What is XDR vs EDR vs MDR? Breaking down Extended Detection and Response
Summary
TLDRThis video script delves into cybersecurity concepts of EDR (Endpoint Detection and Response), XDR (Extended Detection and Response), and MDR (Managed Detection and Response). It explains how EDR focuses on post-execution malware detection and mitigation, while XDR integrates multiple security products for a cohesive threat response. The script also highlights the importance of minimizing 'dwell time'—the period an attacker remains undetected in a network—and how MDR services can provide 24/7 threat monitoring and response using these technologies to enhance cybersecurity posture.
Takeaways
- 🔍 Dwell time refers to the duration an attacker can remain undetected within a network, calculated by adding the mean time of detection and mean time of repair.
- 📉 In 2020, the average global dwell time was 56 days, meaning attackers had nearly two months inside a network before being detected.
- 🛡️ EDR (Endpoint Detection and Response) tools aim to reduce dwell time by detecting and responding to threats at the endpoint level.
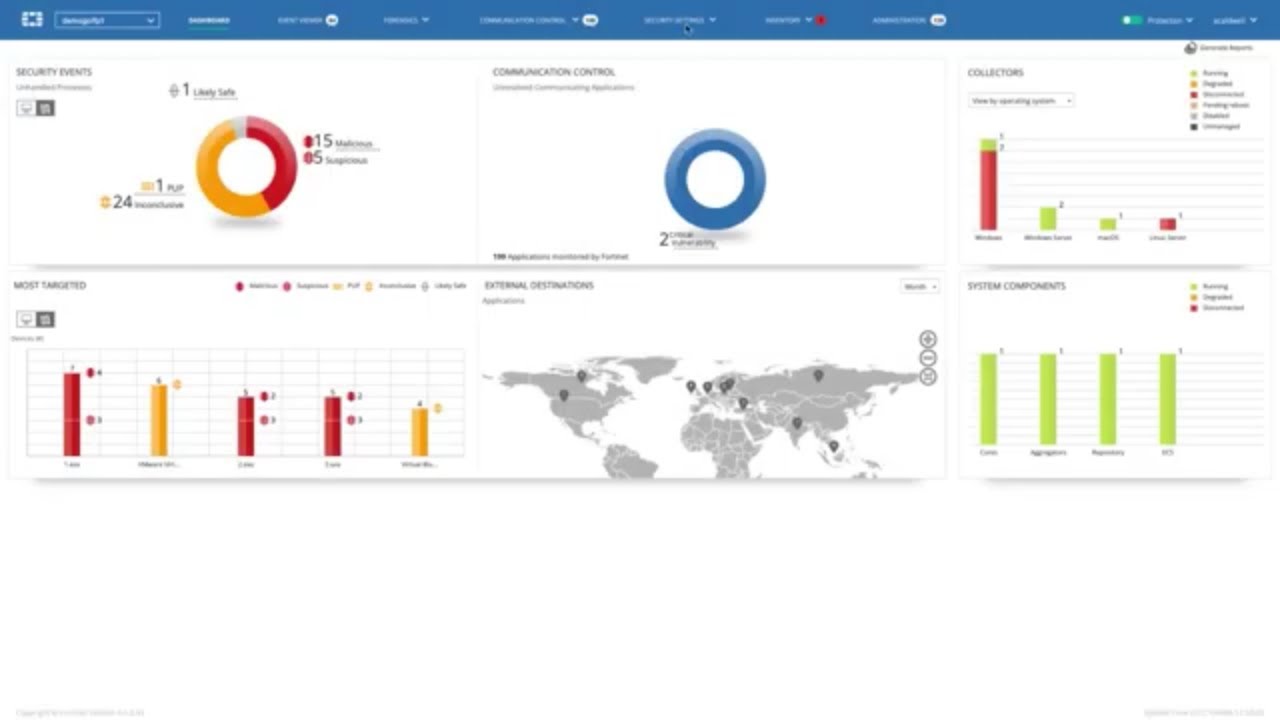
- 🌐 XDR (Extended Detection and Response) expands on EDR by including other critical network areas like firewalls and cloud applications.
- 🔧 EDR focuses on post-infection detection and response, identifying and mitigating threats that antivirus engines may miss.
- 🤖 XDR integrates multiple security products, using AI to analyze and correlate telemetry data to detect and respond to threats automatically or manually.
- ⚙️ The key components of XDR include integration of security products, AI-driven analysis, and automated response based on preconfigured playbooks.
- 🕵️ MDR (Managed Detection and Response) is a 24/7 service provided by third parties, leveraging EDR, XDR, and other technologies to monitor, detect, and respond to threats.
- 📊 MDR providers vary in services offered, from basic threat hunting and response to advanced incident response with on-site personnel.
- 🔗 EDR and XDR are complementary tools, with EDR focusing on endpoints and XDR providing broader network visibility to reduce dwell time and enhance threat response.
Q & A
What is dwell time in cybersecurity?
-Dwell time refers to the length of time an attacker can operate undetected within a network. It is calculated by adding the mean time of detection to the mean time of repair.
What was the average global dwell time in 2020 according to FireEye?
-The average global dwell time in 2020 was 56 days, indicating that attackers had nearly two months on average inside a network before being detected.
What are EDR and XDR, and how do they aim to reduce dwell time?
-EDR (Endpoint Detection and Response) and XDR (Extended Detection and Response) are cybersecurity tools designed to detect and respond to threats more quickly, thereby reducing the time an attacker can remain undetected within a network.
What is the primary focus of EDR?
-EDR focuses on detection and response at the endpoint level, specifically targeting threats that have already been executed on a machine, after traditional antivirus solutions have failed.
