What is DNSSEC (Domain Name System Security Extensions)?
Summary
TLDRThis video explains the importance of DNSSEC (DNS Security Extensions) in preventing attacks where users are redirected to malicious websites. It describes how DNSSEC ensures origin authentication, data integrity, and authenticated denial of existence using public key cryptography. The video details key record types like the DNS Key, ZSK (Zone Signing Key), KSK (Key Signing Key), and NSEC, explaining how they work together to validate DNS responses. Finally, the video guides users on implementing DNSSEC by signing the zone, testing for errors, and setting up a DS record with a registrar.
Takeaways
- 🔒 DNSSEC (DNS Security) is essential for securing DNS queries by ensuring users reach legitimate websites.
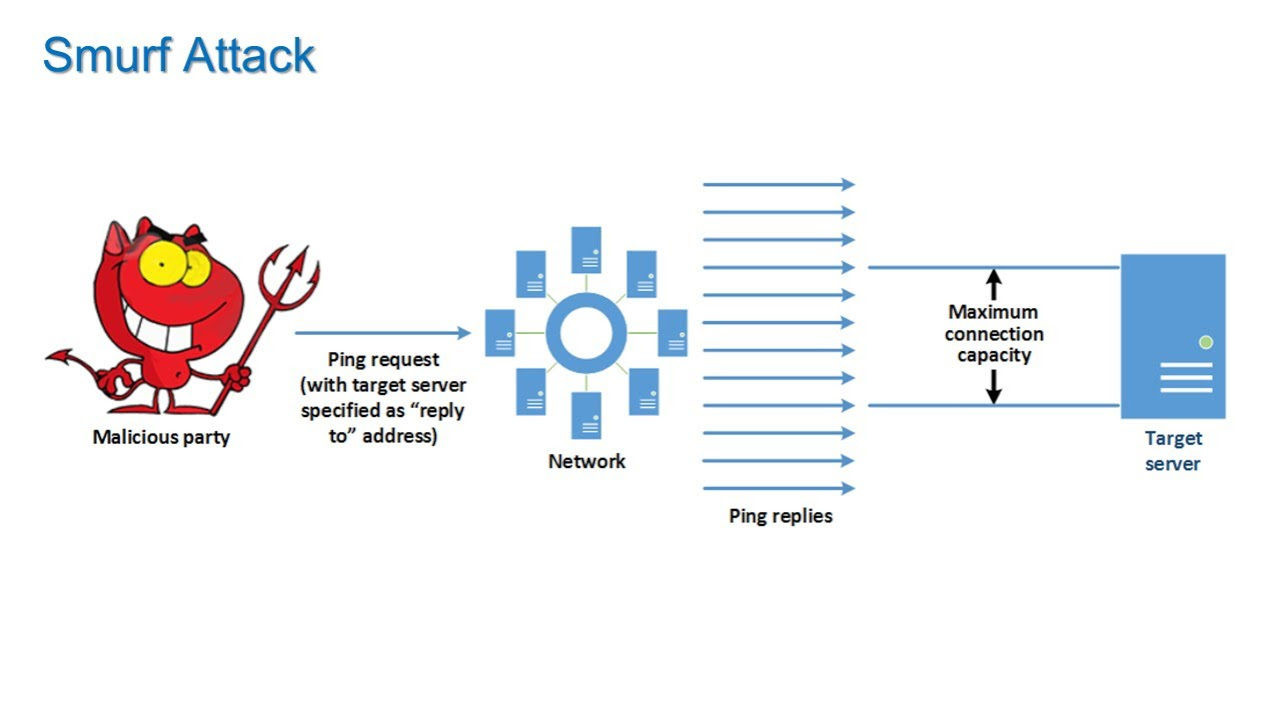
- 💻 Attackers can reroute DNS traffic to malicious servers, leading to credential theft and other malicious activities.
- ✅ DNSSEC provides three key protections: origin authentication, data integrity, and authenticated denial of existence.
- 🌐 DNSSEC verifies each step in the DNS query process, ensuring that users communicate with legitimate servers.
- 🔐 Authenticated denial of existence ensures that non-existent domain requests (e.g., foo.ibm.com) are validated and proven not to exist.
- 🔑 DNSSEC relies on public key cryptography (PKCS) using public/private key pairs to ensure trust and authenticity.
- 📝 New DNS record types introduced by DNSSEC include DNSKEY, RRSIG, KSK (Key Signing Key), ZSK (Zone Signing Key), and NSEC.
- 🔗 The chain of trust is established through delegation signer (DS) records, ensuring that each server in the query chain is legitimate.
- ⚙️ To implement DNSSEC, you need to sign your zone, test your setup, and then submit a DS record to your registrar to enable DNSSEC.
- 🛠️ Testing your DNSSEC configuration is crucial to ensuring that all keys and records are properly set up before going live.
Q & A
What is DNSSEC and why is it important?
-DNSSEC stands for DNS Security Extensions and is important because it helps prevent attacks where traffic is rerouted to malicious DNS servers. It ensures that users are connected to the correct server by providing origin authentication, data integrity, and authenticated denial of existence.
What kind of attack does DNSSEC help to prevent?
-DNSSEC helps to prevent man-in-the-middle attacks where an attacker reroutes DNS traffic to a malicious DNS server. This can lead to users being directed to fraudulent websites where their credentials and sensitive data may be stolen.
How does DNSSEC provide origin authentication?
