How Kerberos Works
Summary
TLDRThis video introduces Kerberos, a single sign-on network authentication protocol that allows secure access to servers through a ticketing system. Named after the mythological three-headed dog, Kerberos involves three components: the user (client), the resource (file server), and the key distribution center. The process begins with the client sending an encrypted access request to the authentication server, which verifies the credentials and issues a ticket granting ticket (TGT). The client then uses this ticket to request access from the ticket granting server, which provides a time-sensitive token for server access, ensuring high security and streamlined login.
Takeaways
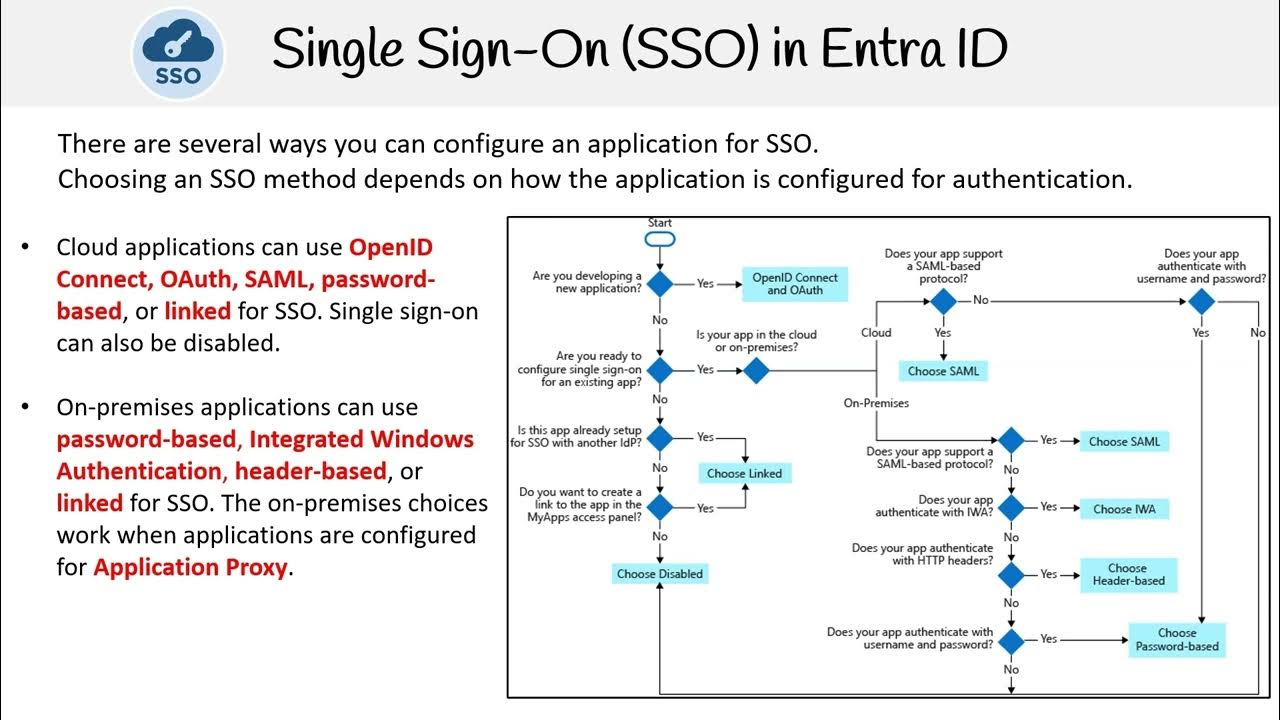
- 🔑 Kerberos is a single sign-on (SSO) network authentication protocol that simplifies access to multiple services.
- 🐶 The name 'Kerberos' is inspired by the mythological three-headed dog that guarded access to the underworld.
- 📄 The protocol involves three main components: the client (user), the resource (file server), and the key distribution center (KDC).
- 🛡️ The KDC consists of an authentication server and a ticket granting server, which manage authentication and ticket issuance.
- 🔒 Client authentication starts with the user sending a request to the authentication server using a username and password.
- 🔑 The request is encrypted using a secret key derived from the client's password to ensure security.
- ✅ Once verified, the authentication server issues a Ticket Granting Ticket (TGT) for the client.
- 📩 The client uses the TGT to request access to specific resources from the ticket granting server.
- 🧾 The ticket granting server issues a token to the client, which is used to access the desired file server.
- ⏳ Kerberos allows time-sensitive access, meaning the client can only access resources for a limited time, enhancing security.
Q & A
What is Kerberos?
-Kerberos is a single sign-on (SSO) network authentication protocol that allows authorized users to access a server using a ticketing scheme.
What does the term 'Kerberos' refer to?
-The term 'Kerberos' is derived from the mythological three-headed dog that guarded the gates of the underworld, symbolizing its role in restricting access.
What are the three main components of Kerberos?
-The three main components of Kerberos are the client (user), the resource (file server), and the Key Distribution Center (KDC), which consists of an authentication server and a ticket-granting server.
How does the authentication process begin in Kerberos?
-The authentication process begins with the client sending an access request to the KDC, using its username and password, which is encrypted with a secret key derived from the client’s password.
What role does the authentication server play in Kerberos?
-The authentication server verifies the client's credentials against its database, using the stored password hash for decryption. Upon successful verification, it issues a Ticket Granting Ticket (TGT).
What is a Ticket Granting Ticket (TGT)?
-A Ticket Granting Ticket (TGT) is a ticket issued by the authentication server, encrypted with a different secret key, which allows the client to request access to resources from the ticket-granting server.
What happens after the client receives the TGT?
-After receiving the TGT, the client forwards it to the ticket-granting server, which decrypts it and provides a token that is encrypted with another key.
What is the purpose of the token provided by the ticket-granting server?
-The token provided by the ticket-granting server allows the client to access the file server by presenting it, which is then verified using a shared secret key.
How does the file server determine access duration?
-The file server grants access based on the token, with the provision that access is time-sensitive, meaning the client can only access the server for a specified duration.
Why is Kerberos considered highly secure?
-Kerberos is considered highly secure because it uses a single login per session and relies on encrypted tickets and tokens for authentication, minimizing the risk of unauthorized access.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen
5.0 / 5 (0 votes)