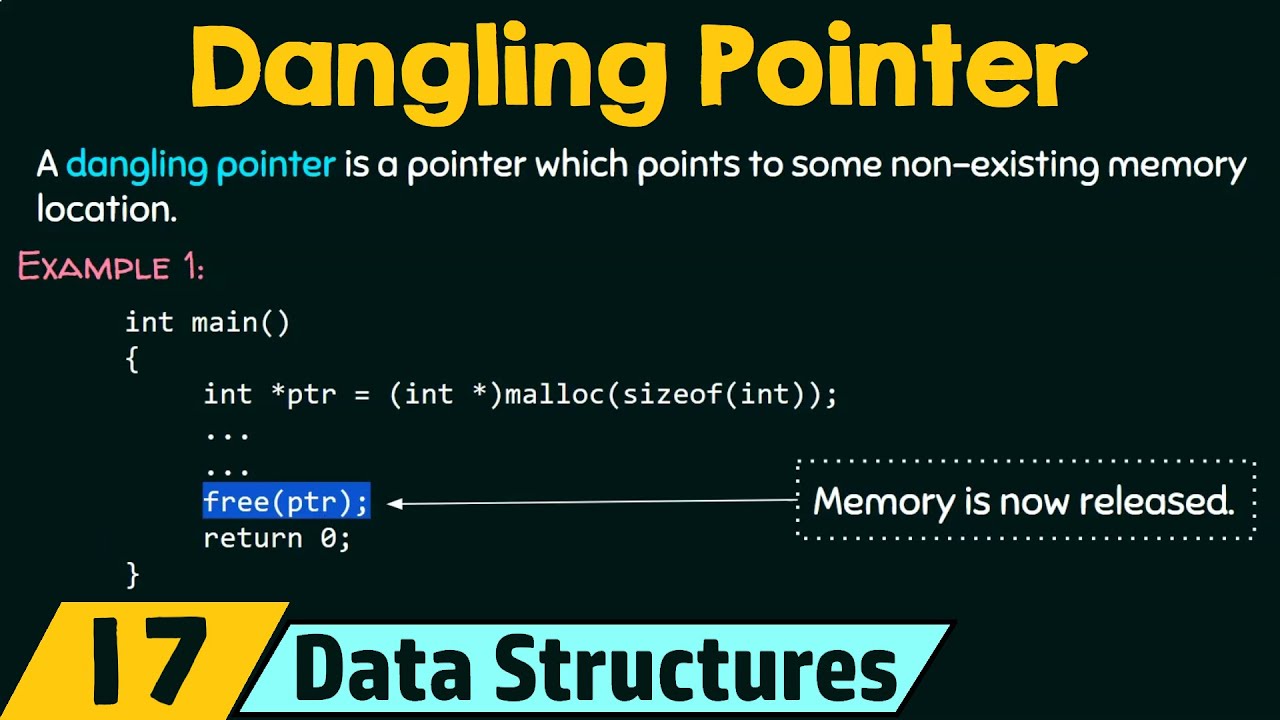
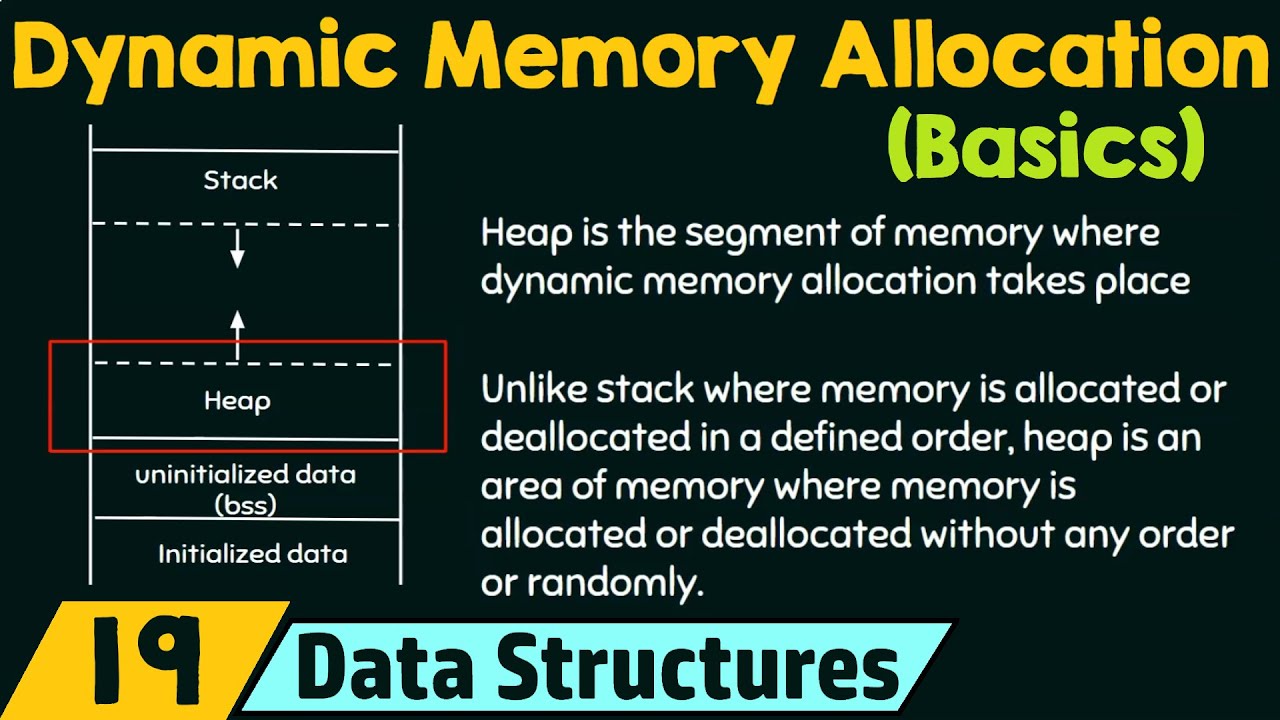
What is the purpose of explicitly allocating memory using malloc in the context of avoiding wild pointers?
-Explicitly allocating memory using malloc provides a legal and specific memory block for the pointer to reference. By initializing the pointer with the address of the first byte of this allocated memory, it ensures that the pointer points to a valid and intended memory location.
What are the two main steps suggested in the script to avoid wild pointers?
-The two main steps suggested are: 1) Assigning the address of a variable, object, or explicitly allocated memory to the pointer, and 2) Ensuring that the memory is properly allocated and initialized before being accessed or modified.
Why is it important to initialize pointers before using them in a program?
-Initializing pointers before use is crucial to ensure that they point to a valid and intended memory location, preventing undefined behavior, crashes, or security vulnerabilities that can arise from pointing to arbitrary or illegal memory addresses.
How can a segmentation fault occur in relation to wild pointers?
-A segmentation fault can occur when a wild pointer, which may be pointing to an illegal or protected memory area, is dereferenced, attempting to read from or write to a memory location that the program is not allowed to access.
What does the script suggest as an alternative to using uninitialized pointers?
-The script suggests initializing pointers with the address of a known variable or explicitly allocating memory for them and then using that allocated memory address to initialize the pointer, as alternatives to using uninitialized pointers.
Outlines

此内容仅限付费用户访问。 请升级后访问。
立即升级Mindmap

此内容仅限付费用户访问。 请升级后访问。
立即升级Keywords

此内容仅限付费用户访问。 请升级后访问。
立即升级Highlights

此内容仅限付费用户访问。 请升级后访问。
立即升级Transcripts

此内容仅限付费用户访问。 请升级后访问。
立即升级5.0 / 5 (0 votes)