My new homelab Firewall is insane! // Sophos XGS 2100
Summary
TLDRThis video showcases the setup and features of the Sophos XG 2100, a next-generation firewall, in a home server rack. The presenter highlights its deep packet inspection for malware detection, management of two new Surface access points, and the ease of network management it provides. The video also discusses the importance of network separation for security, setting up firewall rules, and managing Wi-Fi access points through the Sophos interface. It concludes with a teaser for upcoming content and a recommendation for viewers interested in home lab security solutions.
Takeaways
- 🔒 The video introduces the Sophos XG 2100, a next-generation firewall designed to secure home networks by managing and protecting devices.
- 🏠 The firewall connects all devices in the home network and is equipped with deep packet inspection to detect exploits and malware.
- 📡 Two new Surface Access Points are added to enhance the home Wi-Fi, managed entirely by the firewall for streamlined network management.
- 🔧 The user shared a Twitter poll indicating that many people are considering firewall solutions for their home labs, suggesting a growing interest in home network security.
- 📦 The unboxing segment reveals the contents of the Sophos XG 2100 package, including a getting started guide and an Ethernet cable.
- 🚀 The Sophos XG 2100 is part of the latest series of Sophos XG appliances and is the smallest rackmount model with eight gigabit Ethernet ports and two SFP plus modules.
- 💡 The user plans to upgrade the network speed with a 4x SFP plus Flexi Port Module for 10 gigabit connectivity, showcasing a step-up in network performance.
- 🛠️ The video provides a detailed walkthrough of setting up the firewall, including configuring general settings, licensing, and firmware updates.
- 🌐 The user demonstrates how to create layer 2 bridge interfaces and bind ports for different network zones, emphasizing the importance of network segmentation for security.
- 🔄 The Sophos XG firewall's advanced features include intrusion prevention system (IPS) engines, malware detection, and traffic prioritization, enhancing the home network's security posture.
- 🛡️ The video concludes with a discussion on the importance of firewall rules for controlling traffic and protecting critical services within the home network.
Q & A
What is the Sophos XGS 2100?
-The Sophos XGS 2100 is a next-generation firewall that connects and protects network devices, scans traffic for exploits and malware through deep packet inspection, and manages wireless access points.
What are the key features of the Sophos XGS 2100?
-Key features include eight gigabit Ethernet ports that are fully programmable, two SFP plus modules supporting one gigabit, and the capability to manage wireless access points directly from the firewall.
What additional hardware is required for the Sophos XGS 2100 to support 10 gigabit?
-A four-part SFP plus flexi port module is required to extend the capabilities and support 10 gigabit connections.
How does the Sophos XGS 2100 manage wireless access points?
-The firewall can manage access points directly, allowing for centralized configuration of settings such as SSID, password, and Wi-Fi channels through the Sophos X2U wireless dashboard.
What is the purpose of the layer 2 bridge interface created in the setup?
-The layer 2 bridge interface is created to bind specific ports together, allowing them to be part of the same local network and facilitating the configuration of firewall rules and traffic control.
How does the Sophos XGS 2100 differentiate between different network zones?
-The firewall uses different zones such as LAN and DMZ to control and isolate traffic. It allows the creation of specific firewall rules to manage which services and IP addresses can be accessed within each zone.
What is the advantage of using the physical Sophos XGS 2100 appliance over a virtual machine?
-The physical appliance is optimized for computing tasks and can accelerate and offload traffic more efficiently than a virtual machine, especially when multiple scanning engines are enabled.
How does the Sophos XGS 2100 protect against exploits and malware?
-It includes various scanning engines that can detect and block malicious patterns, exploits, and malware, with capabilities like sandboxing and artificial intelligence.
What is the significance of the firewall rules created in the Sophos XGS 2100 setup?
-Firewall rules define the traffic flow and access permissions within the network, ensuring that only authorized and authenticated users can access specific services and servers.
How does the Sophos XGS 2100 handle unauthorized access to services running on home servers?
-The firewall can be configured to allow unauthorized access to specific services and workloads on home servers by creating rules that permit access to certain IP addresses and ports, while still maintaining security controls.
Outlines