-DNSSEC uses public key cryptography to validate the origin of DNS responses. When a DNS query is made, DNSSEC verifies that the response came from the correct, authenticated DNS server using a public-private key pair.
What are the three main functions of DNSSEC?
-The three main functions of DNSSEC are: 1) Origin authentication, 2) Data integrity checking, and 3) Authenticated denial of existence.
What is 'authenticated denial of existence' in DNSSEC?
-Authenticated denial of existence is a feature of DNSSEC that verifies when a requested DNS name doesn't exist. It ensures that the DNS server is correctly confirming the non-existence of a domain, preventing attackers from fabricating such responses.
What role does public key cryptography play in DNSSEC?
-Public key cryptography underpins DNSSEC by ensuring that DNS responses are signed with a private key and can be validated by anyone with the corresponding public key. This ensures that the response has not been tampered with and comes from a legitimate source.
What is the difference between a KSK and a ZSK in DNSSEC?
-In DNSSEC, a KSK (Key Signing Key) is used to sign the Zone Signing Key (ZSK), while the ZSK is responsible for signing the zone data itself. The KSK helps establish a chain of trust by being recognized at a higher level (TLD) and signing the ZSK.
What is an RRSIG record, and how does it relate to DNSSEC?
-An RRSIG record is used in DNSSEC to cryptographically sign DNS responses. It ensures that the response has not been altered and verifies the origin of the data.
How does DNSSEC establish a chain of trust?
-DNSSEC establishes a chain of trust through the use of DS (Delegation Signer) records at each DNS level. The DS record at one level points to the KSK at the next level, allowing DNS resolvers to verify that the DNS response is coming from an authenticated server.
What is the process for enabling DNSSEC for your domain?
-To enable DNSSEC, you first need to sign the zone by creating a ZSK, KSK, and RRSIG. Then, test the setup to ensure there are no errors. Finally, contact your registrar to add the DS record. Once the DS record is in place, DNSSEC becomes active, and DNS responses are validated.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes

What is DNS Hijacking - How to Protect Yourself?
DEF CON 32 - Sneaky Extensions The MV3 Escape Artists - Vivek Ramachandran, Shourya Pratap Singh

Which Is The Best DNS for Secure Browsing: CloudFlare, Quad9, NextDNS, and AdGuard DNS
Denial of Service and Intrusion Detection - Information Security Lesson #11 of 12

Digital Certificates Explained - How digital certificates bind owners to their public key

Module 5.5 Lab Cross Site Scripting
5.0 / 5 (0 votes)
