If You’ve Clicked on a P*RN Video… YOU’VE BEEN HACKED
Summary
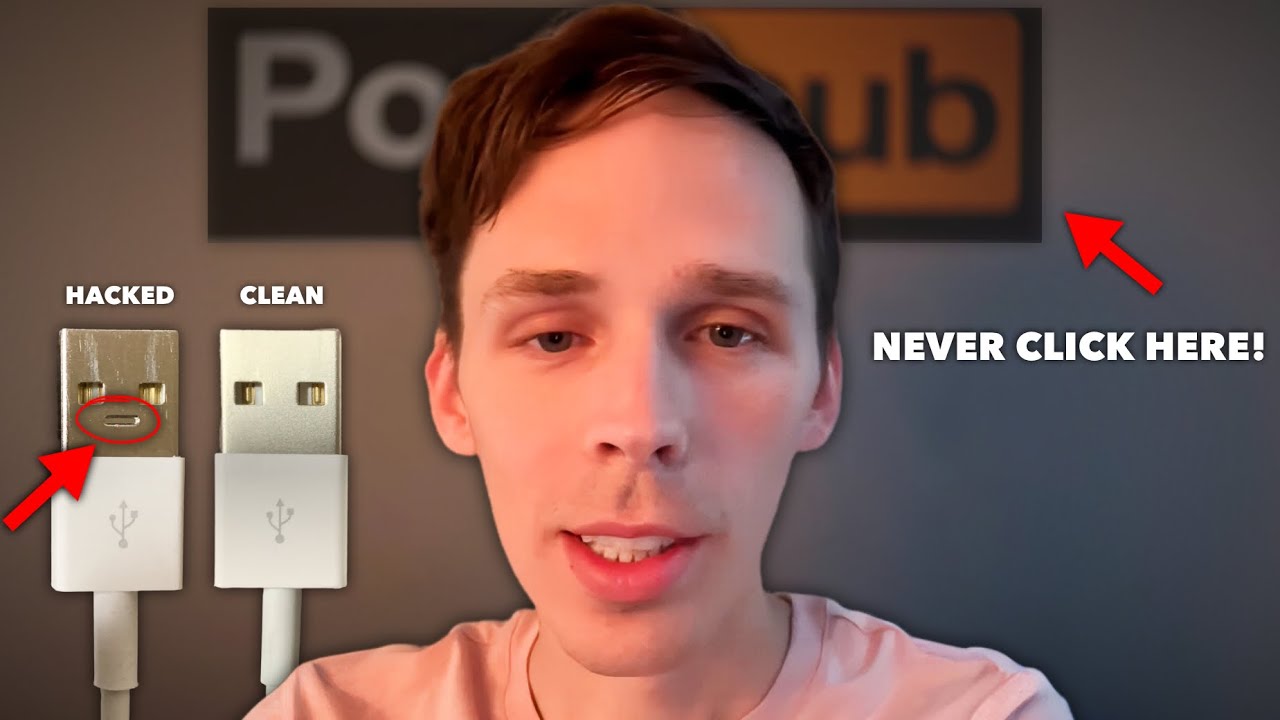
TLDRIn this eye-opening discussion led by renowned white hat hacker Ryan Montgomery and featuring insights from the late John McAfee, the video reveals alarming truths about cybersecurity vulnerabilities. Montgomery demonstrates a seemingly innocuous USB charger that can monitor keystrokes and create a Wi-Fi network, highlighting the risks of public charging stations. McAfee elaborates on how adult websites often deploy keystroke logging software, posing severe threats to smartphone security. The conversation emphasizes the urgent need for awareness regarding digital privacy and the implications of our online activities, urging viewers to reconsider their habits and approach to technology.
Takeaways
- 🔌 Be cautious of public charging stations; they may harbor devices that can compromise your security.
- 💻 White hat hacker Ryan Montgomery discusses how common USB chargers can be modified to monitor keystrokes.
- 📱 John McAfee highlights that many smartphones are infected with keystroke logging software, especially those visiting adult websites.
- 🚨 Many free adult websites monetize user interactions, which can lead to hidden malware and privacy breaches.
- ⚠️ McAfee warns that clicking on adult content can expose users to malicious software that compromises their devices.
- 🕵️♂️ Cybersecurity threats are pervasive, with studies showing that devices accessing adult content face triple the risk of malware.
- 🔍 Hacking can be alarmingly easy; John McAfee explains how any device can be hacked in under 30 minutes.
- 🤖 Our devices are often designed to monitor us, raising concerns about privacy and surveillance.
- 🖥️ The FBI's request for backdoors in devices poses risks, as any vulnerabilities can be exploited by hackers.
- 🌍 Awareness of cyber threats is crucial; users must understand both the capabilities and vulnerabilities of their devices.
Q & A
What is the main concern raised by the white hat hacker Ryan Montgomery regarding charging devices?
-Ryan Montgomery highlights the risks associated with using seemingly innocuous USB chargers that can secretly monitor keystrokes and access personal data. He warns that such devices can create their own Wi-Fi networks to control and exploit connected devices.
Why does Montgomery claim that the NSA sells certain USB devices for $20,000?
-Montgomery suggests that the complexity and capability of these USB devices, which can monitor and manipulate data, justify their high price tag. These devices can pose significant security threats, making them valuable tools for malicious actors.
What did John McAfee reveal about the risks associated with adult film websites?
