Supply Chain Vulnerabilities - CompTIA Security+ SY0-701 - 2.3
Summary
TLDRThe video explores the critical importance of supply chain security, highlighting risks at every stage—from raw materials to end-user delivery. It emphasizes that both hardware and software can be compromised, including through service providers, counterfeit devices, and malicious software updates. Real-world cases such as the Target breach, counterfeit Cisco hardware, and the SolarWinds Orion attack illustrate how attackers exploit trust to access sensitive data. The video underscores the need for strict vendor management, network segmentation, security audits, and verification of every component, advocating a proactive, zero-trust approach to safeguard organizations from indirect and often overlooked threats.
Takeaways
- 🔒 The supply chain includes every step from raw materials to the final product, and each step carries potential security risks.
- 👥 Third-party service providers can be a significant security risk if they have access to sensitive systems or data.
- 📝 Organizations should include regular security audits in contracts with service providers to monitor their practices.
- 🏢 The Target breach (2013) demonstrates how attackers can exploit a service provider to access sensitive customer information.
- 💻 Hardware acquired from vendors, such as routers, switches, or firewalls, should be treated as potentially untrusted until verified.
- ⚠️ Counterfeit hardware, like fake Cisco devices, can compromise network security and cause operational failures.
- 🛡️ Software installations and updates should be trusted and verified, ideally through digital signatures and secure sources.
- ⏱️ Automated software updates pose a risk since installations occur without direct oversight, potentially introducing malicious code.
- 💾 Open-source software can also be vulnerable if malicious changes are introduced into the codebase.
- 🌐 The SolarWinds Orion attack (2020) highlights the dangers of compromised software supply chains affecting major corporations and government agencies.
- 🔑 Trust is the foundation of security, and organizations must ensure every step of the supply chain—from hardware to software—is verified and monitored.
Q & A
What is the supply chain in the context of this transcript?
-The supply chain refers to the entire process of getting a product from raw materials through manufacturing, distribution, and delivery to the end consumer. Security concerns can arise at any step in this process.
Why is supply chain security important?
-Supply chain security is critical because attackers can exploit vulnerabilities at any stage—such as suppliers, manufacturers, or service providers—to gain access to systems, inject malicious code, or compromise sensitive data.
How can third-party service providers introduce security risks?
-Third-party providers may have access to critical systems or sensitive data. If an attacker compromises a service provider, they could indirectly gain access to the organization’s systems and data, as seen in the Target credit card breach.
