11 Directory Bruteforce
Summary
TLDRThe video script discusses the concept of directory brute force attacks, a technique used to uncover hidden pages and content on web applications. It emphasizes the importance of the wordlist used in the attack, as a larger list can potentially reveal more content. The script introduces tools like DirBuster, First Search, and Gobuster for performing directory brute force. The tutorial demonstrates setting up a web server with a predefined content and using the DirBuster tool to attempt brute force on a web application. It explains the command-line usage of DirBuster to target specific file extensions, such as .php, and concludes with the results of the brute force attempt, showcasing discovered content.
Takeaways
- 😀 The video discusses a technique called 'directory bruteforce', which is an attack aimed at discovering hidden pages and content on a web application.
- 🔍 The success of a directory bruteforce attack depends on the list of words, or 'wordlist', used, with a larger list potentially revealing more web content.
- 🛠️ The video mentions several tools that can be used for directory bruteforcing, including DirBuster, First Search, and Gobuster.
- 💻 The tutorial is conducted using Kali Linux, which is a pre-configured environment for such attacks, with a web application already provided for practice.
- 📁 The presenter demonstrates how to use the web application by dragging and dropping it into the Kali Linux environment.
- 🔑 The video shows the process of starting a web server with content that has been previously copied, accessible via a specific port.
- 🌐 The presenter tests the web server by accessing it through a browser, using 'localhost' and the specified port number.
- 🔧 The tutorial then moves on to performing a bruteforce attack, starting with opening a new terminal for the purpose.
- 🔎 The DirBuster tool is highlighted for its ease of use, and the video explains how to run it with specific parameters to filter for certain file extensions, such as '.php'.
- 📝 The DirBuster tool is run with a command that includes the target web server's address and the desired file extension, aiming to find hidden '.php' files.
- 📊 After the bruteforce process, the tool will display the content found, listing any discovered pages or files from the target web address.
- 👋 The video concludes with a summary of the bruteforce method using one of the tools in Kali Linux and an invitation to the next video.
Q & A
What is the main topic of the video script?
-The main topic of the video script is about discussing and demonstrating directory brute-force attacks on web applications.
What is a directory brute-force attack?
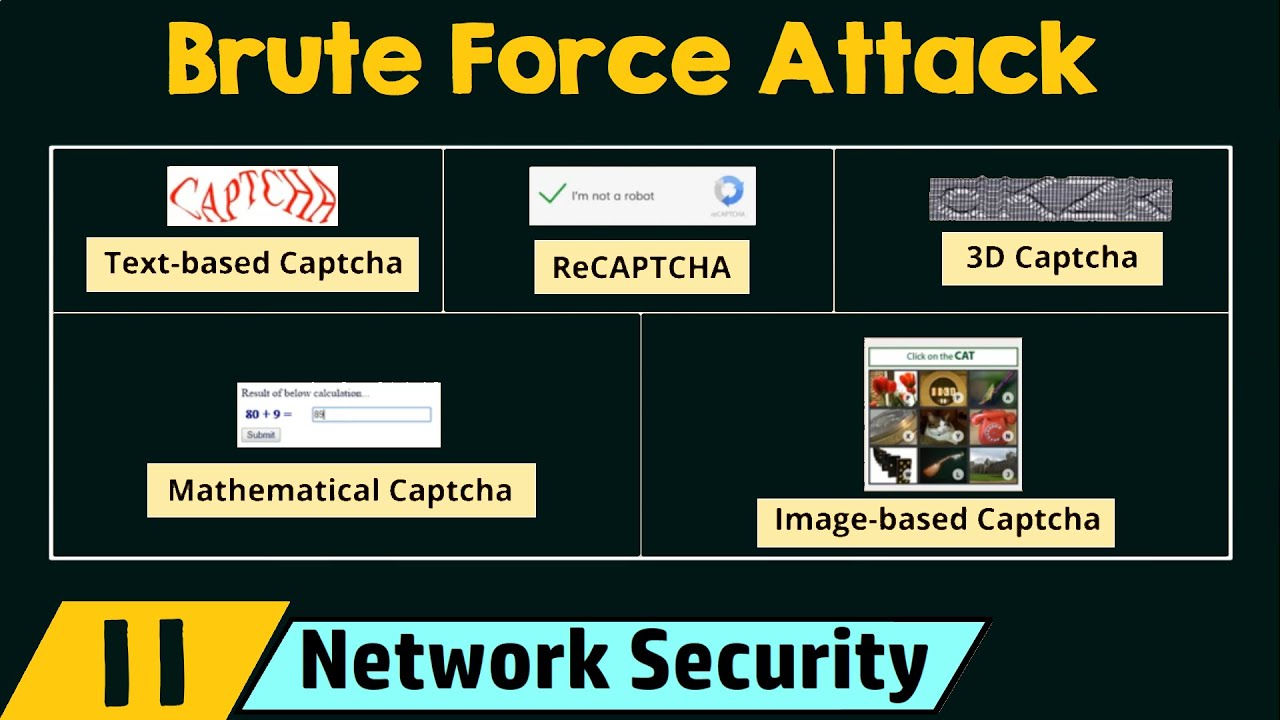
-A directory brute-force attack is a technique where an attacker uses a list of words or phrases to attempt to find hidden pages and content on a web application.
What are the tools mentioned in the script that can be used for directory brute-force attacks?
-The tools mentioned in the script for directory brute-force attacks are dirb, TheHarvester, and Gobuster.
What is the significance of the wordlist in a brute-force attack?
-The wordlist is crucial in a brute-force attack as the success of discovering hidden content on a web application depends on the number of words in the list. The more words in the list, the higher the chance of finding hidden content.
What is the role of Kali Linux in the demonstration provided in the script?
-Kali Linux is used as the platform to run the brute-force attack. It is pre-configured with the necessary tools and web application for the demonstration.
How is the web application prepared for the demonstration in the script?
-The web application for the demonstration is prepared by copying its content into the Kali Linux environment, which can then be accessed and manipulated during the attack.
What is the purpose of running a web server in the context of the script?
-The purpose of running a web server in the script is to host the content that will be targeted by the brute-force attack, simulating a real-world scenario.
What command is used to start the web server in the script?
-The command used to start the web server in the script is 'python -m http.server' with a specified port, such as 8000.
How does the script differentiate between the initial terminal and the one used for the brute-force attack?
-The script differentiates by using 'Ctrl + Alt + T' to open a new terminal for the brute-force attack, while the initial terminal is used to run the web server service.
What is the command used to run the brute-force attack with the tool dirb in the script?
-The command used to run the brute-force attack with dirb in the script is 'dirb http://localhost:port -X .php', where 'localhost:port' is the address of the web server and '-X .php' specifies the file extension to target.
What does the script suggest will be the outcome of a successful brute-force attack?
-A successful brute-force attack will result in the discovery of hidden content, such as index.php, login.php, register.php, and other files, which will be displayed after the attack is completed.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenant5.0 / 5 (0 votes)