DDoS Attack | DDoS Attack Explained | What Is A DDoS Attack? | Cyber Attacks Explained | Simplilearn
Summary
TLDRThis video from Simply Learn explores the concept of Distributed Denial of Service (DDoS) attacks, detailing their mechanics and the damage they can inflict on both individual users and large corporations. It covers the types of DDoS attacks, including volume-based, protocol level, and application layer attacks, and discusses the motives behind such cyber assaults. The video also offers practical advice on prevention and mitigation strategies, such as using load balancers, firewalls, and CDNs. A demonstration using VMware and Parrot Security OS illustrates the impact of a DDoS attack on a server system, highlighting the importance of robust cybersecurity measures.
Takeaways
- 🏡 Work from home has increased internet usage, making individuals and organizations more vulnerable to cyber threats like DDoS attacks.
- 🚀 DDoS attacks have escalated, with three of the six strongest attacks occurring in 2021, highlighting the growing severity of these incidents.
- 🤖 Cybercriminals are leveraging botnets and compromised devices to amplify DDoS attacks, making them more disruptive.
- 🔒 Multinational corporations, including GitHub, have faced significant DDoS attacks, emphasizing the broad impact on businesses.
- 🔄 DDoS attacks involve a two-phase process: creating a botnet and then launching an attack on a target, overwhelming it with traffic.
- 📊 There are three main types of DDoS attacks: volume-based, protocol-level, and application-level, each with different methods and goals.
- 💡 Hackers may launch DDoS attacks for various reasons, including gaining a competitive advantage, extortion, or making political statements.
- 🛡️ Companies can protect against DDoS attacks by using load balancers, firewalls, and early detection systems to manage and mitigate traffic.
- ☁️ Cloud providers offer enhanced cybersecurity measures, including DDoS protection, and can provide network redundancy to maintain service continuity.
- 🌐 Increasing bandwidth and using a Content Delivery Network (CDN) can help分散流量, reducing the impact of DDoS attacks by avoiding a single point of failure.
Q & A
What is a DDoS attack?
-A DDoS attack is a type of cyber attack where multiple systems flood a target with a overwhelming amount of traffic or requests, rendering it inaccessible to legitimate users by consuming all its bandwidth and system resources.
How do hackers create a botnet for DDoS attacks?
-Hackers create a botnet by infecting multiple devices with malware, ransomware, or through social engineering. These compromised devices, known as bots or zombies, can then be remotely triggered to send traffic to a target server.
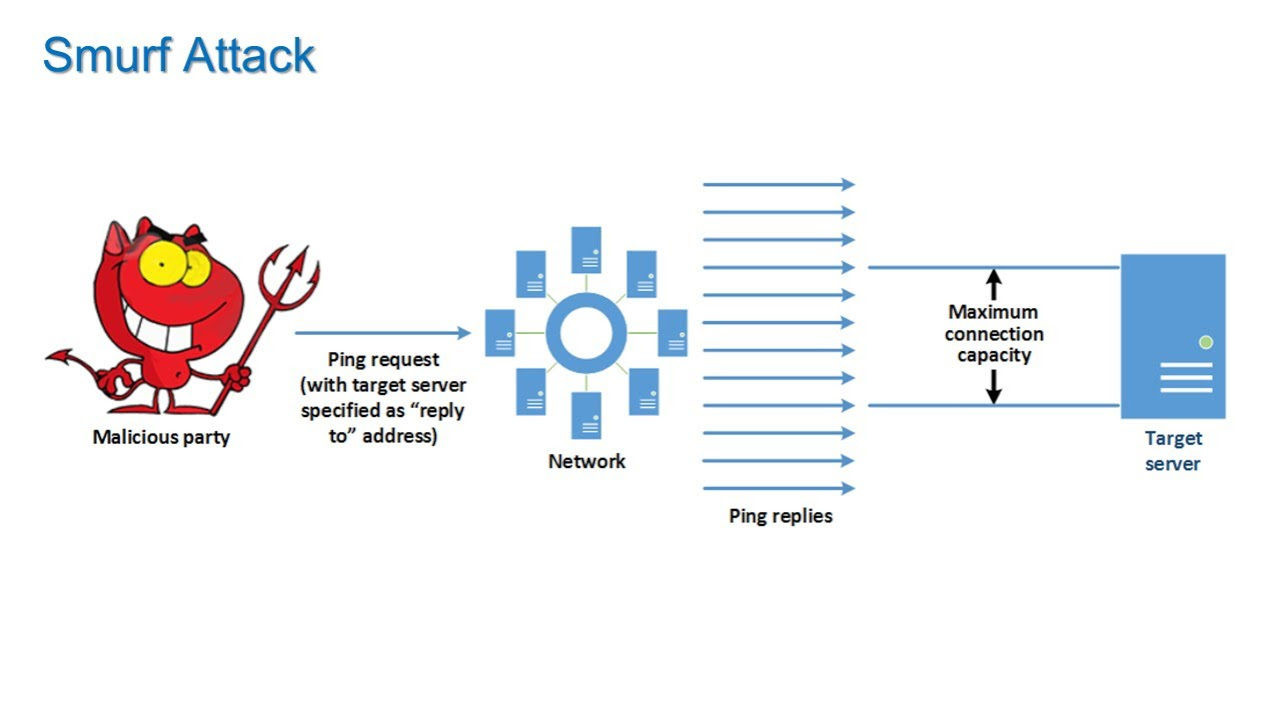
What are the three broad categories of DDoS attacks mentioned in the script?
