Why is JWT popular?
Summary
TLDRIn this video, Sahn, co-author of system design interview books, explains the power and risks of JSON Web Tokens (JWTs) in web security. JWTs are widely used for secure information transmission between parties, utilizing a three-part structure: header, payload, and signature. The video covers signing algorithms, claims, and best practices for secure implementation. It also highlights potential vulnerabilities, such as token hijacking and cryptographic weaknesses. While JWTs offer portability and scalability, they can pose risks if not used carefully. Key security tips and JWT use cases in authentication and authorization are discussed.
Takeaways
- 🔒 JSON Web Tokens (JWTs) securely transmit identity over the web, but a stolen JWT can give hackers full access.
- 🧑💻 JWTs consist of three parts: the header, payload, and signature, each base64 encoded and separated by a period.
- 📋 The payload stores claims, which are statements about a user or entity. Claims can be registered, public, or private.
- 🔐 JWTs are usually signed, not encrypted, meaning that while the data is encoded, it can still be read if intercepted.
- 🛡️ There are two main signing algorithms: symmetric (HMAC SHA256) and asymmetric (RSA), each with different security trade-offs.
- 🚫 JWT payloads should never contain sensitive information unless encrypted, as they are not encrypted by default.
- ⏳ JWTs are stateless and not ideal for managing user sessions, as revoking tokens can be difficult.
- ⚠️ Common JWT vulnerabilities include token hijacking and weak cryptographic algorithms, which can be exploited.
- ✔️ Best practices for JWTs include keeping payloads small, using short expiration times, and securing tokens properly.
- 📈 JWTs offer scalability for authentication and authorization, but they can be vulnerable if not implemented securely.
Q & A
What is a JSON Web Token (JWT)?
-A JSON Web Token (JWT) is a secure method for transmitting information between parties as JSON objects. It is widely used in web security for its ability to securely authenticate and authorize users.
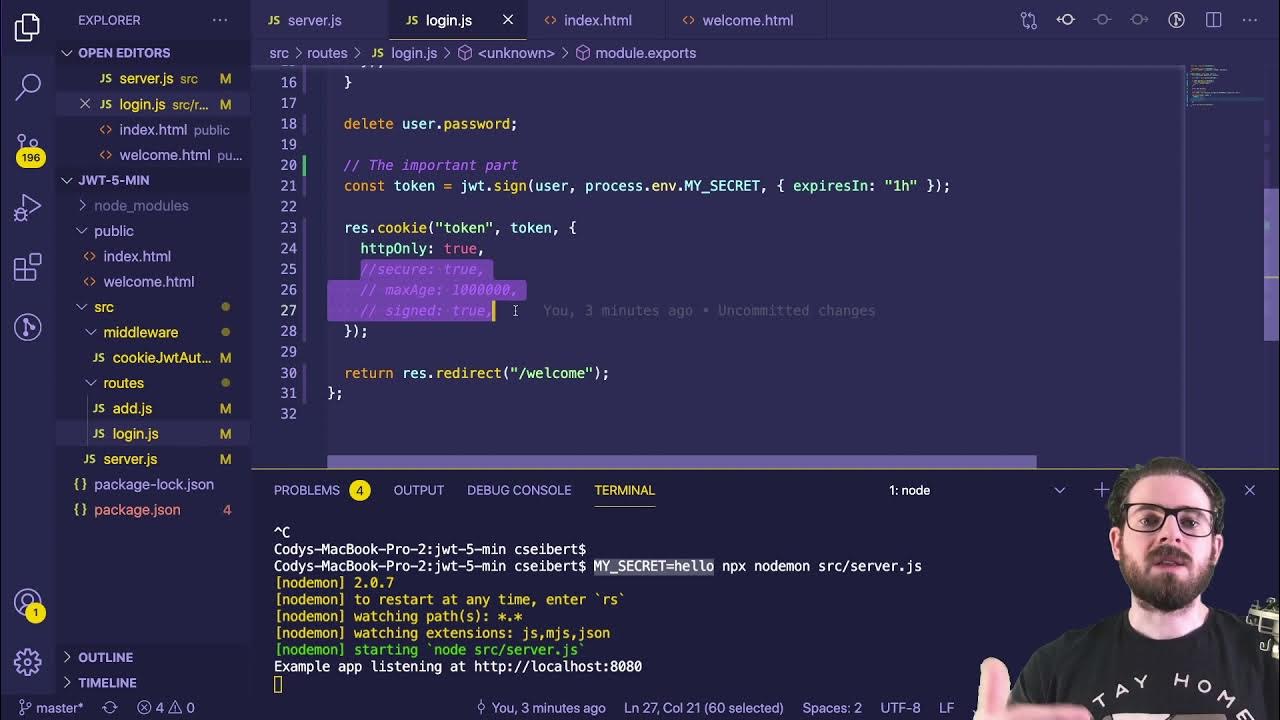
How is a JWT structured?
-A JWT consists of three parts: the header, the payload, and the signature. Each part is base64 encoded and separated by a period.
What information is typically included in the JWT header?
-The JWT header usually contains the token type (JWT) and the algorithm used for signing, such as HMAC SHA256 or RSA.
What is the purpose of the JWT payload?
-The payload of a JWT contains claims, which are statements about an entity (usually the user) along with additional data. Claims can be registered, public, or private.
Why should sensitive information not be included in a JWT payload?
-Since JWTs are usually only signed and not encrypted, the payload can be read if intercepted. Therefore, sensitive information should not be included unless the payload is encrypted.
What are the two main types of JWT signing algorithms?
-JWTs can be signed using symmetric algorithms, like HMAC SHA256, which use a shared secret key for both signing and verification. Alternatively, they can use asymmetric algorithms, like RSA, which use a public/private key pair.
What are some of the key advantages of using JWTs?
-JWTs are self-contained and portable, making them useful for secure information exchange without requiring server-side storage. They are commonly used for authentication and authorization in standards like OAuth2 and OpenID Connect.
What are some of the key risks and vulnerabilities associated with JWTs?
-JWTs can be vulnerable to token hijacking, where attackers steal a JWT to impersonate a user. They can also be exposed to cryptographic weaknesses, especially if weak hashing algorithms are used.
What are some best practices for securely using JWTs?
-Best practices include keeping JWT payloads compact, using short expiration times, storing tokens securely, invalidating leaked tokens, and using strong signature algorithms.
When should JWTs not be used?
-JWTs should not be used when handling highly sensitive data unless encryption is applied. They are also not ideal for managing user sessions due to their stateless nature, making session revocation difficult.
Outlines

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنMindmap

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنKeywords

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنHighlights

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنTranscripts

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنتصفح المزيد من مقاطع الفيديو ذات الصلة
5.0 / 5 (0 votes)