Complete Guide to SentinelOne EDR (Endpoint Detection and Response): Exploring the Console in Part 1
Summary
TLDRThe video script offers an in-depth introduction to SentinelOne, a leading endpoint detection and response (EDR) solution used by major corporations. The presenter, from a managed security service provider (MSSP), explains the hierarchical structure of SentinelOne's console, which includes global, account, and site levels. The script delves into various features such as threat detection, remediation actions, and policy configurations. It also touches on advanced capabilities like Deep Visibility for incident response and threat hunting, as well as the Ranger product for network device identification. The presenter highlights the importance of threat and alert management, the use of AI engines, and the integration with Active Directory through Ranger AD. Additionally, the script covers application vulnerability scanning, inventory management, and the significance of the activity log for auditing purposes. The video concludes with a teaser for further detailed exploration of these features in subsequent videos, inviting viewers to subscribe for more comprehensive EDR insights.
Takeaways
- 📊 Sentinel One is a top-tier endpoint detection and response (EDR) product used by large corporations.
- 👥 The platform operates on a tenant structure with levels including Global, Account, Site, and Groups, catering to various customer sizes and needs.
- 🏢 For small businesses like Technology Interpreters, access to Sentinel One is typically through a Managed Security Service Provider (MSSP) that has direct access to Global settings.
- 🔍 The dashboard provides insights into solved and unsolved threats, medicated threats, and the status of endpoints as either infected or healthy.
- 🛠️ Detection engines are a core part of the policy, with various types for detecting files, scripts, and other potential threats.
- 🧐 Deep Visibility is a powerful feature for incident response and threat hunting, but it's restricted to prevent misuse that could lock up the console or database.
- 🚀 The Ranger product identifies devices on the network, especially those without Sentinel One agents, aiding in the detection of rogue devices.
- 🛡️ Policies within the platform determine the actions taken on threats, including blocking, quarantining, remediating, and rolling back changes.
- 🔑 The Site Key is used for software installation, linking devices to a specific tenant within the platform.
- 📋 Identity features, such as Ranger AD and Threat Strike, protect against threats targeting Active Directory and lateral movement within a network.
- 📊 The Application section offers vulnerability scanning, providing risk assessments and inventory details of installed applications and their versions.
Q & A
What is Sentinel One and why is it significant in the cybersecurity industry?
-Sentinel One is a top endpoint detection and response product used by many large companies and managed security service providers (MSSPs). It is significant because it offers comprehensive security solutions, including threat detection, mitigation, and response capabilities.
What is the role of a managed security service provider (MSSP) in the context of Sentinel One?
-An MSSP is a company that manages multiple customers' security needs through a centralized console. They purchase Sentinel One services from a company with access to the global level of Sentinel One and then provide security services to their own customers, acting as an intermediary.
How does the tenant structure work in Sentinel One?
-The tenant structure in Sentinel One starts with the global level, which is managed by the company providing the service. Under the global level, there are accounts, which belong to MSSPs or individual customers. Under accounts, there are sites, which represent individual customer environments or practice areas. Within sites, there can be groups that allow for specific policy assignments and monitoring.
What is Deep Visibility and why is it a valuable feature in Sentinel One?
-Deep Visibility is a feature in Sentinel One that allows users to run queries for incident response or threat hunting. It provides detailed insights into network activities and is valuable because it can help detect and respond to threats more effectively. However, it's only enabled for users who have been trained and certified to use it, to prevent misuse that could lock up the console or database.
What are detection engines in Sentinel One, and how do they contribute to threat detection?
-Detection engines in Sentinel One are components of the security policies that detect various types of threats. They include static detection for files on the machine and other engines that detect scripts or other non-file based threats. These engines are powered by artificial intelligence, which helps in the remediation process of detected threats.
How does the threat intelligence in Sentinel One categorize different types of threats?
-Sentinel One divides threats into different categories, which can include various types of malware and potentially unwanted programs. The specific number of categories may vary, but the system is designed to provide detailed classification to help with the detection and response to threats.
What is the Sentinel One Ranger product, and how does it help in network security?
