"Hack ANY Cell Phone" - Hacker Shows How Easy It Is To Hack Your Cell Phone
Summary
TLDRIn this podcast, cybersecurity expert Ryan Montgomery, known as zero day, showcases various hacking tools, including a Wi-Fi-enabled charging cable that can emulate a keyboard and type at 860 characters per second, potentially for malicious use. He also introduces a 'data blocker' device to prevent such attacks, emphasizing the need for vigilance against cyber threats. Montgomery discusses the balance between ethical hacking for security testing and unethical hacking for criminal activities, highlighting the importance of protecting personal data.
Takeaways
- 🔍 The speaker discusses various hacking tools and their potential uses, both ethical and malicious.
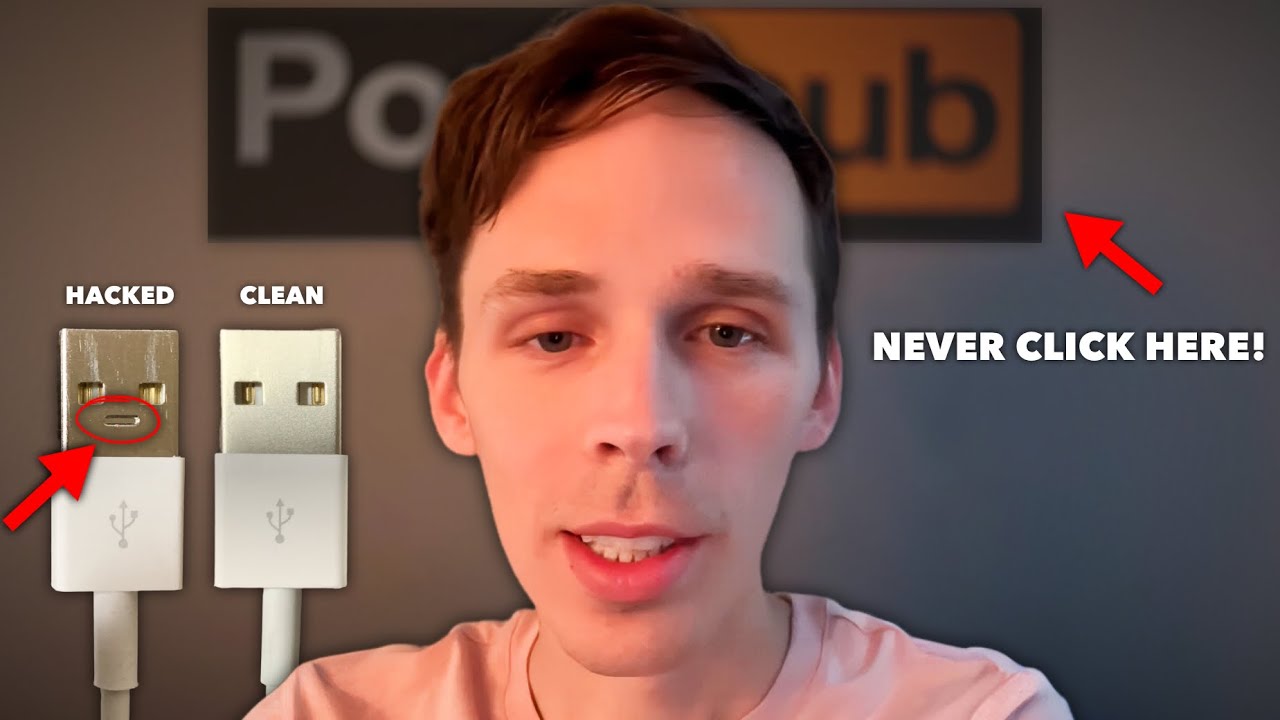
- 📱 A 'charger' device is revealed to have a hidden Wi-Fi chip and keyboard emulation capabilities, allowing for rapid keystroke injection.
- 💸 The NSA is mentioned to have sold similar devices for $20,000, but they are now available at a fraction of the cost.
- 🛡️ Data blockers are introduced as a protective measure against malicious charging devices, limiting them to charging only.
- 🖥️ A device that can capture and transmit screen activity wirelessly is demonstrated, highlighting the risk of unauthorized surveillance.
- 💾 The use of SD cards in surveillance devices for storing data is mentioned, showing how data can be retrieved later.
- 🔑 The importance of physical security checks, such as inspecting behind computer monitors for hidden devices, is emphasized.
- 🤝 The speaker shares a personal philosophy on privacy and trust in relationships, suggesting trust is more important than surveillance.
- 💰 The range of prices for different security and hacking tools is discussed, from affordable to high-end enterprise solutions.
- 👮♂️ The script concludes with a call to action for viewers to seek help with cyber security and child safety, offering assistance.
Q & A
What is the purpose of the orange tag on the charger mentioned in the script?
-The orange tag is used to distinguish the charger from a regular one, as it actually contains a Wi-Fi chip and a mini computer that can emulate a keyboard, making it look like a regular charger but with hidden functionalities.
What is the speed at which the hidden device in the charger can type?
-The device can type at 860 characters per second.
What is the original price of the NSA's version of the cable mentioned in the script?
-The NSA's version of the cable is priced at $20,000.
What is the function of the device that can be plugged into a phone or computer?
-The device can monitor keystrokes, inject keystrokes, and potentially install malware or viruses, providing remote control over the connected device.
How can one protect themselves from malicious USB devices like the one described?
-One can use a data blocker, which only allows the device to charge and not perform any other functions, thus preventing any potential malicious activities.
What is the name of the device that creates a Wi-Fi network and can be used for penetration testing?
-The device is referred to as 'OMG cable' in the script, and it is used for ethical hacking purposes such as penetration testing.
What is the price range for the most expensive tool mentioned in the script?
-The most expensive tool mentioned is the cellebrite, with a price range from $20,000 to $50,000.
What is the purpose of the 'Unblocker' device mentioned in the script?
-The 'Unblocker' is a data blocker that not only prevents malicious attacks but also has the capability to perform the same actions as the malicious devices it protects against, for demonstration or testing purposes.
What is the role of the 'Malicious Cable Detector' in the context of the script?
-The 'Malicious Cable Detector' is a device that can be plugged into a system to identify if a connected cable is malicious or not, providing an extra layer of security.
What is the function of the device that can be hidden behind a computer monitor?
-The device hidden behind a computer monitor can wirelessly transmit or store what's displayed on the screen, potentially capturing sensitive information without the user's knowledge.
What advice does Ryan Montgomery give regarding relationships and privacy in the script?
-Ryan Montgomery advises against invading privacy in relationships, stating that trust is important and that if someone is going to cheat, they will do so regardless of any monitoring.
Outlines

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифMindmap

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифKeywords

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифHighlights

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифTranscripts

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифПосмотреть больше похожих видео

20 Powerful Dangerous Hacking Gadgets in 2024 #hacker #gadgets

Ethical Hacker: "100% your phone is hacked!"
Ethical Hacker Warns: Check Your Charger ASAP & What Happens After Clicking Adult Sites

If You’ve Clicked on a P*RN Video… YOU’VE BEEN HACKED

Never plug this in!

ieee 802 introduction / wireless network technology/smarter daybyday
5.0 / 5 (0 votes)
