Getting Started with Magnet AXIOM - File System and Registry
Summary
TLDRIn this video, Jamie McQuaid from Magnet Forensics introduces viewers to analyzing file systems and registry views in Magnet Axiom. Key features highlighted include source linking, navigating between views, and decoding data. The video demonstrates how to access raw file details, use the built-in SQLite viewer for mobile devices, and filter artifacts for specific users or folders. It also showcases the registry view and the ability to export data for further analysis.
Takeaways
- 😀 Jamie McQuaid from Magnet Forensics introduces a tutorial on using Magnet Axiom for file system and registry analysis.
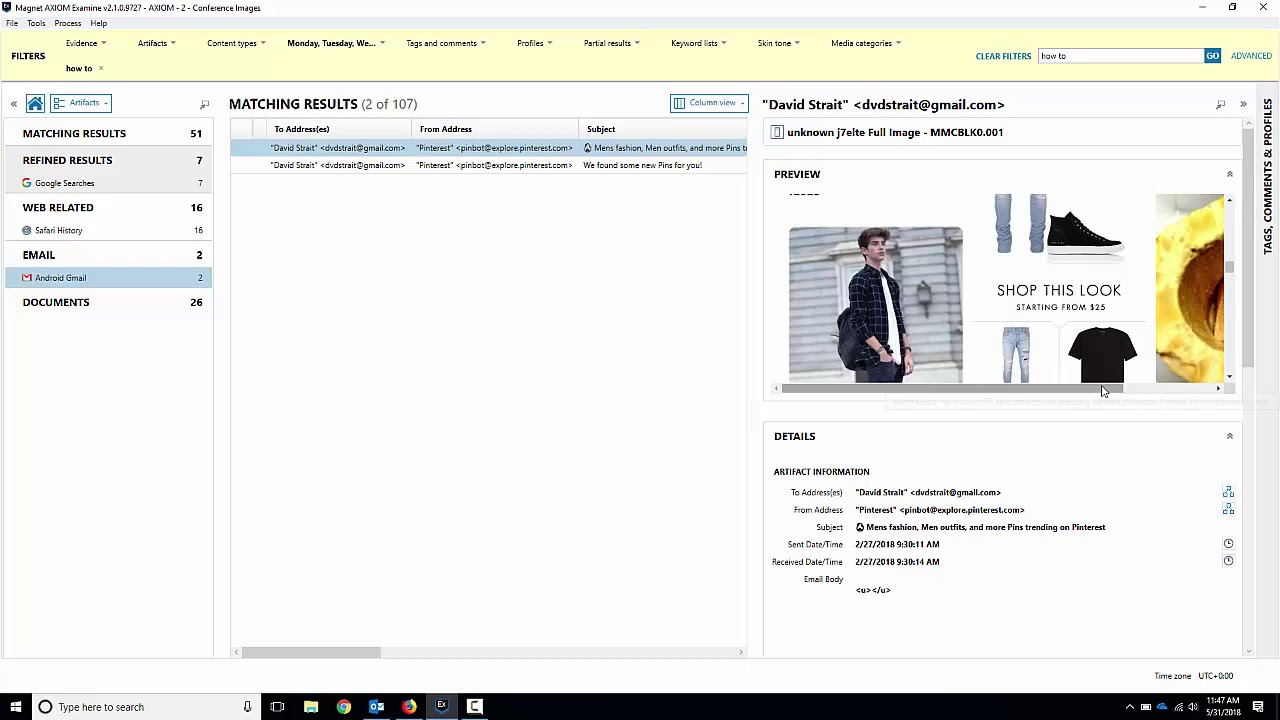
- 🔍 The video demonstrates how to navigate from artifacts to the file system view in Magnet Axiom, highlighting the source and location of artifacts.
- 💾 It showcases the ability to view raw file system details such as MAC times and cluster sizes, as well as raw hex and text data.
- 🔎 The script explains the decoding feature in Magnet Axiom, which attempts to decode highlighted data into readable formats like ASCII, base64, unicode, or timestamps.
- 📊 The tutorial includes a walkthrough of viewing SQLite databases natively within Axiom, including the ability to open and preview tables and data.
- 📱 The video mentions the utility of Axiom's native viewers for mobile device data, such as SQLite databases and plist files for iOS devices.
- 🗂️ It discusses the capability to perform recursive searches across all subfolders within a user's profile or other specified folders.
- 📈 The script highlights the feature to view related artifacts for a specific file or folder, which can be useful for focusing analysis on particular user activity.
- 🔗 The video explains how to use source linking to quickly navigate between the file system and registry views within Axiom.
- 🛠️ It touches on the ability to export registry hives or other data from Axiom for further analysis using dedicated registry tools outside the platform.
Q & A
What is the main focus of the video presented by Jamie McQuaid?
-The main focus of the video is to provide guidance on using Magnet Axiom for analysis in the file system and registry views, including traversing between different views and utilizing the tool's features for in-depth analysis.
How does Magnet Axiom help in navigating to the file system from an artifact?
-Magnet Axiom allows users to navigate to the file system from an artifact by clicking on a link that takes them directly to the SQLite database for that specific artifact, displaying the file system details and raw hex and text data.
What additional feature does Magnet Axiom provide for analyzing raw data?
-Magnet Axiom provides a feature that attempts to decode highlighted data in the raw hex and text view, such as strings, timestamps, and various data types, to assist in the analysis process.
Can Magnet Axiom open SQLite databases natively within the tool?
-Yes, Magnet Axiom has a built-in SQLite viewer that allows users to open and view the contents of an SQLite database directly within the tool, such as tables and their associated data.
What is the purpose of the native plist viewer in Magnet Axiom?
-The native plist viewer in Magnet Axiom is used to view and analyze property list (plist) files from iOS devices, providing details such as IMEI, installed applications, phone numbers, and other relevant information.
How can users manipulate data in the file system view within Magnet Axiom?
-Users can manipulate data in the file system view by selecting options such as 'All Subfolders' to get a recursive view of all files within a folder or user profile, which is useful for timelining activities or filtering data.
What does the 'View Related Artifacts' feature in Magnet Axiom do?
-The 'View Related Artifacts' feature in Magnet Axiom allows users to quickly filter and display artifacts related to a specific file or folder, narrowing down the analysis to a particular user or area of interest within a case.
How does Magnet Axiom handle the analysis of registry data?
-Magnet Axiom provides a dedicated registry view where users can analyze registry hives and artifacts. It also offers source linking to directly navigate to the registry view from an artifact, simplifying the process of locating and analyzing registry data.
What is the significance of the rot13 encoding mentioned in the video?
-Rot13 is a simple letter substitution cipher used by Microsoft to store certain data in the registry. Magnet Axiom automatically translates this encoded data, making it readable and easier for analysts to understand the content.
Can users export data from Magnet Axiom for further analysis using other tools?
-Yes, users can export data from Magnet Axiom by right-clicking and saving files out of the tool, allowing for additional analysis using dedicated registry or other forensic tools outside of Axiom.
What is the benefit of the source linking feature in Magnet Axiom?
-The source linking feature in Magnet Axiom allows for quick navigation between different views, such as the file system and registry views, by providing a direct link to the exact location of the data, saving time and improving efficiency in the analysis process.
Outlines

