Kali Linux: Hacking Networks Part 1
Summary
TLDRThis video tutorial demonstrates how to hack Cisco switches using Kali Linux and the Yersinia framework, focusing on layer 2 attacks. The presenter guides viewers through the installation of Kali, the setup of a small network, and the use of Yersinia to exploit protocols such as CDP, DTP, and STP. Key misconfigurations on a Cisco switch are highlighted, showcasing how attackers can leverage these vulnerabilities. The tutorial emphasizes the importance of understanding networking protocols for effective penetration testing and invites viewers to subscribe for further insights into hacking techniques.
Takeaways
- 😀 The video demonstrates how to hack Cisco switches using Kali Linux and the Yersinia framework.
- 🛠️ A previous video covered the installation of Kali Linux on a Windows 10 computer.
- 🔍 Yersinia supports various layer 2 attacks against protocols such as CDP, DTP, DHCP, HSRP, and more.
- 📡 Understanding network protocols is crucial for successfully hacking Cisco networks.
- 💻 The demonstration involves a basic network setup with a Cisco Catalyst 2960CG switch and devices connected via Ethernet.
- ⚠️ Default configurations on network devices can pose significant security risks and should be avoided.
- 🔌 The configuration of VLANs and DHCP on the switch is examined to understand the network layout.
- 🌐 The tutorial covers how to install Yersinia on Kali Linux, which is no longer included by default in the latest release.
- 🚦 The video includes practical examples of flooding the CDP table and performing spanning tree attacks.
- 📅 Viewers are encouraged to subscribe for more content on hacking techniques and network security.
Q & A
What is the primary focus of the video?
-The video demonstrates how to hack Cisco switches using Kali Linux, specifically employing the Yersinia framework for layer 2 attacks.
What prerequisite knowledge should viewers have before watching this video?
-Viewers should have an understanding of various network protocols, particularly those mentioned like CDP, DTP, HSRP, and others, to effectively follow the hacking techniques demonstrated.
Why is Kali Linux used in this demonstration?
-Kali Linux is used because it is a specialized Linux distribution designed for penetration testing and security auditing, making it suitable for ethical hacking purposes.
What does Yersinia allow users to do?
-Yersinia is a framework that enables users to perform attacks on multiple network protocols, such as Spanning Tree Protocol (STP), CDP, DTP, DHCP, and others, primarily targeting Cisco networks.
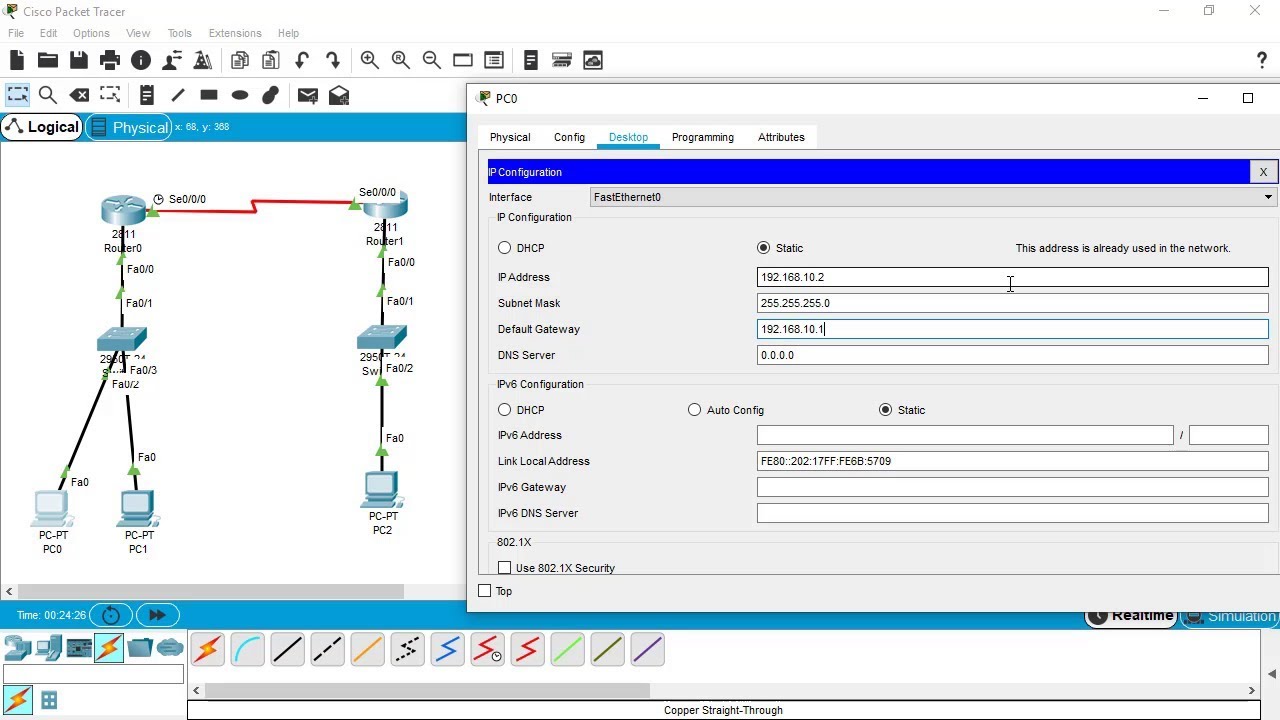
How is the network topology set up in the video?
-The network consists of a Cisco Catalyst 2960CG switch, a Windows 10 laptop, and a MacBook, with both laptops connected to the switch via Ethernet cables.
What command is used to install Yersinia on Kali Linux?
-The command used is 'apt-get install yersinia' after updating the package references with 'apt-get update'.
What issue arises when the presenter first tries to access Yersinia?
-The presenter finds that Yersinia is not installed by default in the latest version of Kali Linux being used, necessitating an installation.
What does the presenter demonstrate regarding the Cisco switch's configuration?
-The presenter shows that the switch is improperly configured, including enabled DTP on ports and the absence of best practices, making it vulnerable to attacks.
What is the significance of flooding the CDP table on the switch?
-Flooding the CDP table can overwhelm the switch's processing capabilities and disrupt normal operations, showcasing a simple yet effective attack method.
What happens when the presenter launches a Spanning Tree attack?
-By claiming the root role in the Spanning Tree, the presenter can manipulate the switch's topology, altering which device is considered the root and potentially causing network disruptions.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes

Cara install Kali Linux di virtualbox terbaru 2024!
Tutorial Install Kali Linux Terbaru di Virtualbox 2025

Kali Linux: Hacking ARP
SSH Configuration on Cisco Routers and Switches using Cisco Packet Tracer

How To Install And Run ZPhisher on Kali Linux Phishing Tool - Video 2023 with InfoSec Pat

Lab Setup for Cybersecurity in Mobile Phone
5.0 / 5 (0 votes)