How does XDR differ from EDR?
-XDR expands on EDR by including other critical areas of the network, such as firewalls and cloud applications, and it integrates multiple security products into a cohesive system for unified threat detection and response.
What is the significance of forensics in the EDR process?
-Forensics in EDR is crucial for facilitating the threat hunting process, allowing security professionals to search for specific indicators of compromise or analyze recorded events on endpoints to identify the impact of breaches.
How does XDR leverage AI in its operation?
-XDR uses AI to analyze and correlate telemetry data from various security products, identifying behavioral patterns that may indicate a security risk, which would be nearly impossible to detect manually.
What is the role of MDR in the context of cybersecurity?
-MDR (Managed Detection and Response) is a service provided by a third party that offers 24/7 threat monitoring, detection, and lightweight response, leveraging a combination of technologies and often incorporating XDR capabilities for extended visibility.
What are the key components of an MDR service as defined by Forrester?
-Forrester defines the key components of an MDR service as security analytics, proactive threat hunting, and automated incident response using SOAR (Security Orchestration, Automation, and Response) or manual response using predefined playbooks.
How do EDR and XDR complement each other in a cybersecurity strategy?
-EDR and XDR are not mutually exclusive but complementary. EDR provides detailed insights at the endpoint level, while XDR offers a broader view by integrating data from various network components, enhancing the overall ability to detect and respond to threats.
Why might an organization opt for an MDR service over managing EDR or XDR in-house?
-Organizations might choose an MDR service due to a lack of in-house manpower or expertise to manage EDR or XDR solutions effectively, allowing them to leverage the specialized knowledge and resources of a managed service provider.
Outlines

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenMindmap

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenKeywords

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenHighlights

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenTranscripts

Dieser Bereich ist nur für Premium-Benutzer verfügbar. Bitte führen Sie ein Upgrade durch, um auf diesen Abschnitt zuzugreifen.
Upgrade durchführenWeitere ähnliche Videos ansehen

Microsoft Defender for Business EDR to XDR Security Upgrade Using Microsoft 365 Business Premium

XDR Implementation And AI Use Cases
Uncovering Cyber Threats: EDR vs SIEM Comparison #cybersecurity #cyber #risk #threats #detective

Complete Guide to SentinelOne EDR (Endpoint Detection and Response): Exploring the Console in Part 1
FortiEDR - Advanced Endpoint Protection with Automated Detection and Response | Endpoint Security

Kernel Karnage: Patching EDR in Kernel Space
5.0 / 5 (0 votes)
