Introduction to IP - CompTIA A+ 220-1101 - 2.1
Summary
TLDRThis video explains networking concepts through a moving truck metaphor. The network acts as a road, while IP functions like a moving truck that carries data in boxes to different locations. The box contains application data, which is routed using protocols like TCP or UDP. TCP offers reliable, connection-oriented delivery, while UDP is faster but connectionless. Port numbers determine where data goes within a device. Understanding the difference between TCP and UDP, as well as the use of port numbers, helps in navigating how data is efficiently transmitted across networks.
Takeaways
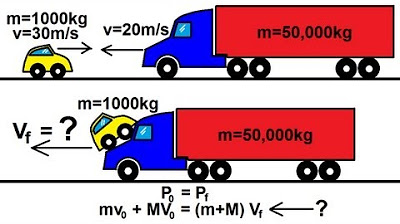
- 😀 The network is like a road, and the moving truck is the Internet Protocol (IP), transporting data from one location to another.
- 😀 Data is encapsulated in packets, which are like boxes being transported by the moving truck (IP) across the network.
- 😀 Inside the box, the data could belong to different applications or functions, similar to how rooms in a house have specific purposes.
- 😀 The encapsulation process involves multiple layers, such as Ethernet, IP, TCP, and application data (like HTTP).
- 😀 TCP and UDP are two common protocols used at the transport layer (OSI Layer 4) to move data across the network.
- 😀 TCP is connection-oriented and reliable, ensuring data delivery and providing mechanisms like retransmission and flow control.
- 😀 UDP, on the other hand, is connectionless and unreliable, sending data without guarantees, making it faster but with no acknowledgment of receipt.
- 😀 UDP is ideal for real-time applications where missing data can be tolerated (e.g., VoIP, DHCP, and TFTP).
- 😀 TCP is used for protocols that require reliable communication, such as HTTPS and SSH, which handle retransmissions and flow control automatically.
- 😀 Every device on a network has a unique IP address, similar to a house address, and the data needs to be routed to the correct application via port numbers.
- 😀 Port numbers act like rooms in a house, ensuring that data goes to the right service (e.g., port 80 for web servers and port 443 for secure HTTPS connections).
Q & A
What is the primary purpose of the moving truck metaphor in networking?
-The moving truck metaphor is used to explain how data is transported across a network. The truck represents the Internet Protocol (IP), which moves data (inside boxes) from one location to another across various networks, such as wireless, DSL, or ethernet.
What role do TCP and UDP play in data transport across networks?
-TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) are protocols used for transporting data within an IP packet. TCP is connection-oriented and ensures reliable, ordered delivery, while UDP is connectionless and does not guarantee delivery, making it faster for real-time applications.
Why is TCP referred to as a 'reliable' protocol?
-TCP is considered reliable because it verifies that data sent over the network has been received at the destination. It uses acknowledgment and retransmission mechanisms to ensure that lost or out-of-order packets are properly handled.
How does UDP differ from TCP in terms of communication?
-UDP is connectionless, meaning there is no setup or teardown process for communication. It simply sends data to the destination without acknowledgment or retransmission, making it faster but less reliable than TCP, which manages communication and ensures packet delivery.
What is the significance of port numbers in networking?
-Port numbers are used to direct data to specific services or applications on a device. They act like rooms in a house where each service (such as web servers, mail servers, etc.) listens on a particular port, ensuring that incoming data is delivered to the correct application.
Why are some port numbers designated as 'well-known'?
-Well-known port numbers are standard port numbers assigned to common services like HTTP (port 80) and HTTPS (port 443). These port numbers are universally recognized and allow devices to know where to send specific types of data across the network.
How do 'ephemeral' port numbers work in networking?
-Ephemeral port numbers are temporary ports assigned by the operating system for the client-side of a connection. These ports are used for the duration of the session and are often assigned from the range 1024 to 65535. Once the session ends, the port is no longer in use.
What are the advantages of using UDP for real-time applications?
-UDP is ideal for real-time applications like VoIP or streaming because it allows for quick data transmission without the delays caused by acknowledgments or retransmissions. It's suitable for scenarios where occasional data loss is acceptable and cannot disrupt the communication flow.
How does TCP handle data flow and congestion control?
-TCP includes mechanisms for flow control and congestion management. If a device is overwhelmed by incoming data, it can signal the sender to slow down. Additionally, if packets are lost or received out of order, TCP will request retransmission and reorder the packets.
Why is port scanning not an effective security measure despite hiding services behind non-standard ports?
-Port scanning can easily identify open ports and reveal which services are running on a server. Therefore, simply changing port numbers does not provide true security. Proper security measures like encryption and authentication are necessary to protect services.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video
5.0 / 5 (0 votes)