Wireshark - Malware traffic Analysis
Summary
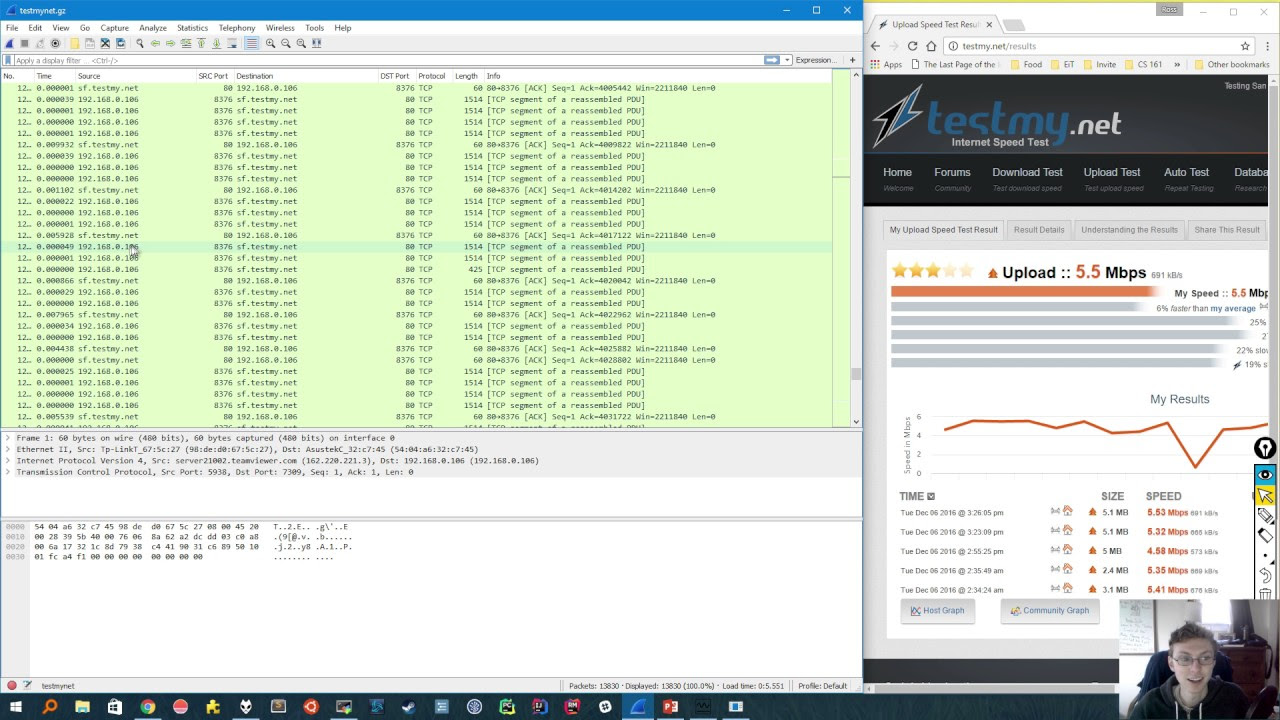
TLDRIn this episode of 'Hack Explored,' the host delves into packet analysis using Wireshark, a vital skill for security professionals. They guide viewers through using Wireshark to analyze network traffic, focusing on identifying indicators of compromised systems, such as IP addresses and domain names. The demonstration includes filtering HTTP traffic, exporting objects, and using tools like VirusTotal to check for malware. The video concludes with tips on blocking malicious files and sites, and further learning resources are suggested for mastering network analysis.
Takeaways
- 📚 The video is an educational tutorial on packet analysis using Wireshark, a leading network traffic analyzer.
- 👨🏫 It is aimed at security professionals, including beginners, and provides step-by-step guides for mastering the tool.
- 🔍 Wireshark is popular for troubleshooting network issues and can reveal interesting events happening on a network.
- 🔑 The script explains how to collect I/O CS, which are forensics data pieces collected during analysis and can indicate compromised systems.
- 🚫 It demonstrates using IP addresses and domain names to block malicious activity detected within a network.
- 🖥️ The tutorial covers how to use Wireshark to analyze network traffic captures, either locally or from sample captures online.
- 📈 The video guides viewers on how to enhance the default view in Wireshark to make analysis easier, such as by modifying the time display format.
- 📊 It emphasizes the importance of understanding the protocols used in a traffic capture and how to filter traffic to focus on specific protocols like HTTP.
- 🔎 The script details how to add and modify columns in Wireshark to better understand the source, destination, and nature of network traffic.
- 🛠️ It shows how to export HTTP objects from a capture to find and save files that may be infected, such as executables or Java files.
- 🛡️ The tutorial suggests using VirusTotal to check the downloaded files for malware by uploading them or checking their hashes.
- 🔗 Finally, the video provides a method to identify the infected machine's hostname, IP address, and MAC address from the captured data.
Q & A
What is the main topic of the video?
-The main topic of the video is packet analysis using Wireshark, a network traffic analyzer, and its importance for security professionals.
Why is packet analysis an important skill for security professionals?
-Packet analysis is important for security professionals to troubleshoot network issues, discover events happening on a network, and collect forensics data known as IoCs (Indicators of Compromise).
What is Wireshark and how is it used in the video?
-Wireshark is a leading network traffic analyzer used in the video to demonstrate how to analyze network traffic, filter specific protocols, and collect data to investigate potential security threats.
What is an IoC (Indicator of Compromise) and how can it be used?
-An IoC is a piece of forensic data collected during analysis, such as IP addresses, domain names, and user agents, which can be used to detect and prevent attacks by identifying compromised systems.
How can an IP address be utilized in cybersecurity?
-In cybersecurity, if an IP address is detected as spreading malware, it can be immediately blocked to prevent further threats to the network.
What is the purpose of the 'protocol hierarchy' in Wireshark?
-The protocol hierarchy in Wireshark provides a summary of the protocol activity within a traffic capture, helping users understand the types of protocols used and focus on relevant sections for analysis.
How can Wireshark filters help in narrowing down the analysis?
-Wireshark filters allow users to display only the traffic of interest, such as HTTP requests, which helps in focusing the analysis on specific activities and reducing the amount of data to be examined.
What is the significance of adding custom columns in Wireshark for analysis?
-Adding custom columns in Wireshark can make the interface more meaningful and understandable by displaying specific information relevant to the analysis, such as source and destination ports, URLs, and hostnames.
How can Wireshark be used to identify and save infected files from a network traffic capture?
-Wireshark can be used to identify file downloads through HTTP requests, and the 'export objects' feature can be utilized to save the files for further analysis, such as checking for malware.
What is the role of VirusTotal in the context of the video?
-VirusTotal is used in the video to check the downloaded files for any infections by uploading the files or their hashes to determine if they are malicious.
How can the information collected from Wireshark be used to prevent future attacks?
-The information collected, such as infected file hashes and IP addresses, can be used to block malicious traffic within the network and conduct investigations on compromised systems to ensure they are cleaned and secure.
What additional resources are mentioned in the video for learning more about packet analysis and Wireshark?
-The video mentions 'Wireshark Network Analysis' by Laura Chappell as a book for learning more about packet analysis, and 'malware_traffic_analysis.net' as a website with exercises related to traffic analysis.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード5.0 / 5 (0 votes)