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantMindmap

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantKeywords

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantHighlights

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantTranscripts

Cette section est réservée aux utilisateurs payants. Améliorez votre compte pour accéder à cette section.
Améliorer maintenantVoir Plus de Vidéos Connexes
Opnsense Firewall Installation - Virtual Lab Building Series: Ep2

Everything I Learned About Home Networking - A Newbie’s Perspective
How to install an FTP Server on Ubuntu 22.04 with VSFTPD
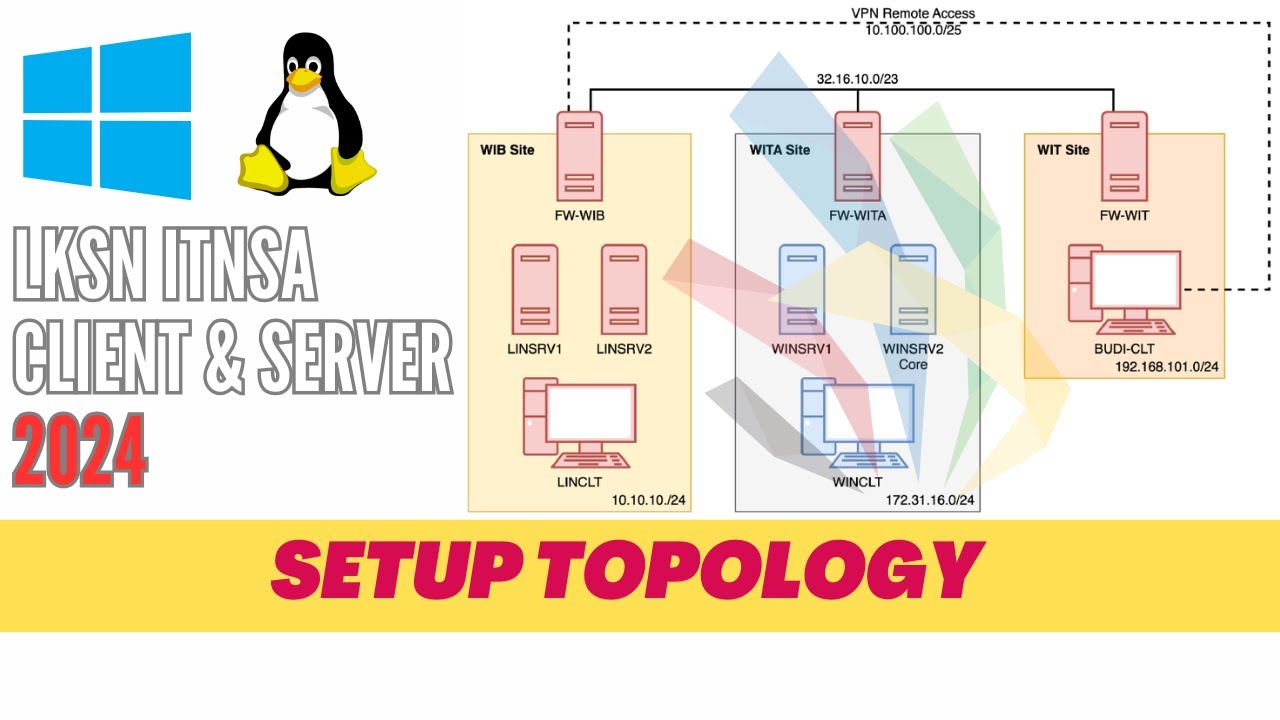
LKSN ITNSA CLIENT SERVER 2024 - SETUP TOPOLOGY

Cloud - 2. Настройка VDS. Docker, nftables

The Perfect Home Server 2025 – 56TB, ECC, IPMI, Quiet & (kind of) Compact
5.0 / 5 (0 votes)
