Azure DevOps Workload Identity Federation with Azure Overview. NO MORE SECRETS!
Summary
TLDRThis video explores leveraging workload identity federations in Azure DevOps to securely authenticate and authorize service connections without relying on secrets. It highlights the drawbacks of traditional app registration methods with secrets and introduces using OpenID Connect with Azure Active Directory (AAD) to establish a federated identity and generate access tokens. The process streamlines security, simplifies maintenance, and grants specific pipelines controlled access to service connections representing app registrations. Additionally, the video covers converting existing secret-based service connections, bulk conversion scripts, and utilizing managed identities as an alternative for those without app registration permissions.
Takeaways
- 💻 Azure DevOps can leverage Workload Identity Federations to securely authenticate service-to-service communications, eliminating the need for storing secrets.
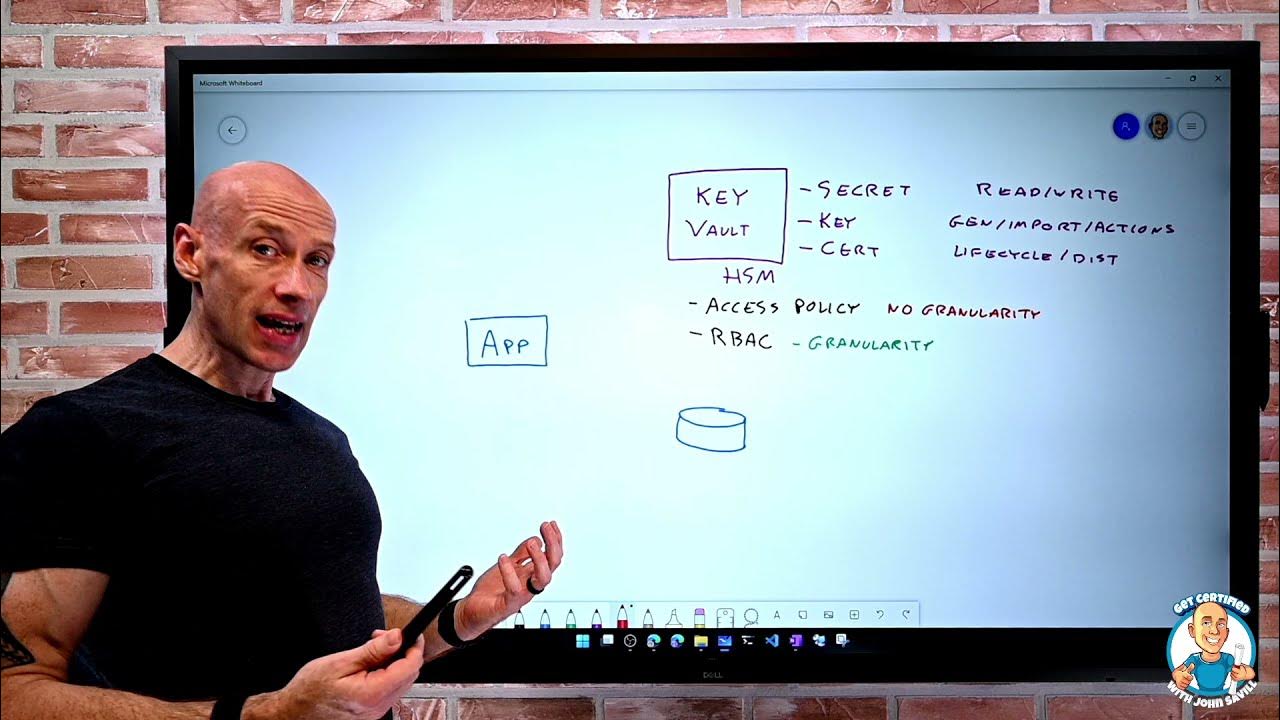
- 🔑 Traditionally, app registrations and service principles in Azure AD (ENT) facilitated authentication, requiring secrets for service connections in Azure DevOps.
- 🛠️ With Identity Federation, the reliance on secrets is removed, enhancing security and simplifying maintenance by using OpenID Connect for authentication.
- 📚 Azure DevOps automatically integrates with Azure AD, simplifying the initial setup for OpenID Connect-based authentication.
- 🛡️ Workload Identity Federation service connections in Azure DevOps eliminate the need for secrets by establishing a federation link to app registrations.
- 📝 Managed identities offer an alternative to app registrations, useful when permissions to create app registrations are restricted.
- 📈 The process involves creating a federated credential for the managed identity, specifying issuer URL and subject identifier.
- 🔧 Azure DevOps supports converting existing service connections to use Workload Identity Federation, streamlining the transition to a more secure setup.
- 🔨 Role-Based Access Control (RBAC) in Azure ensures that the app registration or managed identity has the necessary permissions on target resources.
- 📊 Managed identities and service principals enable Azure DevOps pipelines to authenticate without secrets, relying on tokens issued by Azure AD.
Q & A
What is the purpose of using workload identity federations in Azure DevOps?
-The purpose of using workload identity federations in Azure DevOps is to securely authenticate services without the need for secrets, allowing pipelines to interact with Azure resources securely and efficiently.
What role does Azure Active Directory (Azure AD) play in the authentication process between Azure DevOps and Azure?
-Azure Active Directory (Azure AD), formerly known as Entra, acts as the identity provider that binds Azure DevOps and Azure together, facilitating the authentication process by trusting app registrations and issuing tokens for secure interactions.
