Advanced Wireshark Network Forensics - Part 3/3
Summary
TLDRThis script details a network security analysis of a denial-of-service attack on an FTP server. The investigation uncovers an ARP scan, port scanning, and a brute-force attack resulting in unauthorized file access. The presenter guides through packet analysis techniques, using tools to filter and identify malicious activities, ultimately carving out and examining the downloaded file. The session concludes with resources for further learning in network security and forensics.
Takeaways
- 🔍 The script describes a network security analysis scenario involving a denial-of-service attack on an FTP server.
- 📍 The attacker's IP address is identified as 101.168.56.101, and the FTP server's address is 56.1.
- 🕵️♂️ The analysis aims to determine the cause of the FTP traffic spike and events leading to the server going offline, including file transfers and user account compromises.
- 📝 Documentation of goals, steps, and results is emphasized as a crucial part of the analysis process.
- 🔎 The capture file is filtered to show only two IP addresses, indicating a focus on the attacker and the FTP server.
- 🌐 An ARP scan is detected, suggesting the attacker was mapping the network to find the FTP server.
- 🔑 A port scan reveals open ports 21, 445, 139, 135, and unregistered high-number ports, which might be related to Microsoft NetBIOS.
- 🚀 The script details a brute-force attack on the FTP server, with the attacker successfully logging in using the 'anon anon' credentials.
- 📁 The attacker downloaded a file named 'why we can't have nice cat.PNG', which was carved out of the network traffic for further analysis.
- 🔑 The file's hash was taken to ensure integrity and to compare against the original file on the server.
- 📚 The presenter recommends resources for learning more about network security, including forensics contest, honeynet.org, and malware traffic analysis.
Q & A
What type of attack was reported against the FTP server?
-A denial-of-service attack was reported against the FTP server.
What was the IP address of the attacker?
-The IP address of the attacker was 101.168.56.101.
What was the IP address of the FTP server that was attacked?
-The IP address of the FTP server that was attacked was 56.1.
What was the purpose of the ARP scan mentioned in the script?
-The ARP scan was used by the attacker to discover the IP address of the FTP server and potentially other devices on the network.
How many IP addresses were visible in the capture file according to the statistics?
-Only two IP addresses were visible in the capture file, which were the attacker's address and the FTP server's address.
What ports were found open by the attacker during the port scan of the FTP server?
-The attacker found ports 21, 445, 139, and 135 open during the port scan.
What is the FTP response code that indicates a successful login?
-FTP response code 230 indicates a successful login.
What file did the attacker download from the FTP server?
-The attacker downloaded a file named 'why we can't have nice cat.PNG'.
What method was used to verify the integrity of the downloaded file?
-The file was carved out of the network bytes and its hash was taken to compare it with the hash of the original file on the server.
What resources were recommended in the script for further learning in network security?
-Resources recommended include forensicscontest.com, honeynet.org, malware-traffic-analysis.net, and books such as 'Practical Packet Analysis' and 'Network Forensics: Tracking Hackers through Cyberspace'.
What is the significance of the file signature in the context of the script?
-The file signature, such as 'PNG' in the case of the image file, helps in identifying the type of file that was downloaded by the attacker and ensures it matches the expected file format.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen

37. OCR GCSE (J277) 1.4 Preventing vulnerabilities

Instalasi dan Konfigurasi FTP Server pada Debian 10 Buster
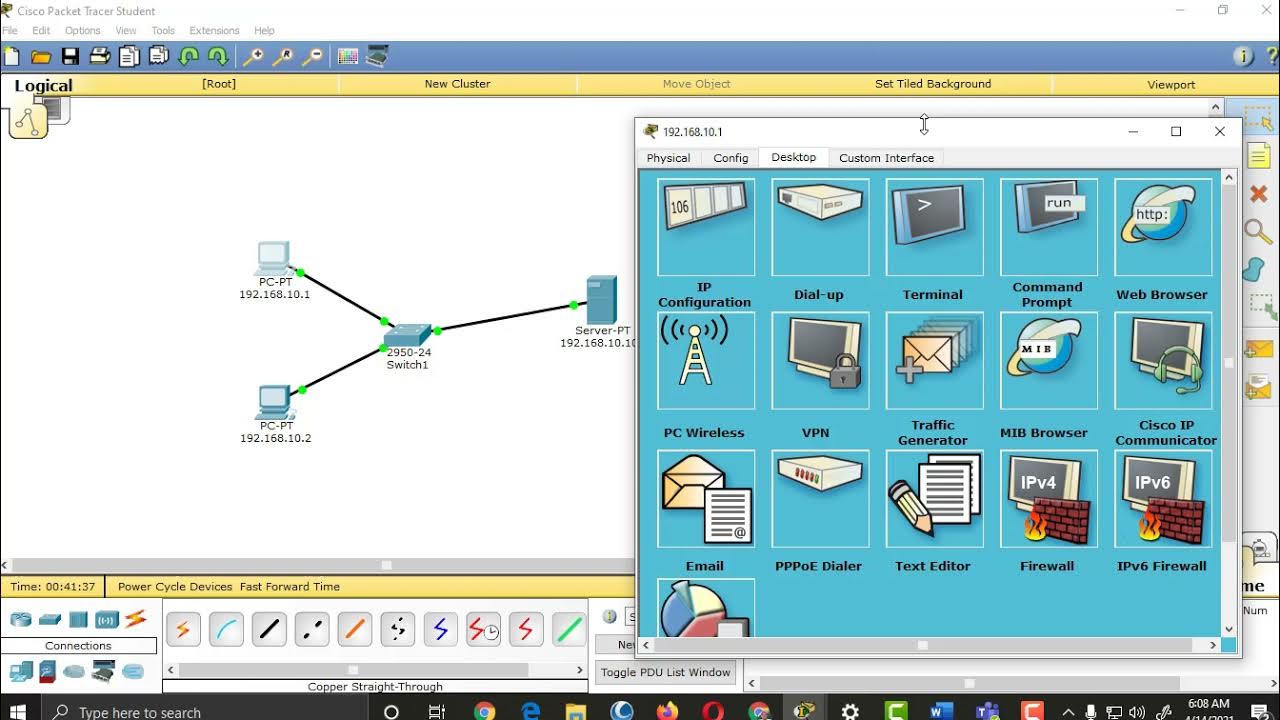
Setting up HTTP, DNS, FTP and DHCP Server Services in Packet Tracer

