Simple Penetration Testing Tutorial for Beginners!
Summary
TLDRThe video script offers a step-by-step tutorial on ethical hacking, focusing on scanning devices for vulnerabilities and exploiting them to gain control of a system. It covers the use of tools like nmap for scanning, dirb for directory listing, and metasploit for exploiting found vulnerabilities. The tutorial also delves into privilege escalation, capturing credentials, and emphasizes the importance of security testing to protect servers from such attacks.
Takeaways
- 🚀 The video is an educational tutorial on ethical hacking techniques, emphasizing that hacking is illegal and should not be attempted without permission.
- 🔍 It covers the process of scanning devices to identify vulnerabilities, including servers and phones, to gain control over the system.
- 🔑 The tutorial explains the importance of finding a loophole in the system to exploit for gaining unauthorized access.
- 🛠️ It demonstrates the use of tools like nmap for scanning target devices and identifying open ports and services.
- 🌐 The script mentions the significance of determining the operating system and version to tailor the attack method effectively.
- 🔎 The tutorial includes using dirb to discover directories on a server, which can be potential targets for exploitation.
- 💥 It introduces Metasploit (msfconsole) for launching targeted attacks against discovered vulnerabilities.
- 📈 Post-exploitation techniques are discussed, such as escalating privileges to gain root access and control over the system.
- 🔒 The video shows how to dump usernames and passwords from a compromised system for further exploitation.
- 🛡️ It highlights the importance of defense mechanisms, like firewalls, to block unauthorized access but also their limitations.
- 🔄 The process of uploading and executing files to escalate privileges is illustrated, including overcoming permission issues.
Q & A
What is the main topic of the video script?
-The main topic is end-to-end article hacking, specifically scanning devices and exploiting vulnerabilities to gain control of computer systems.
What tool is recommended for scanning target devices?
-The tool recommended for scanning target devices is Nmap.
Why is it important to scan devices before attempting an exploit?
-It is important to scan devices to identify vulnerabilities, such as open ports and running services, which can be exploited to gain control of the system.
What does 'elevating privileges' mean in the context of hacking?
-Elevating privileges means gaining higher-level access permissions on a system, typically from a regular user account to root or administrative access.
What is the purpose of using the 'dirb' tool in this hacking tutorial?
-The 'dirb' tool is used to discover directories and files on a web server that might be vulnerable to exploitation.
What is the significance of the 'CGI bin' directory in the script?
-The 'CGI bin' directory is significant because it often contains executable scripts that can be exploited to gain access to the system.
How is Metasploit used in the hacking process described in the script?
-Metasploit is used to find and exploit vulnerabilities in the target system, particularly using the 'shellshock' exploit in this tutorial.
What is a 'reverse shell' and why is it useful for hackers?
-A reverse shell is a method where the target machine connects back to the hacker's machine, bypassing firewall restrictions that block inbound connections, allowing the hacker to control the system remotely.
What is the final goal of the hacking process described in the script?
-The final goal is to gain root access to the target system and extract sensitive information, such as usernames and passwords.
Why does the script emphasize the illegality of hacking?
-The script emphasizes the illegality of hacking to remind viewers that these techniques should not be used for malicious purposes and to warn against attempting these actions without permission.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen

Dalfox XSS Automation Scanner for Bug Bounty | Security Awareness

Simple Penetration Metasploitable 2 (Cybersecurity)

Buffer Overflow Exploit: A Step-by-Step Tutorial for Beginners
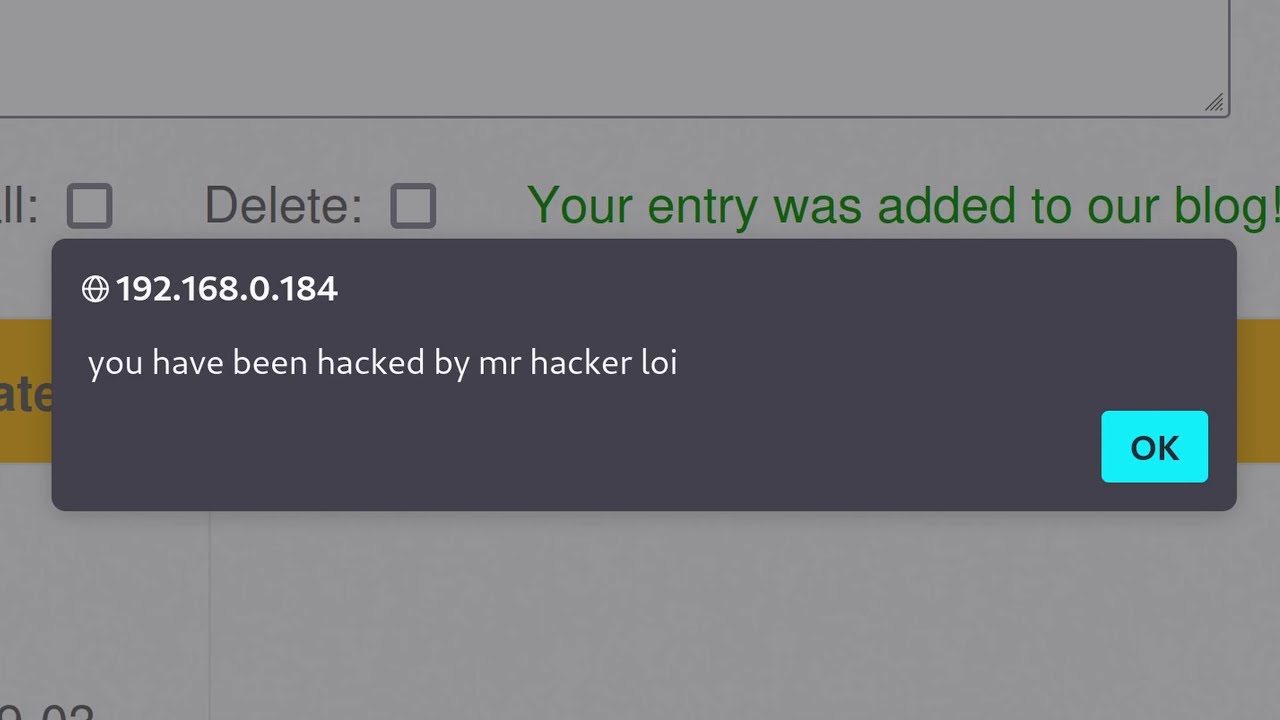
Cross Site Scripting (XSS) tutorial for Beginners

Beginners Guide to Hacking (Start to Finish)
Belajar Ethical Hacking Lengkap (Part 1) || Introduction
5.0 / 5 (0 votes)
