All-In-One Open Source Security Scanner | Docker Image Analysis with Trivy
Summary
TLDRThis video from the Blue Team Training series explores Docker image analysis with Trivy, emphasizing the importance of vulnerability scanning for container security. It introduces Trivy, a tool for scanning images, file systems, and Git repositories for vulnerabilities and misconfigurations. The tutorial demonstrates how to use Trivy to identify and address security issues in Docker images, showcasing its capabilities through practical examples and emphasizing the significance of incorporating vulnerability scanning into Docker workflows.
Takeaways
- 🔍 Vulnerability scanning for Docker images is crucial for identifying security risks in packages used in Docker images.
- 🛠️ Trivi is a comprehensive tool for scanning Docker images, file systems, and Git repositories for vulnerabilities and configuration issues.
- 📋 The process involves understanding the importance of vulnerability scanning, an introduction to Trivi, and a practical demonstration of scanning Docker images with Trivi.
- 🐳 Docker containers are created from Docker images, which are defined by Dockerfiles that specify the packages and configurations used.
- ⚠️ Vulnerabilities in the packages used in Docker images can lead to potential exploitation by attackers.
- 🔧 It is important to scan Docker images for vulnerabilities before deploying them to ensure the security of the containerized applications.
- 🔒 Trivi can also scan Infrastructure as Code (IaC) files like Terraform, Dockerfiles, and Kubernetes configurations for potential issues.
- 💾 A practical demonstration shows how to set up and use Trivi on an Ubuntu server with Docker installed to scan for vulnerabilities.
- 📊 Trivi outputs detailed information on detected vulnerabilities, including severity, affected packages, and fixed versions.
- 🛡️ Regularly scanning and updating Docker images based on Trivi's findings helps maintain secure container environments.
Q & A
What is the main focus of the video?
-The main focus of the video is Docker image analysis with Trivy, specifically scanning Docker images for vulnerabilities and misconfigurations.
Why is vulnerability scanning for Docker images important?
-Vulnerability scanning for Docker images is important because it helps identify security vulnerabilities in the packages used within a Docker image, preventing potential exploitation by attackers and ensuring container security.
What are the prerequisites for using Trivy as demonstrated in the video?
-The prerequisites for using Trivy include basic familiarity with Docker and Docker CLI commands, as well as familiarity with Linux and various command line utilities.
What is Trivy and what can it be used for?
-Trivy is a tool for scanning vulnerabilities in container images, file systems, and Git repositories, as well as for configuration issues. It can be used to scan infrastructure as code (IaC) files such as Terraform, Dockerfile, and Kubernetes to detect potential configuration issues.
How does Trivy help with Docker security?
-Trivy helps with Docker security by scanning Docker images for vulnerabilities and misconfigurations, allowing users to identify and fix issues before deploying or running the images.
What is the significance of scanning Docker images before deployment?
-Scanning Docker images before deployment is significant because it allows detection of vulnerabilities that could be exploited by attackers, ensuring that the images are as secure as possible before they are used in production environments.
What does the video demonstrate in terms of practical application of Trivy?
-The video demonstrates a practical application of Trivy by showing how to scan Docker images for vulnerabilities and misconfigurations, including pulling the Trivy Docker image, running scans on specific images, and interpreting the results.
What is the Shell Shock vulnerability mentioned in the video?
-The Shell Shock vulnerability is a family of security bugs in the Unix Bash shell, which allows attackers to remotely execute arbitrary commands. It was first disclosed in September 2014 and is considered critical due to its potential for remote exploitation.
How does Trivy categorize vulnerabilities in its scan results?
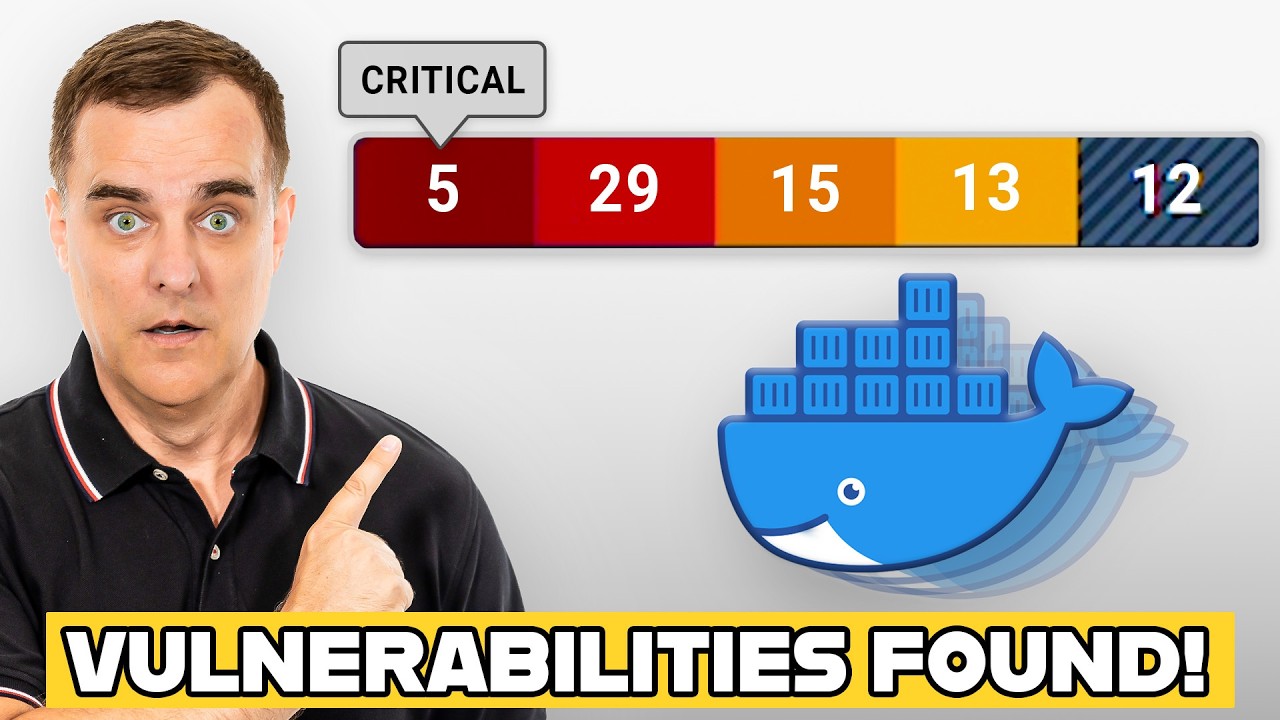
-Trivy categorizes vulnerabilities in its scan results based on their severity, which can include low, medium, high, and critical levels.
What is the next topic covered in the series after Docker image analysis with Trivy?
-The next topic covered in the series is incident response with FireEye Redline, a tool developed by FireEye for incident response and digital forensics.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes
Never use a Docker container without doing this first! (And don't create one either!)

Blue Team Training Course - Introduction

18 Weird and Wonderful ways I use Docker

SpeedTalk Pentera - The LOLBAS Odyssey: Tracing the Path of Finding Hidden Gems in Executables

How to Dockerize Spring Boot Apps | Containerize and Deploy Microservices with Docker

What is Cloud Security?
5.0 / 5 (0 votes)