How does the traditional authentication method using service principals and secrets work in Azure DevOps?
-Traditionally, Azure DevOps uses an app registration in Azure AD to create a service principal, which is then configured with a secret. This secret is used by a service connection in Azure DevOps to authenticate and interact with Azure resources.
What are the drawbacks of using secrets for authentication in Azure DevOps?
-Using secrets for authentication in Azure DevOps poses security risks, as it requires storing and managing sensitive information, which could be misused if compromised. It also involves additional management tasks, such as secret rotation and expiry handling.
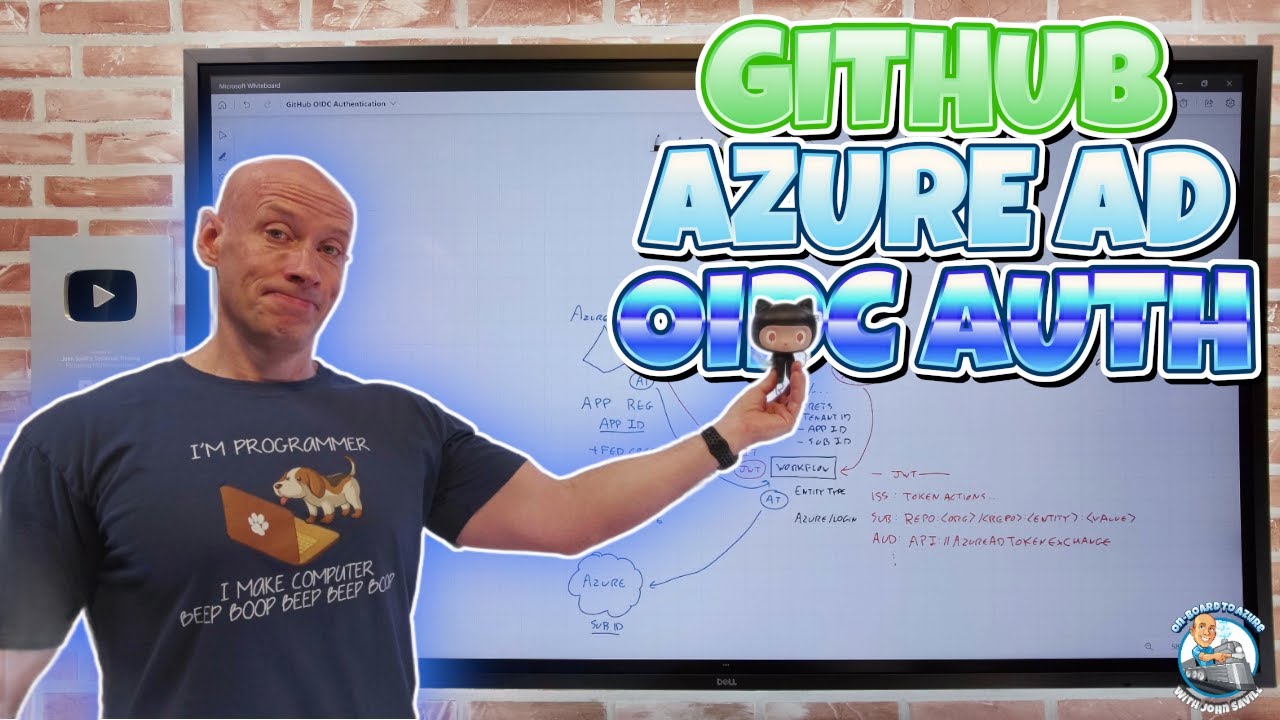
How does OpenID Connect improve the authentication process in Azure DevOps?
-OpenID Connect improves the authentication process by allowing Azure DevOps to authenticate using identity tokens instead of secrets. This method leverages a standard protocol for authentication, reducing the need for managing secrets and enhancing security.
What is required to create a new workload identity federation-based service connection in Azure DevOps?
-To create a new workload identity federation-based service connection, one needs permission to create an app registration in the Azure AD tenant. This app registration will be linked to the service connection without requiring a secret.
How does Azure DevOps authenticate using workload identity federation and OpenID Connect?
-Azure DevOps authenticates using workload identity federation and OpenID Connect by issuing an identity token from Azure DevOps, which is then validated and exchanged for an access token by Azure AD, allowing secure access to Azure resources.
Can existing service connections using secrets be converted to use workload identity federation?
-Yes, existing service connections using secrets can be easily converted to use workload identity federation, enhancing security by eliminating the need for secrets and simplifying maintenance.
What alternative is available in Azure DevOps if creating app registrations is not permitted?
-If creating app registrations is not permitted, managed identities can be used as an alternative in Azure DevOps. This allows for secure authentication without needing to manage app registrations or secrets.
What are the benefits of using workload identity federation in Azure DevOps?
-The benefits of using workload identity federation in Azure DevOps include improved security by avoiding secrets, simplified management without the need for secret rotation, and streamlined authentication processes using standard protocols like OpenID Connect.
Outlines

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنMindmap

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنKeywords

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنHighlights

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنTranscripts

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآن5.0 / 5 (0 votes)