What happened in the Target Corporation breach in 2013?
-The breach started when attackers infected a third-party HVAC service provider with malware. The compromised vendor had network access to Target's systems, which allowed attackers to access cash registers and steal 40 million credit card records.
Why should hardware be treated as potentially untrusted?
-New hardware such as switches, routers, or firewalls could be compromised during manufacturing or distribution. Even if it comes from trusted vendors, it should be verified and treated as potentially insecure until properly validated.
What example was given about counterfeit hardware?
-In 2022, a reseller sold counterfeit Cisco products worth over a billion dollars. These devices were manufactured abroad, mislabeled as Cisco, and some were defective or hazardous, highlighting the risks of unverified hardware.
How can organizations verify software trustworthiness?
-Organizations should check the digital signatures of software installations and updates to ensure authenticity. Automatic updates also require trust in the software source, and open-source software must be carefully monitored for unauthorized changes.
What was the SolarWinds Orion supply chain attack?
-Attackers gained access to SolarWinds systems and inserted malicious code into software updates. These updates, digitally signed, were sent to ~18,000 customers, including major corporations and U.S. government agencies, allowing attackers to infiltrate sensitive networks.
Why are supply chain attacks often hard to detect?
-Supply chain attacks exploit trusted processes or providers, making them less visible. In the SolarWinds case, the compromise occurred in March–June 2020 but was only detected in December 2020, showing how delays in detection are common.
What are best practices for managing supply chain security?
-Best practices include maintaining trusted vendor relationships, auditing service providers, verifying hardware and software authenticity, treating new devices as untrusted, and using digital signatures and other verification tools.
Can non-IT service providers create security vulnerabilities?
-Yes. Even providers for office cleaning, payroll, utilities, or cloud services can inadvertently provide attackers with access to sensitive systems if proper security measures are not in place.
What is the overall lesson about trust in supply chains?
-Trust is essential but must be verified at every step. Organizations should assume that any part of the supply chain—hardware, software, or service providers—could be compromised and enforce procedures to minimize risk.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード関連動画をさらに表示
WHAT IS SUPPLY CHAIN MANAGEMENT ? 5 MINUTES EXPLANATION !!
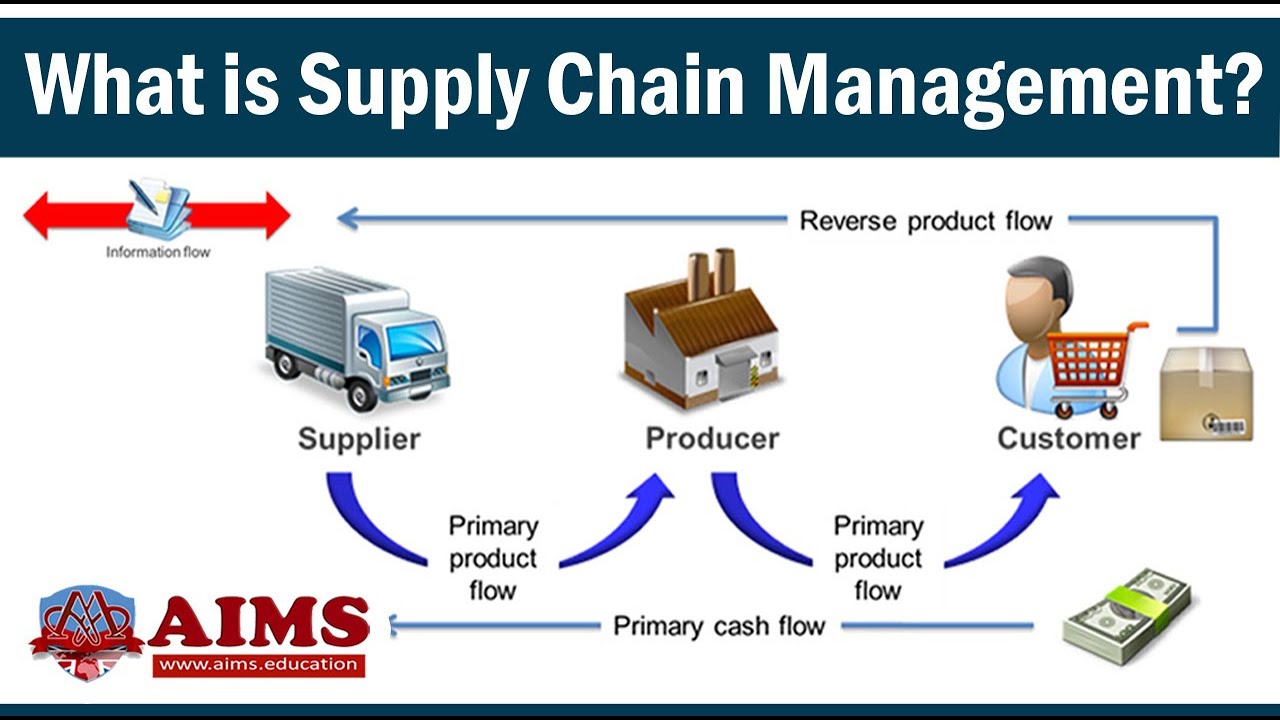
What is Supply Chain Management? Definition, Introduction, Process & Examples - AIMS UK

PES 2024 - DAY 1 - EUROPEAN CHAT: The Future of Global Trade – SPEECHES

Supply Chain Management PT. Garudafood Putra Putri Jaya - Kelompok 5

#1.1 Konsep Dasar Manjemen Rantai Pasok (Pengantar SCM)

CADEIA de SUPRIMENTOS e LOGÍSTICA
5.0 / 5 (0 votes)
