Session vs Token Authentication in 100 Seconds
Summary
TLDRThis video discusses two main approaches to user authentication: server-side sessions and token-based authentication. Sessions store user data on the server, creating potential vulnerabilities like cross-site request forgery and bottlenecks in distributed systems. Token-based authentication, using JSON Web Tokens (JWT), avoids server storage by keeping tokens client-side, which improves scalability but introduces its own risks, such as token hijacking and difficulties in invalidation. The video concludes by highlighting a 12-week web security coaching program, focusing on modern security practices.
Takeaways
- 🔐 Cookie-based sessions involve storing session IDs on the server, and the session ID is stored in the browser's cookie jar.
- ⚠️ Cross-Site Request Forgery (CSRF) can occur in session-based authentication but is generally mitigated in modern frameworks.
- 📉 A major drawback of session-based authentication is the need to store session IDs in a database or memory, which can be a bottleneck in horizontally scaled cloud systems.
- 🔄 Token-based authentication, like JSON Web Tokens (JWTs), eliminates the need for storing session IDs on the server.
- 🗝️ JWTs are created with a private key on the server and stored in the browser's local storage for client-side management.
- 🚀 JWTs make it more efficient to handle distributed cloud systems as there's no need for a database lookup.
- ⚠️ Tokens can still be vulnerable to hijacking and may be difficult to invalidate after being issued.
- 💡 A key difference between sessions and tokens: sessions are managed server-side, while tokens are managed client-side.
- 🧩 Tokens can't be used for background authentication on the server, limiting some functionalities.
- 📚 The script promotes a web security academy and a 12-week coaching program for mastering web security, including a module on Firebase security.
Q & A
What is the traditional approach to user authentication on the web?
-The traditional approach is cookie-based, server-side sessions. The server validates the user's credentials, creates a session in the database, and sends a session ID to the browser, which is stored in the browser's cookie jar.
How does the session ID function in subsequent requests?
-The session ID stored in the browser's cookie jar is sent back to the server with each subsequent request, allowing the server to respond with content tailored to the authenticated user.
What are some drawbacks of session-based authentication?
-Drawbacks include vulnerability to cross-site request forgery (CSRF) attacks and the need to store session IDs in a database or in server memory, which can become a bottleneck when scaling cloud applications horizontally.
What is cross-site request forgery (CSRF) and how does it affect session-based authentication?
-CSRF is an attack where an attacker tricks the user into performing actions on a site they're logged into, such as making payments or changing passwords. Although the risk is low with modern frameworks, it remains a potential issue for session-based authentication.
How does token-based authentication solve the problem of horizontal scaling in cloud applications?
-Token-based authentication eliminates the need for database lookups by generating a JSON Web Token (JWT) after login, which is stored in the browser and sent in the authorization header for future requests. The server only needs to validate the JWT signature, reducing the need for database interactions.
What is a JSON Web Token (JWT), and how is it used in token-based authentication?
-A JWT is a token created with a private key on the server, which is sent to the browser after login. It is stored in local storage or cookies and sent with each request in the authorization header. The server validates the token to authenticate the user.
What are the potential risks of using token-based authentication?
-Tokens can still be hijacked by attackers, and they can be difficult to invalidate once issued. Additionally, tokens can't be used to authenticate a user in the background on the server.
What is the key difference between session-based and token-based authentication?
-The key difference is that in session-based authentication, the authentication state is managed on the server, whereas in token-based authentication, the state is managed on the client.
Why is token-based authentication considered more efficient in distributed cloud systems?
-Token-based authentication is more efficient because the server only needs to validate the JWT's signature, removing the need for database lookups and allowing better performance in horizontally scaled systems.
What is a key challenge of token-based authentication in terms of token management?
-One of the challenges is that tokens are difficult to invalidate once they have been issued, posing a risk if they are compromised.
Outlines

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифMindmap

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифKeywords

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифHighlights

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифTranscripts

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифПосмотреть больше похожих видео
JWT Authentication with Node.js, React, MySQL | Node JS Authentication With JSON Web Token

How I Handle Authentication in My Chrome Extension

Retina Scanner Fingerprints and Biometric Sign In
The Wrong Way to Handle Authentication in React (Code Review)

#37 Spring Security | Generating JWT Token
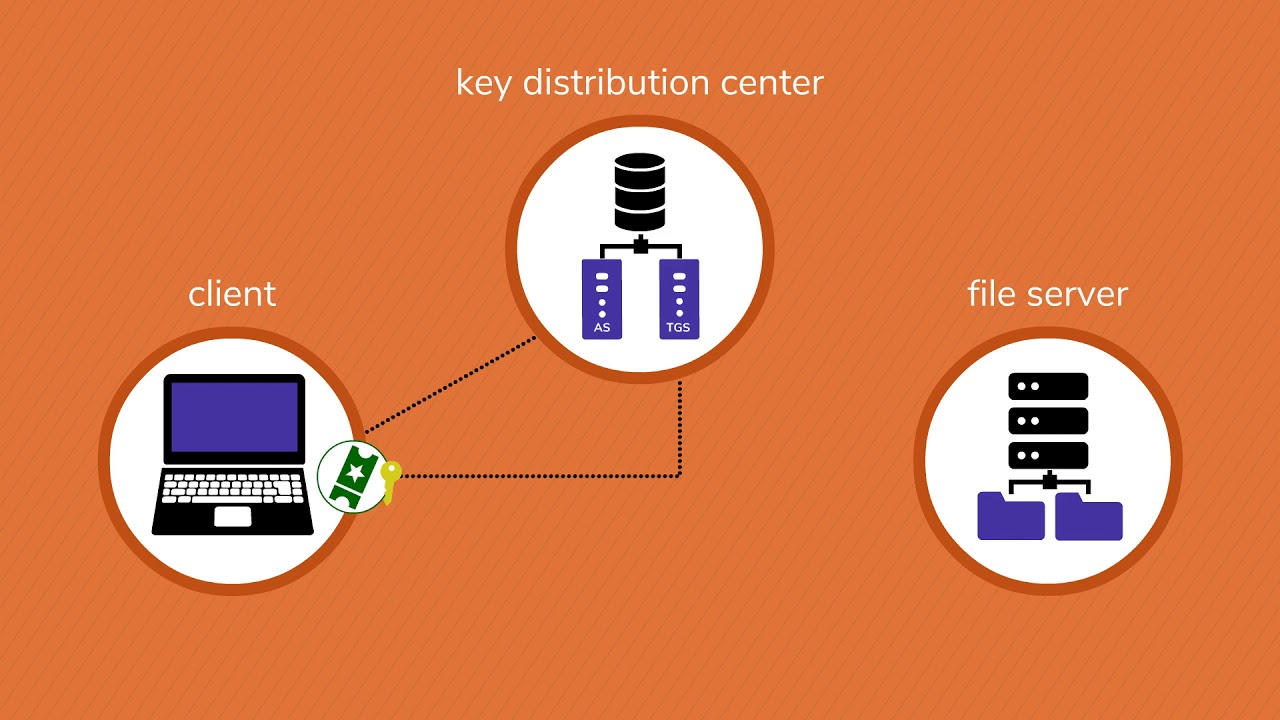
How Kerberos Works
5.0 / 5 (0 votes)