-The three broad categories of DDoS attacks are volume-based attacks, protocol-level attacks, and application-level attacks. Volume-based attacks overwhelm resources with traffic, protocol-level attacks consume essential server resources, and application-level attacks target application and operating system vulnerabilities.
What is the purpose of using a SYN flood in a DDoS attack?
-A SYN flood is used in DDoS attacks to exhaust the resources of the target server. It does this by initiating a connection with a SYN request but never completing the handshake, causing the server to hold open connections and resources, eventually leading to denial of service.
Why would a hacker launch a DDoS attack to hold a company at ransom?
-A hacker might launch a DDoS attack to hold a company at ransom to force the company to pay a designated amount of money to the hackers. The attack disrupts the company's services, which can be detrimental to their reputation and market value, prompting them to pay to restore service.
What is the role of load balancers in mitigating DDoS attacks?
-Load balancers play a crucial role in mitigating DDoS attacks by distributing incoming traffic across multiple servers. This helps to prevent any single server from becoming overwhelmed and ensures that legitimate traffic can still be processed during an attack.
How can a CDN help in protecting against DDoS attacks?
-A Content Delivery Network (CDN) can help protect against DDoS attacks by distributing content across multiple servers in different locations. This not only reduces the load on any single server but also ensures that there is no single point of failure, making it harder for an attack to take down the entire service.
What is the significance of the GitHub DDoS attack mentioned in the script?
-The GitHub DDoS attack mentioned in the script is significant because it was one of the strongest DDoS attacks at the time, lasting about 20 minutes and causing the platform to reconsider its security practices. It highlights the impact that DDoS attacks can have on even large, well-established platforms.
What is the difference between a DDoS attack and a DoS attack?
-The main difference between a DDoS attack and a DoS attack is the source of the malicious traffic. A DoS attack comes from a single system, while a DDoS attack originates from multiple systems, often part of a botnet, making it more difficult to defend against due to the distributed nature of the attack.
What are some preventive measures that can be taken to protect against DDoS attacks?
-Some preventive measures against DDoS attacks include employing load balancers and firewalls, using cloud providers with high levels of cybersecurity, increasing available bandwidth, and utilizing CDNs. Early detection and response, including filtering traffic and blocking offending IPs, are also crucial.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード5.0 / 5 (0 votes)