Spring Security explained with no code
Summary
TLDRIn this educational video, the host demystifies Spring Security by drawing a relatable analogy to organizing an exclusive party. The backend or REST API is likened to the party space, with endpoints as doors and entry points managed by controllers. Spring Boot Starter Security Dependency acts as the security company, while security filters are the bouncers at each door. The video explains the authentication process using JWT tokens and the role of the security configuration class. It guides viewers through the intricacies of Spring Security without coding, making it accessible to all.
Takeaways
- 🎉 The video aims to demystify Spring Security without coding, using a party analogy to explain the concept.
- 🏠 The 'party space' in the analogy represents the backend or REST API, which is the core area of the application.
- 🚪 'Doors and entry points' in the party are likened to endpoints in a Spring application, controlled by party controllers.
- 🛂 The 'security team' or 'bouncers' are equivalent to the security filters in Spring Security, ensuring only authorized access.
- 🎫 The 'party ticket' is analogous to a JWT token in Spring Security, used to authenticate and authorize users.
- 🔐 The 'security company' hired for the party represents the Spring Boot Starter Security dependency, providing a base for security setup.
- 🛠️ Custom security configurations are made by assigning 'security guys' to each door, similar to configuring security filters for each endpoint.
- 🔗 The 'authentication controller' is where users get their 'digital tickets', paralleling the process of obtaining JWT tokens.
- 🔑 The 'user details service' and 'password encoder' are crucial for verifying user credentials and are part of the Dow authentication provider.
- 🔄 The 'security context holder' updates with each request, maintaining stateless session management as per the security contract.
Q & A
What is the main focus of the video?
-The main focus of the video is to explain the architecture of Spring Security without writing any code, using a party analogy to make it more understandable.
What is the role of the 'party space' in the Spring Security analogy?
-In the analogy, the 'party space' represents the backend or REST API, which is the core area where all the application's functionalities are centralized.
What does the term 'end points' refer to in the context of the video?
-In the video, 'end points' are likened to the doors and entry points of a party space, which in the context of a Spring application, are the API endpoints controlled by the party controllers.
What is the function of the 'security team' in the video's analogy?
-The 'security team' in the analogy represents the bouncers at a party, which in Spring Security terms, are the security filters that check if guests (users) are authorized to enter the system.
What is the digital equivalent of a party ticket in the Spring Security context?
-In the Spring Security context, the digital equivalent of a party ticket is a JWT (JSON Web Token), which users present as proof of authentication.
What does the 'spring boot starter security' dependency represent in the analogy?
-The 'spring boot starter security' dependency is compared to hiring a security company for the party, which comes with its own standard procedures but can be customized to fit specific security needs.
How does the video explain the role of the 'security filters' in Spring Security?
-The video explains that security filters are like security guards at each door of a party, responsible for checking if the JWT token is valid, correctly formatted, and issued by the system.
What is the purpose of the 'authentication controller' in the Spring Security setup?
-The 'authentication controller' is where users receive their digital tickets (JWT tokens), serving as the registration method for guests to gain access to the party (Spring application).
What is the significance of the 'security configuration class' in the video?
-The 'security configuration class' is where the Spring application's security requirements are defined, similar to a meeting with a security company to outline how the party should be secured.
How does the video describe the process of authenticating a user in Spring Security?
-The video describes the authentication process as a series of checks starting from the user's request, through the filter chain, to the authentication manager, and finally updating the security context holder if the authentication is successful.
What are the three exceptions that the video mentions during the authentication process?
-The three exceptions mentioned during the authentication process are DisabledException, LockedException, and BadCredentialsException, which correspond to different authentication errors.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen

AWS Security Tools Shield, WAF, GuardDuty, Inspector - How they work

Kalimat Perbandingan dan Kalimat Analogi
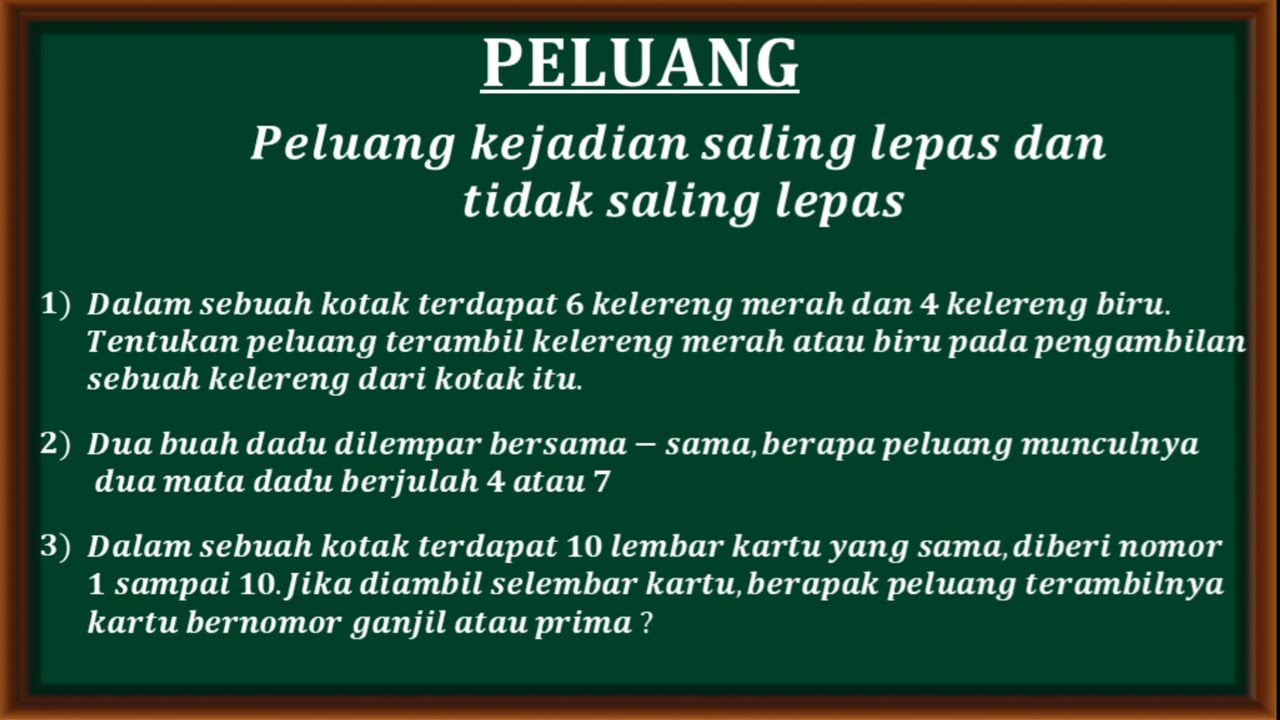
PELUANG - Kejadian saling lepas dan tidak saling lepas

#1 What is Spring Framework?

What is dependency injection in spring [ Getting started ] | Spring framework tutorial for beginners

#8 Spring without Boot
5.0 / 5 (0 votes)
