Implementing Infrastructure as Code with Terraform | AWS Cloud Resume Challenge - Part 6
Summary
TLDRIn part six of the AWS Cloud resume challenge, host Richard dives into the concept of Infrastructure as Code (IaC) with Terraform, chosen by the audience. He guides through setting up a provider configuration, creating a Lambda function, and deploying it with Terraform. Richard also covers deploying a Lambda function URL and addressing IAM permissions for accessing DynamoDB. The video concludes with a functional Lambda setup, a walkthrough of Terraform files, and suggestions for further automation with GitHub actions, inviting viewers to explore creating IaC for DynamoDB, S3, and CloudFront.
Takeaways
- 😀 The video is part of a series on the AWS Cloud resume challenge, hosted by Richard.
- 🛠️ The series has covered various topics including CI/CD setup for an S3 bucket, creation of an S3 bucket with CloudFront, a DynamoDB table, and a Lambda function in Python.
- 📈 The main focus of this part is on IaC (Infrastructure as Code), with an emphasis on using Terraform over CloudFormation based on audience poll results.
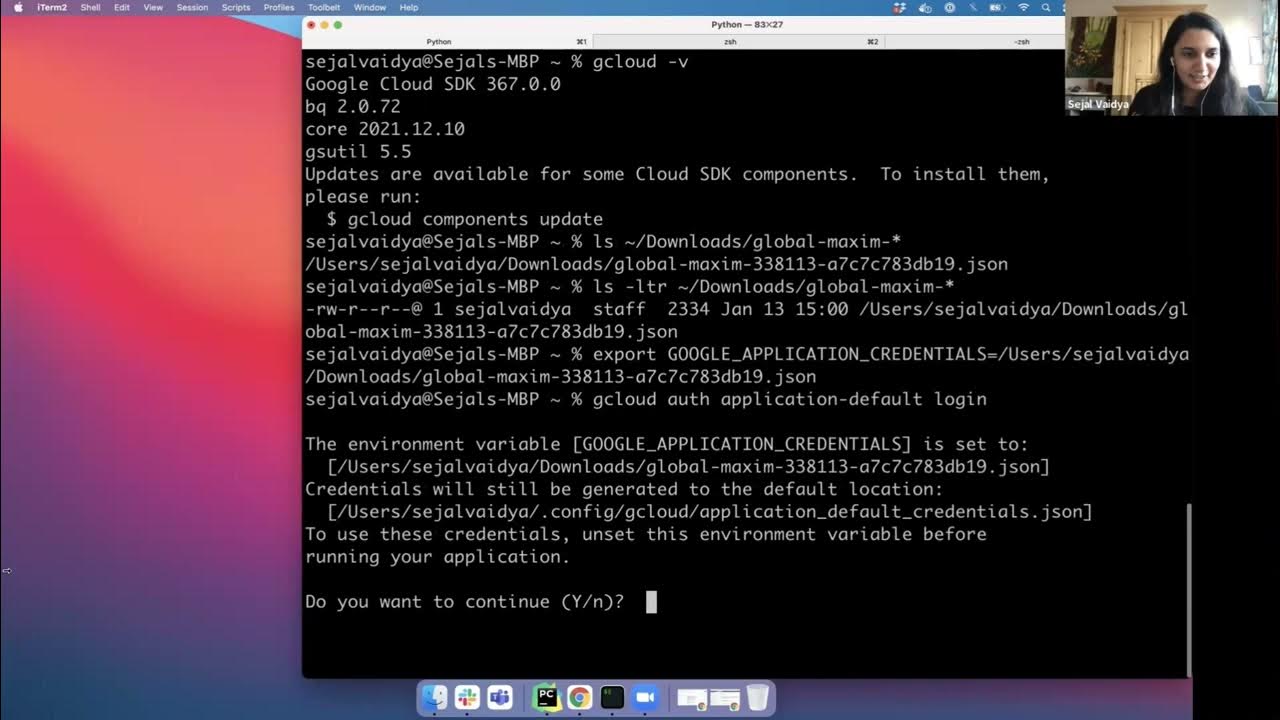
- 📝 The tutorial guides through setting up the `provider.tf` file for Terraform, detailing the use of AWS CLI profiles or direct access key and secret key setup.
- 🔧 It demonstrates creating a Lambda function and an IAM rule using Terraform, including the use of a zip file for the Lambda function code deployment.
- 📁 The script mentions creating a `func.py` file containing the Python code for the Lambda function, which is then referenced in the Terraform files.
- 🚀 The process of deploying infrastructure with Terraform is explained, including the use of `terraform init`, `terraform plan`, and `terraform apply` commands.
- 🔗 The importance of the state file in Terraform for tracking infrastructure changes is highlighted.
- 🔒 A section is dedicated to adding a Lambda function URL with proper authorization settings to allow public access or restrict it to specific domains.
- 🛡️ The video addresses a common error related to IAM permissions, showing how to attach a policy to an IAM role to grant the Lambda function access to DynamoDB.
- 🔄 The script suggests automating further deployments with GitHub Actions and setting up a CI/CD pipeline for backend changes and testing.
Q & A
What is the main topic covered in part six of the AWS Cloud resume challenge?
-The main topic covered is Infrastructure as Code (IC), specifically using Terraform for deploying AWS resources.
What AWS services were set up in the previous parts of the challenge?
-In the previous parts, they set up CI/CD for an S3 bucket, created an S3 bucket with CloudFront to host a website, and created a DynamoDB table and a Lambda function in Python.
Why did the audience choose Terraform over CloudFormation?
-The audience preferred Terraform based on a poll conducted by the host, although the exact reasons for their preference are not specified in the script.
What is the purpose of the Lambda function created in the script?
-The Lambda function is used to get a viewer count from a DynamoDB table and display it on the website.
How is the Lambda function code transferred to the AWS environment using Terraform?
-The Lambda function code is transferred using a zip file that contains the Python code written for the Lambda function.
What is the significance of the 'terraform plan' command?
-The 'terraform plan' command shows what changes are planned to be made to the AWS infrastructure, such as adding or modifying resources.
Why was an 'Internal Server Error' encountered when trying to access the Lambda function URL?
-The error occurred because the Lambda function's IAM role did not have the necessary permissions to access DynamoDB, which it requires to get and update the viewer count.
What is the role of the 'terraform apply' command in the deployment process?
-The 'terraform apply' command is used to create or update resources in the AWS infrastructure according to the Terraform configuration files.
What is the purpose of the 'terraform state' file?
-The 'terraform state' file keeps track of the current state of the infrastructure, allowing Terraform to understand what has changed and what needs to be updated or created.
How can the deployment process be automated using GitHub Actions?
-GitHub Actions can be set up to automatically deploy changes made to the Terraform files, ensuring that updates to the infrastructure are applied quickly and consistently.
What additional resources could be managed by Terraform as suggested in the script?
-The script suggests creating Terraform files for managing a DynamoDB table, S3 bucket, and CloudFront distribution, in addition to the Lambda function.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführen5.0 / 5 (0 votes)