Cara Mengamankan Website dari Serangan Hacker | IDCloudHost
Summary
TLDRThis video script highlights the rapid advancements in technology and the potential risks of cyber-attacks, especially for business owners, bloggers, and website administrators. It outlines various types of cyber threats, such as malware, denial-of-service attacks, man-in-the-middle attacks, cross-site scripting, and phishing. The script offers practical advice on securing websites, including regular data backups, implementing SSL, using firewalls, updating software, and choosing a reliable hosting service with anti-DDoS systems. It emphasizes the importance of proactive measures to protect against the ever-evolving tactics of hackers.
Takeaways
- 😨 Cybersecurity is a growing concern with 1.2 billion cyberattacks daily in Indonesia, posing a serious threat to both government and businesses.
- 🔒 To protect websites, it's crucial to understand the types of cyberattacks, such as Malware, which can infect sites through harmful links or attachments.
- 🚫 Denial-of-Service (DoS) attacks disrupt servers by flooding websites with traffic, making them inaccessible to legitimate users and causing significant damage.
- 🕵️♂️ Man-in-the-Middle attacks involve hackers intercepting communication between users, potentially modifying and redirecting information.
- 🤖 Cross-Site Scripting (XSS) attacks target websites by injecting malicious scripts, leading to data theft and damaging the site's reputation.
- 🎯 Phishing attacks deceive users into visiting fake websites to steal their data, often without the victim's awareness.
- 💾 Regular data backups are essential for website security, ensuring data is not lost even if the hosting service provides automatic backups.
- 🔐 Installing Secure Socket Layer (SSL) certificates protects websites from data theft, prevents data mishandling, and enhances the site's reputation and visitor trust.
- 🛡️ Firewalls are critical security systems that monitor and control incoming and outgoing network connections, protecting data from hacker attacks.
- 🔄 Keeping software and applications updated is vital to prevent hackers from exploiting vulnerabilities in outdated systems.
- 🏢 Choosing a trusted hosting provider with robust security measures, like anti-DDoS systems and load balancers, can significantly enhance website security.
Q & A
What is the main concern discussed in the video script regarding technology advancement?
-The main concern is the potential risks associated with technology, especially for business owners, bloggers, and website owners who may be targeted by hackers.
According to the data from the Ministry of Communication and Information, how many cyber attacks occurred daily in Indonesia in 2017?
-There were 1.2 billion cyber attacks daily in Indonesia in 2017.
What is the impact of cyber attacks on the government's efforts to maintain data security on the internet?
-Cyber attacks pose a serious threat to the government's efforts to ensure data security on the internet.
What is the first type of cyber attack mentioned in the script, and how does it occur?
-The first type of cyber attack mentioned is Malware, which often occurs through harmful software when users click on dangerous links or open malicious attachments that automatically install harmful applications.
What is the purpose of a Denial-of-Service (DoS) attack, and how does it affect a website?
-A Denial-of-Service (DoS) attack aims to disrupt a specific server by flooding the hosting site with traffic, making it inaccessible to legitimate users and potentially paralyzing the website, causing significant losses.
What is a Man-in-the-Middle attack, and how does it compromise communication between users?
-A Man-in-the-Middle attack involves a hacker intercepting the communication path between two users, gaining access to all information exchanged, and potentially altering or redirecting the communication, leading to disruptions and unauthorized access.
What is Cross-Site Scripting (XSS), and how does it affect a website's reputation and user data?
-Cross-Site Scripting (XSS) is an attack where hackers inject malicious scripts into a website, allowing them to steal user data such as usernames, passwords, and other information, which can damage the website's reputation and lead to its abandonment by visitors.
What is the final type of cyber attack mentioned in the script, and what is its objective?
-The final type of cyber attack mentioned is Farming, which involves redirecting users from a legitimate site to a fake one to collect visitor data, often without the victims realizing they are being targeted.
What is the first simple method suggested in the script to protect a website from hacker attacks?
-The first method suggested is to ensure regular data backups, creating a storage solution that guarantees the safety of the data even if the hosting service provides automatic backups.
What is SSL, and how does it help in protecting a website from data theft and enhancing its reputation?
-SSL, or Secure Socket Layer, is a security protocol that encrypts data transmission, preventing data theft, avoiding incorrect data transmission, and improving the website's reputation by increasing visitor trust.
What is the role of a firewall in protecting a website from various attacks?
-A firewall is a security system that monitors and controls all incoming and outgoing network connections, protecting data from hacker attacks by blocking unwanted content and monitoring bandwidth usage.
Why is it important to regularly update software and applications on a website, and what are the risks of not doing so?
-Regularly updating software and applications is crucial to protect the website from hackers who may exploit vulnerabilities in outdated software, potentially leading to data breaches and security compromises.
What is the recommendation for choosing a web hosting service provider to ensure website security against cyber attacks?
-It is recommended to choose a trusted web hosting service provider that guarantees website security from attacks, such as one that uses anti-DDoS systems like pipeline and load balancer, ensuring a secure and fast-access web server.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen

Transformasi Digital Bank Sentral bersama Abdurrahman - Departemen Kebijakan Sistem Pembayaran

Cybersecurity for the Internet of Things (IoT)
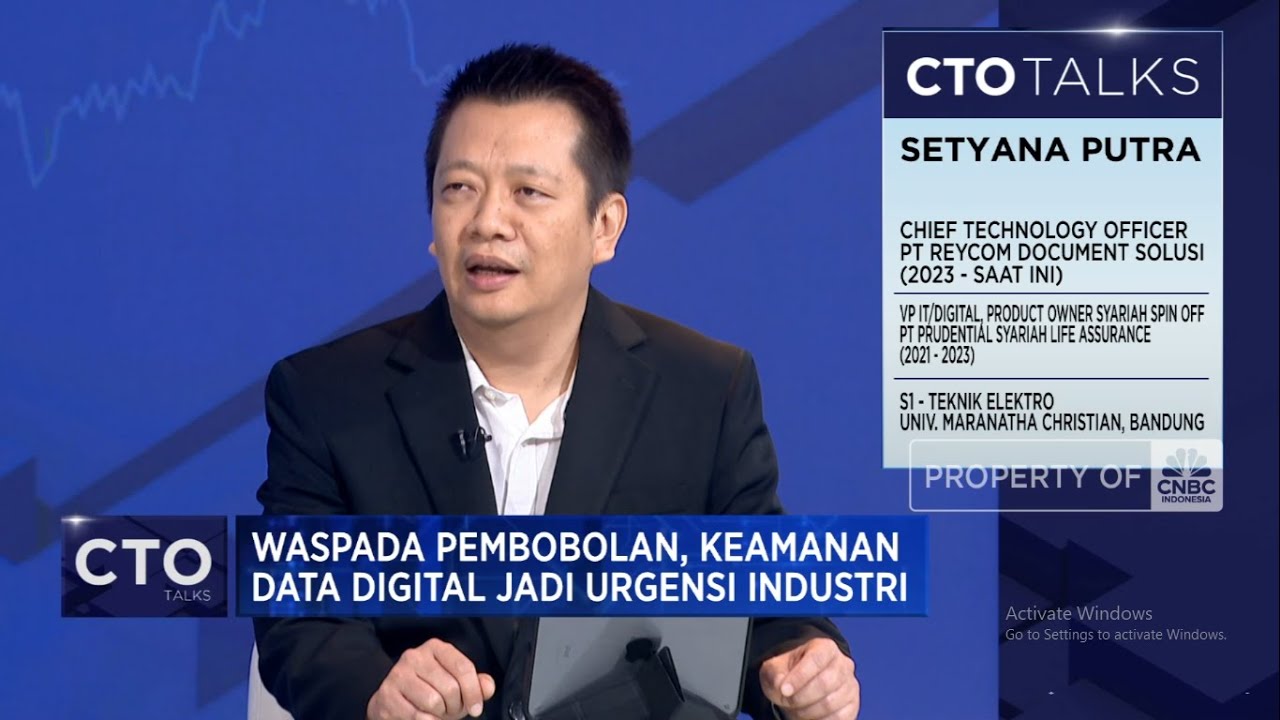
Waspada Pembobolan Keamanan Data digital Jadi Urgensi Industri

Are Hackers the Biggest Threat to America’s Critical Infrastructure?

Importância da informática do século XXI

Dampak Negatif Kemajuan Teknologi Informasi
5.0 / 5 (0 votes)