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraMindmap

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraKeywords

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraHighlights

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraTranscripts

Esta sección está disponible solo para usuarios con suscripción. Por favor, mejora tu plan para acceder a esta parte.
Mejorar ahoraVer Más Videos Relacionados
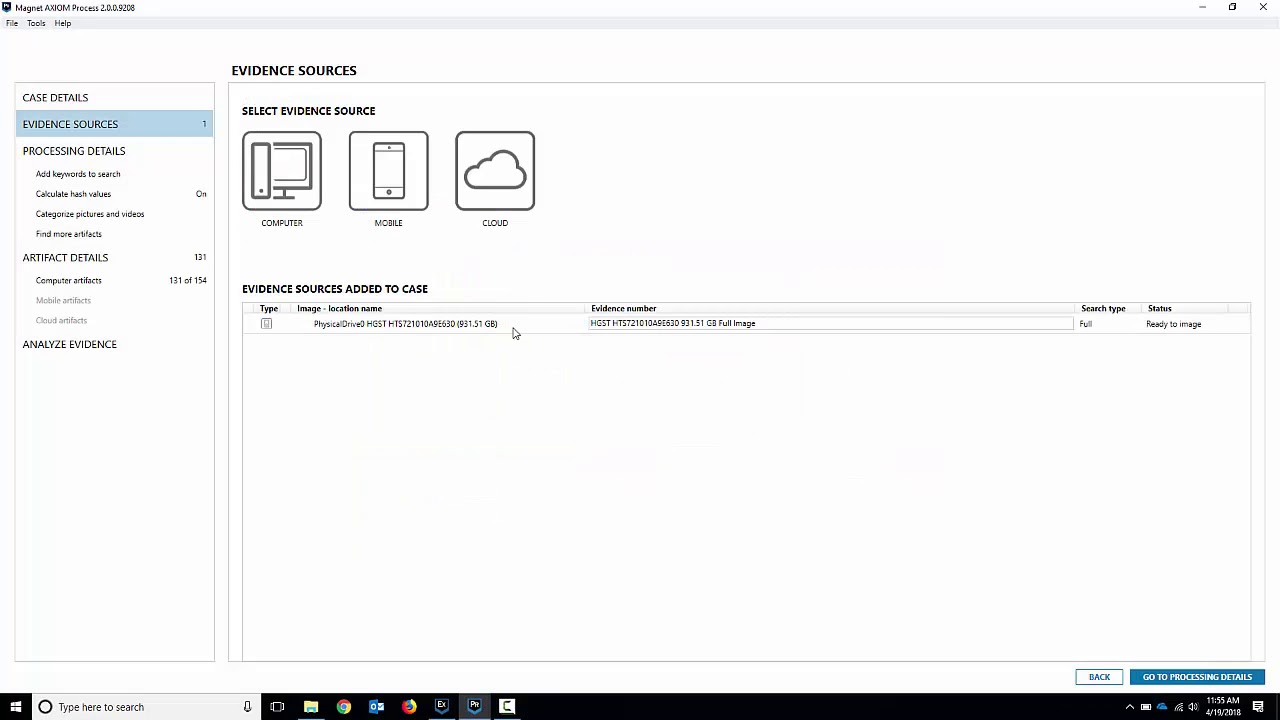
Getting Started with Magnet AXIOM Process - Computers
Getting Started with Magnet AXIOM Examine - Search and Filters

Apple iPhone 7 Quick Acquisition with Magnet AXIOM

Faraday's Law of Induction Demonstration - Penn Physics

Simulasi Magnet dan Induksi Elektromagnetik Menggunakan PHET

¿Puede resolverse la paradoja de Faraday?
5.0 / 5 (0 votes)