-John McAfee claims that over half of smartphones are infected with keystroke logging software, especially for users visiting adult film sites. This software can record users' keystrokes and monitor their activities, leading to severe privacy invasions.
How do pornography sites monetize users' interactions according to McAfee?
-McAfee explains that pornography sites often run scripts that download unauthorized applications onto users' devices when they visit. This allows hackers to access sensitive data and monitor users without their consent.
What is the implication of the FBI's request to Apple regarding security checks?
-The FBI's request to alter Apple's software to bypass security checks raises concerns about potential misuse. If such backdoors are created, they could be exploited on any device, compromising user privacy and security.
What does McAfee mean by stating that all smartphones are essentially computers?
-McAfee emphasizes that smartphones have processors, operating systems, and memory, similar to traditional computers. This means they are susceptible to hacking and malware, underscoring the importance of securing these devices.
What steps does McAfee outline for how hackers can easily access smartphones?
-McAfee outlines a simple process where a hardware engineer disassembles the phone to copy its instruction set, followed by a coder who can identify vulnerabilities in just half an hour, making it alarmingly easy for hackers to gain control.
What psychological impact does the speaker suggest smartphones have on users?
-The speaker suggests that smartphones act as 'black mirrors' that can distract users, reduce focus, and even draw them into negative behaviors or mindsets. This metaphor indicates a broader concern about technology's influence on mental well-being.
What does the speaker suggest individuals do to protect themselves from these vulnerabilities?
-The speaker encourages individuals to avoid clicking on questionable websites and to seek sincere forgiveness if they have engaged with harmful content, asserting that a connection to faith can offer protection and peace of mind.
How does the transcript frame the relationship between technology and personal privacy?
-The transcript portrays technology as a double-edged sword, where the convenience of devices comes with significant risks to personal privacy. It stresses the need for awareness and caution when using technology, especially in relation to personal data security.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video
Ethical Hacker Warns: Check Your Charger ASAP & What Happens After Clicking Adult Sites

Ethical Hacker: "100% your phone is hacked!"

On a reçu le hacker qui rend fou la CIA (nous tuez pas svp)

CYBER SECURITY BASICS - VIDEO 1 | ZERO TO HERO | TAMIL #learncybersecurity #youtubetech #tamiltech

Every Hidden Hackers Explained
What Is Ethical Hacking? | Ethical Hacking In 8 Minutes | Ethical Hacking Explanation | Simplilearn
5.0 / 5 (0 votes)