What is Web Security? | Purpose of Web security | Web Security Threats and Approaches

[HINDI] Networking Basics | Part #54 | Application Layer | File Transfer Protocol (FTP)
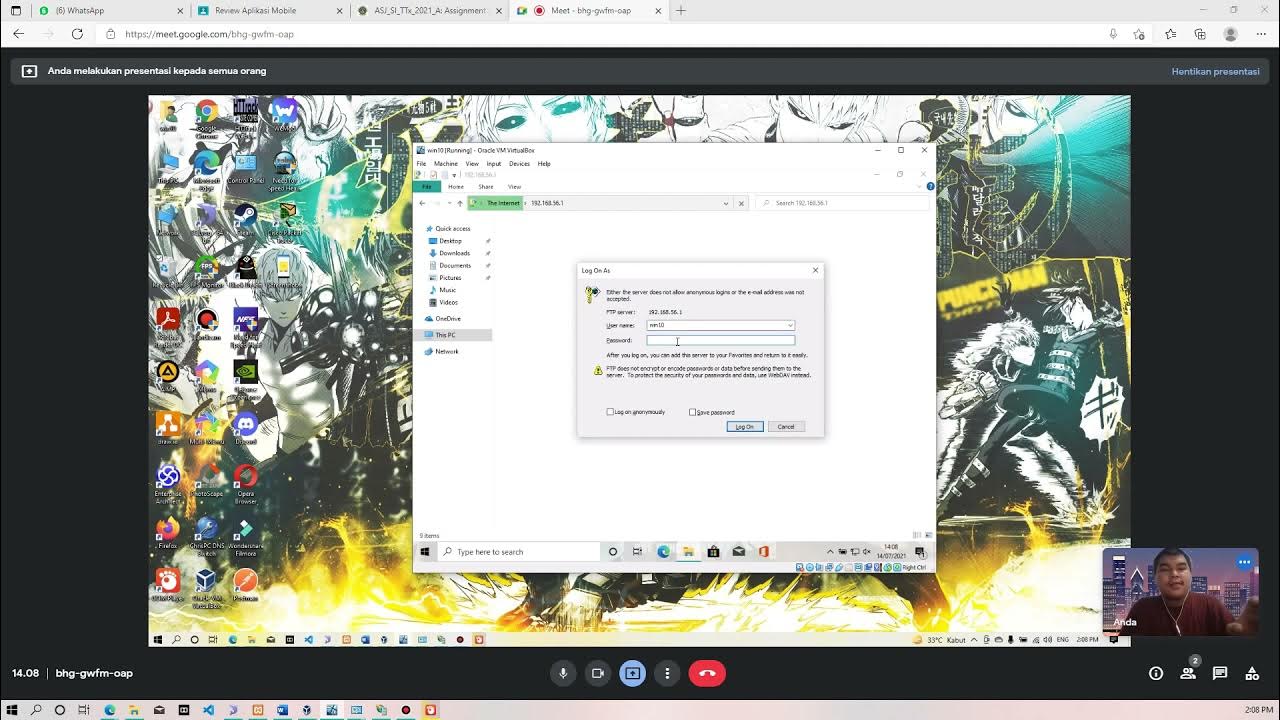
Membuat FTP Server dan FTP Client pada Windows 10
5.0 / 5 (0 votes)
