Payatu Case Study | Automotive Security Assessment | EV Security Testing
Summary
TLDRThis video covers the assessment of hardware security vulnerabilities in electric vehicles (EVs), focusing on protocols like CAN, UART, JTAG, and Bluetooth. The speaker, a lead IoT security consultant, explains their process for testing EV devices, identifying critical vulnerabilities like outdated Android systems and insecure ADB access. They also discuss the use of professional tools to perform these assessments, emphasizing the importance of comprehensive testing under tight deadlines. The findings include risks that could lead to financial loss, physical harm, and trust erosion, urging companies to conduct regular security audits.
Takeaways
- 🔒 The speaker is a lead IoT security consultant and hardware security researcher, focusing on securing devices from a hardware perspective.
- 🔍 As a consultant, they conduct hardware testing of client devices, provide remediation steps, and ensure device security.
- 💻 As a researcher, they analyze various IoT devices, such as medical devices, to stay updated with vulnerabilities and improve testing processes.
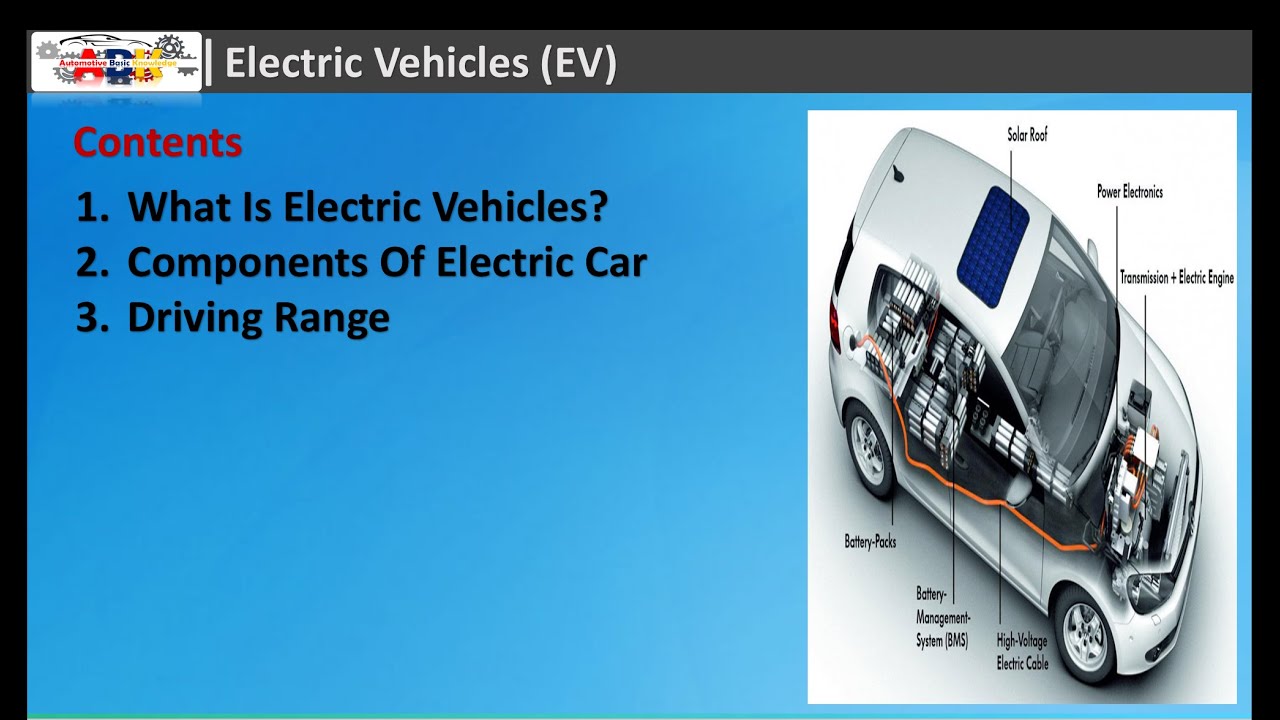
- 🚗 The client operates in the EV (electric vehicle) sector, requiring a security assessment of their device, particularly its communication protocols.
- 🛡️ CAN protocol, commonly used in automotive applications, is highlighted for its speed and importance in critical communication, like airbags.
- 🔧 The hardware assessment involved identifying debug ports (e.g., UART, JTAG) that could allow firmware extraction and malicious firmware injection.
- 📡 The team also sniffed communication protocols like SPI, I2C, and CAN to detect vulnerabilities, including potential data injection over the CAN bus.
- 📱 A mobile Android app communicating with the EV dashboard was tested for sensitive data leaks and Bluetooth security issues, including replay attacks.
- ⚠️ Critical vulnerabilities included outdated Android systems on the EV hardware and unauthorized ADB shell access, posing significant security risks.
- 🚨 Four high-severity vulnerabilities were found, including DoS attacks on the CAN bus, malicious packet injection, and exposure of sensitive boot logs.
Q & A
What is the primary role of a lead IoT security consultant?
-A lead IoT security consultant is responsible for overseeing the security of client devices from a hardware perspective, conducting hardware testing, and suggesting remediation steps to enhance device security.
How does a hardware security researcher contribute to IoT device security?
-A hardware security researcher contributes by researching various devices like medical or IoT devices to identify and understand emerging vulnerabilities, ensuring that testing processes remain current and effective.
Why is it important for the EV sector to conduct security assessments?
-Security assessments are crucial in the EV sector due to the implementation of numerous communication protocols in EV devices, which if compromised, could lead to serious security and safety issues.
What is the significance of the CAN protocol in automotive security?
-The CAN protocol is significant in automotive security because it is a fast communication protocol used for critical vehicle functions, such as airbag deployment during sudden braking, requiring quick and reliable communication.
What kind of vulnerabilities were discovered during the hardware assessment of the EV device?
-The hardware assessment revealed vulnerabilities such as the possibility of firmware extraction from debug ports like UART or JTAG, and the ability to inject malicious data over communication protocols like SPI, I2C, and CAN.
How was the firmware extracted from the SPH chip during the assessment?
-The firmware was successfully extracted from the SPH chip by identifying and exploiting its vulnerabilities, which allowed for the potential patching of malicious firmware.
What tools and techniques were used to perform the hardware assessment on the EV device?
-Tools such as the exploit Nano board for firmware extraction, Bus Auditor for identifying debug ports, and Bluetooth adapters for communication sniffing were used. Techniques included checking for firmware extraction methods, sniffing wire communication, and analyzing Bluetooth data.
What challenges did the team face during the security assessment of the EV device?
-The team faced challenges such as working within tight deadlines to perform comprehensive testing, covering all areas identified in a large checklist to ensure a thorough security assessment.
What were the critical vulnerabilities found in the EV hardware during the assessment?
-Two critical vulnerabilities were identified: access to the ADB shell which provided complete device control, and the outdated Android version running on the EV hardware, which contained numerous security vulnerabilities.
How did the team approach the firmware assessment of the EV device?
-The firmware assessment was conducted using a proprietary framework, focusing on areas such as sensitive information leakage, Bluetooth communication security, and potential for malicious data injection.
What advice does the security professional give to organizations regarding EV security?
-The security professional advises organizations to conduct comprehensive security assessments of their EV systems, keep up with security updates, and perform regular assessments to ensure the devices are well protected against potential threats.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen
5.0 / 5 (0 votes)