-The Ranger product is used to identify devices that connect to a network and detect those without Sentinel One agents installed. It helps in network security by alerting the IT or security department about unmanaged devices, potentially identifying rogue devices on the network that need to be protected.
What is the purpose of the Application feature in Sentinel One, and how does it assist with vulnerability management?
-The Application feature in Sentinel One provides a vulnerability scan by using the agent on the machine to assess the software installed. It compares the software against the Common Vulnerability Scoring System (CVSS) to determine the severity of any vulnerabilities found. This helps with vulnerability management by identifying risks and assisting in the remediation process without the need for additional tools like Tenable.
What is the Activity Log in Sentinel One, and why is it important for monitoring console actions?
-The Activity Log in Sentinel One records all actions and events that occur within the console. It is important for monitoring because it allows administrators to track and audit all activities, such as logins, remote access, scans, and device decommissioning. This can help in identifying unauthorized access or actions and ensures transparency in the console usage.
How does the automation feature in Sentinel One benefit administrators in managing large groups of machines?
-The automation feature in Sentinel One allows administrators to run pre-defined scripts, such as PowerShell or shell scripts, on large groups of machines. This can be used for tasks like fixing issues, remediating vulnerabilities, or performing other maintenance tasks. It benefits administrators by streamlining and automating repetitive tasks, saving time and reducing the potential for human error.
What is a policy override in Sentinel One, and when might it be necessary to use it?
-A policy override in Sentinel One is a more advanced method of instructing the AI detection engine to ignore specific parameters, such as processes, hashes, executables, or file types. It might be necessary when standard exclusions do not suffice, and a more detailed instruction is required to prevent the engine from acting on certain items or conditions.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video
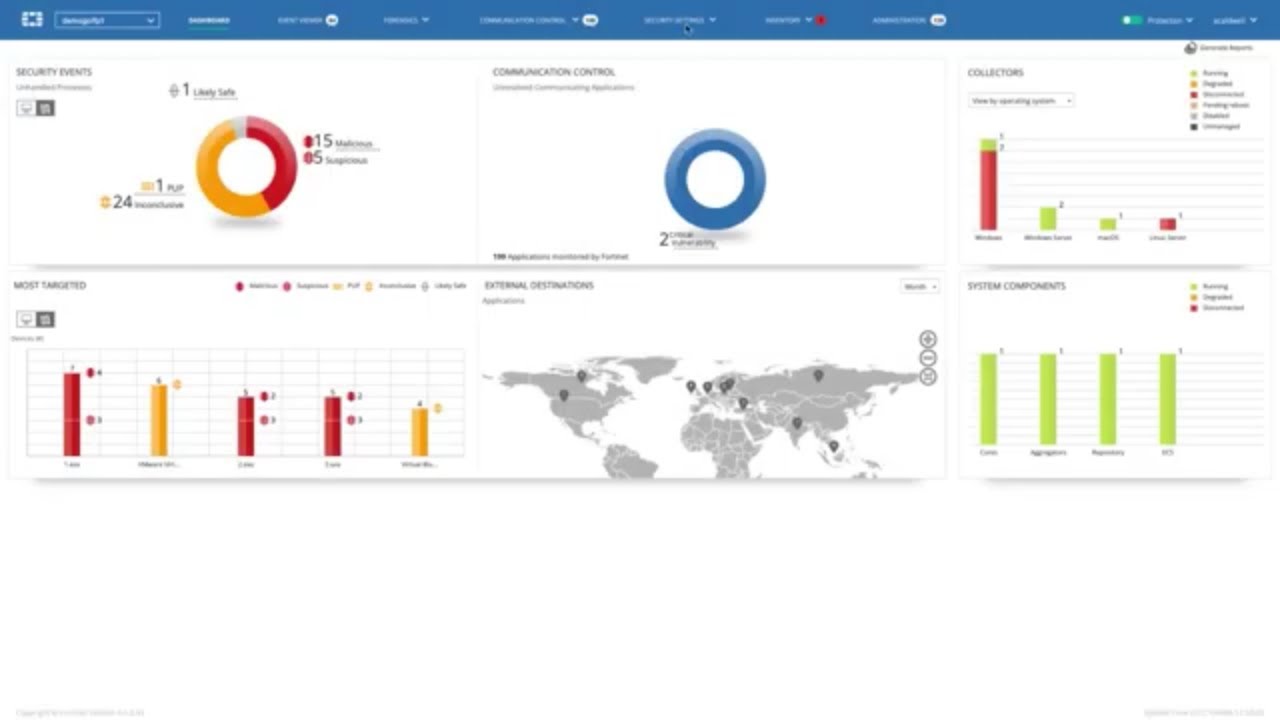
FortiEDR - Advanced Endpoint Protection with Automated Detection and Response | Endpoint Security
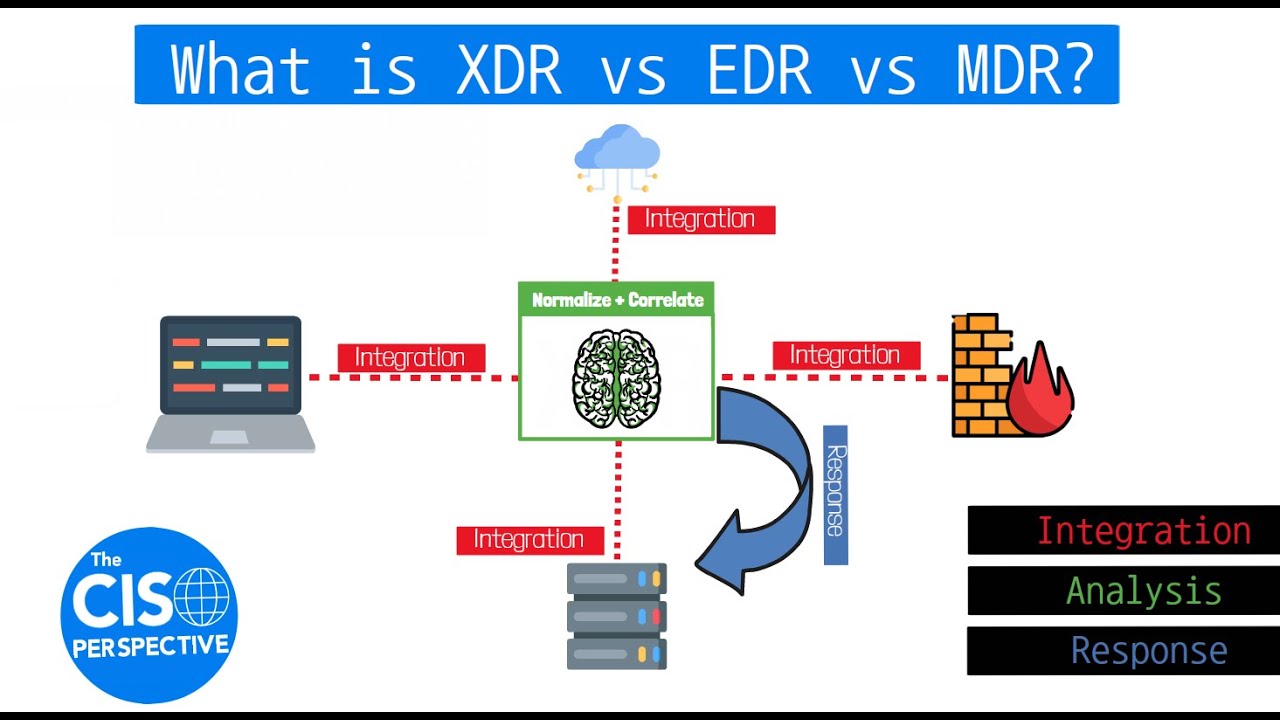
What is XDR vs EDR vs MDR? Breaking down Extended Detection and Response

MDE Tutorial -13 - Endpoint Detection and Response (EDR) in Microsoft Defender for Endpoints

Microsoft Defender for Business EDR to XDR Security Upgrade Using Microsoft 365 Business Premium
Uncovering Cyber Threats: EDR vs SIEM Comparison #cybersecurity #cyber #risk #threats #detective

Microsoft 365 Defender for Endpoint? Good Enough for your Business?
5.0 / 5 (0 votes)