How to connect EC2 instance over SSH using Windows and Mac? | Visual Explanations
Summary
TLDRIn this informative tutorial, the host guides viewers through the process of connecting to an Amazon Web Services (AWS) EC2 instance using various tools and methods. Starting with the creation of an EC2 instance on AWS, the host then demonstrates how to connect to it via SSH with both Windows and Mac/Linux systems. For Windows 10, PowerShell and Command Prompt are used, while PuTTY and MobaXterm are recommended for older Windows versions. On Mac, the default terminal is utilized, and tools like Terminus are highlighted for a more user-friendly interface. The video also covers key management and permission settings to ensure secure connections. This comprehensive guide is designed to help users effectively manage and connect to their AWS instances.
Takeaways
- 🚀 The video continues a tutorial series on connecting to AWS EC2 instances using SSH.
- 💻 The presenter demonstrates how to create a new EC2 instance using Amazon Linux 2 AMI and a T2 micro instance, which is free tier eligible.
- 🔑 A new key pair is created and downloaded for secure SSH access to the instance.
- 🖥️ The video covers different methods to connect to the EC2 instance from both Windows and Mac/Linux systems.
- 🛠️ For Windows 10 users, the presenter shows how to use PowerShell and Command Prompt to SSH into the instance after enabling SSH and setting the correct permissions on the key file.
- 🔒 The importance of protecting the SSH key file with proper permissions is emphasized to ensure secure access.
- 🔄 For older Windows versions, the use of PuTTY as an alternative to connect to the EC2 instance is suggested.
- 🔗 The process of converting a PEM file to PuTTY's PPK format using PuTTYgen is explained.
- 🌐 The video introduces MobaXterm as a tool for Windows users to connect to EC2 instances with a graphical interface.
- 🍎 On Mac, the presenter uses the Terminal application to demonstrate the SSH connection process, including setting key permissions.
- 🎨 Terminus is highlighted as a favorite tool for Mac users, offering a visually appealing UI for managing and connecting to SSH hosts.
Q & A
What is the main topic of the video?
-The main topic of the video is about connecting to an AWS EC2 instance using different methods and tools on Windows, Linux, and Mac.
What are the steps to create a new EC2 instance in AWS as described in the video?
-The steps include selecting the Amazon Linux 2 AMI, choosing the T2 micro instance which is free tier eligible, configuring the instance details without changes, adding a name tag, setting up a security group, and launching the instance with a new key pair.
What is the default username for connecting to an Amazon Linux AMI instance?
-The default username for connecting to an Amazon Linux AMI instance is 'ec2-user'.
How can one check if SSH is enabled on Windows 10?
-One can check if SSH is enabled on Windows 10 by opening PowerShell or Command Prompt and typing 'ssh' to see if there are options displayed or if there's an error like 'switch command not found'.
What is the process to connect to an EC2 instance using SSH on Windows 10?
-The process involves opening PowerShell or Command Prompt, typing 'ssh' followed by the username 'ec2-user' and the instance's IP address, trusting the machine if prompted, and associating the previously downloaded SSH key to the command using the '-i' flag followed by the key file path.
Why is it important to protect the SSH key file when connecting to an EC2 instance?
-It is important to protect the SSH key file because the key is used to authenticate your connection to the EC2 instance securely, and an unprotected key can pose a security risk.
What is the recommended permission setting for the SSH key file on Windows?
-The recommended permission setting for the SSH key file on Windows is to allow modifying the file only by the user who owns it, by removing permissions for all other users and setting full control for the owner.
How can one connect to an EC2 instance using PuTTY on an older version of Windows?
-One can connect to an EC2 instance using PuTTY by installing PuTTY, entering the hostname or IP address, specifying the username 'ec2-user', and using a PuTTY-compatible SSH key file (.PPK) which is created by importing the original .pem file using PuTTYgen.
What is MOBA Xterm and how is it used to connect to an EC2 instance?
-MOBA Xterm is a terminal emulator for Windows that provides a graphical interface for SSH connections. It is used to connect to an EC2 instance by creating a new SSH session, entering the username and IP address, specifying the private key file, and establishing the connection.
What is the recommended permission setting for the SSH key file on Mac?
-The recommended permission setting for the SSH key file on Mac is to change the permissions using 'chmod 400' command, allowing read access only to the owner of the file.
What is Terminus and how does it facilitate connecting to an EC2 instance?
-Terminus is a terminal management tool with a graphical user interface. It facilitates connecting to an EC2 instance by allowing users to add a new host with a label and IP address, specify the username and SSH key, and connect with a single click.
Outlines

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraMindmap

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraKeywords

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraHighlights

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraTranscripts

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraVer Más Videos Relacionados

Hosting Dynamic Website Using AWS EC2 Instance

AWS Cloud Quest - Computing Solutions - basketball court is the reward!
HOW TO CONNECT TO EC2 INSTANCE FROM WINDOWS LAPTOP | MOBAXTERM | #aws #devops #abhishekveeramalla
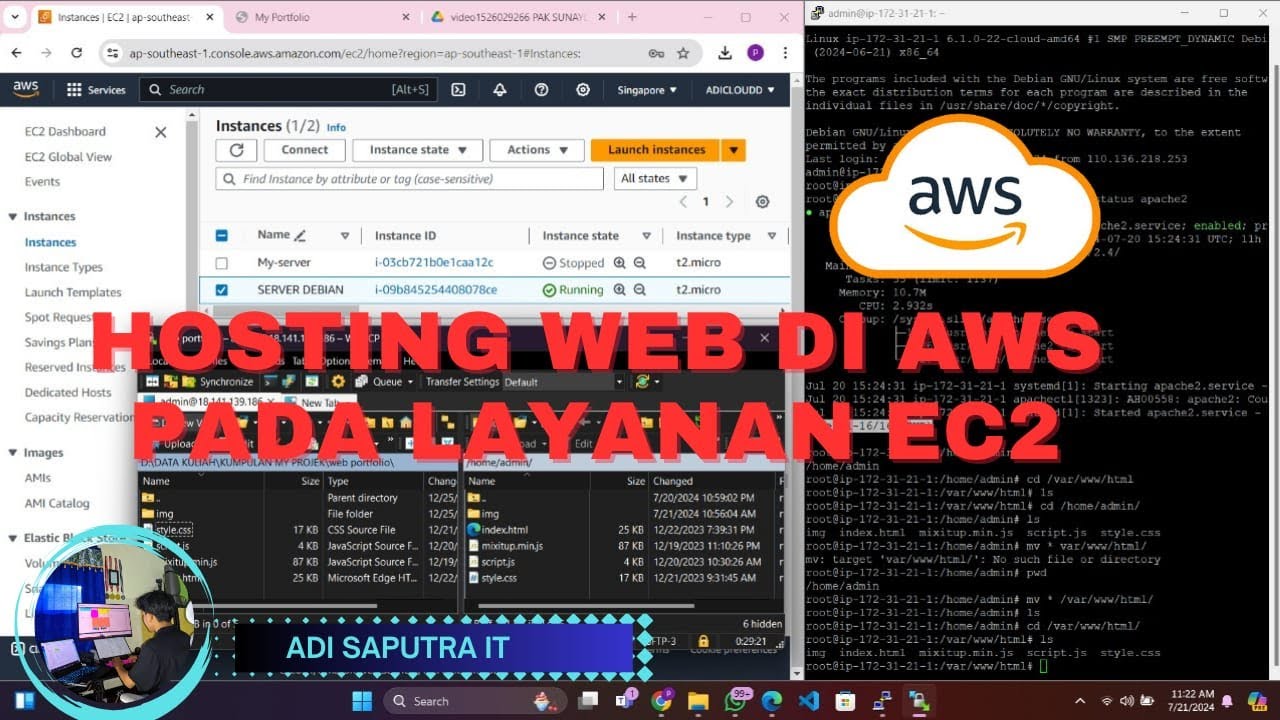
CARA HOSTING/UPLOAD WEBSITE DI AWS MENGGUNAKAN LAYANAN EC2
Hosting Your Resume on AWS EC2 with a CI/CD Setup Using GitHub Actions | AWS Project Demo

How To: Route 53 Health Checks (4 Min) | AWS | Monitor Health & Performance Of Your Web Application
5.0 / 5 (0 votes)
