How to BECOME UNHACKABLE?
Summary
TLDREste video ofrece estrategias esenciales para protegerse contra hackers experimentados. Se discuten pasos para asegurar teléfonos inteligentes, como establecer contraseñas fuertes y activar el buscador de dispositivos, así como mantener actualizaciones automáticas. Se aconseja eliminar aplicaciones innecesarias, usar firewalls de aplicaciones y desactivar Wi-Fi y Bluetooth cuando no se usan. También se explora cómo fortalecer cuentas en línea con gestores de contraseñas, evitar preguntas de seguridad y habilitar la autenticación de dos factores. Finalmente, se menciona la importancia de proteger redes domésticas, con un enlace a una guía adicional para fortalecer la seguridad de la red.
Takeaways
- 🔒 Establecer una contraseña fuerte en la pantalla de bloqueo y activar el dispositivo de seguimiento de Google para proteger tu smartphone.
- 📱 Configurar las actualizaciones de software para que se descarguen e instalen automáticamente para evitar vulnerabilidades conocidas.
- 📱 Eliminar aplicaciones innecesarias y usar herramientas de firewall de aplicaciones como NetGuard o Lockdown para mejorar la seguridad.
- 🚫 No usar Wi-Fi o Bluetooth sin necesidad y desactivar la conexión automática a redes abiertas para evitar ataques.
- 📡 Conectar a redes Wi-Fi públicas solo mediante VPN para proteger la privacidad y la seguridad de los datos.
- 🚫 No instalar aplicaciones desde fuentes no oficiales para evitar malware o spyware.
- 🔄 Realizar una restauración de fábrica si sospecha que su teléfono está infectado con spyware.
- 💾 Mantener copias de seguridad de los datos en un disco duro cifrado y no confiar únicamente en el almacenamiento en la nube.
- 🔑 No usar la misma contraseña en todas partes y usar gestores de contraseñas para generar y almacenar contraseñas seguras.
- 🔒 Habilitar la autenticación de dos factores en todas las cuentas en línea y preferir herramientas de autenticación de código abierto en lugar de SMS.
- 🏠 Seguir un guía paso a paso para proteger la red doméstica, disponible en el enlace de la descripción del vídeo.
Q & A
¿Qué dos pasos son cruciales para asegurar un smartphone según el guion?
-Establecer una contraseña fuerte en la pantalla de bloqueo y activar el dispositivo de encontrar Google.
¿Por qué es importante actualizar automáticamente el software de un smartphone?
-El 80% de los hacks a smartphones ocurren debido a software obsoleto, y los hackers comparten vulnerabilidades conocidas en diferentes foros de hacking.
¿Qué son los 'firewalls de aplicación' y qué hacen?
-Los 'firewalls de aplicación' son aplicaciones que permiten bloquear o restringir la conexión Wi-Fi para ciertas aplicaciones que no la necesitan, evitando que envíen o reciban datos si están comprometidas o tienen características maliciosas.
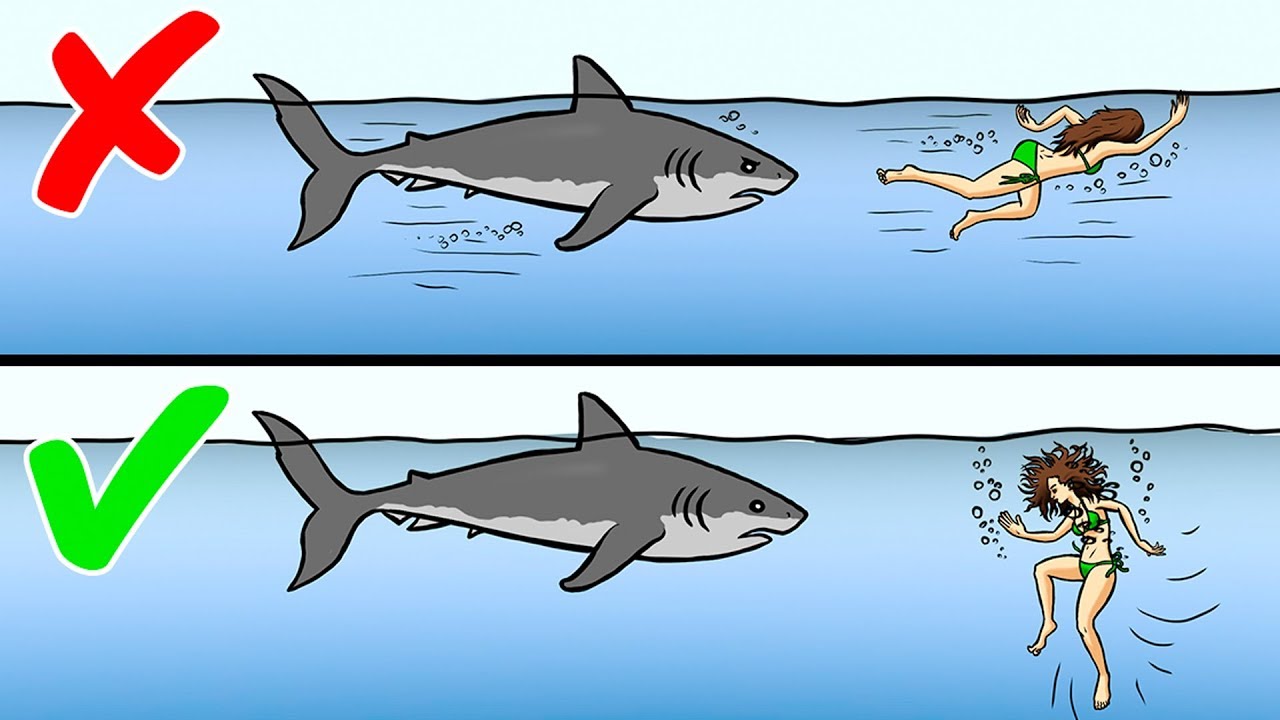
¿Qué consejo se da sobre el uso de Wi-Fi y Bluetooth cuando no se está utilizando el smartphone?
-Se recomienda apagar los ajustes de Wi-Fi y Bluetooth cuando no se estén utilizando, ya que pueden dejar el dispositivo vulnerable a varios ataques.
¿Por qué no se debe confiar en las redes Wi-Fi abiertas y cómo protegerse al usarlas?
-No se debe confiar en las redes Wi-Fi abiertas porque cualquiera con conocimientos técnicos puede configurar una y robar datos privados. Para protegerse, se debe usar una VPN para proporcionar una conexión segura.
¿Qué riesgos implican instalar aplicaciones desde fuentes no oficiales y cómo evitarlos?
-Las aplicaciones crackeadas o modificadas de fuentes no oficiales siempre contienen algún tipo de malware o spyware. Para evitarlos, nunca se deben instalar aplicaciones desde fuera de la tienda de aplicaciones oficial como Google Play Store.
¿Qué se recomienda hacer si se sospecha que un smartphone está infectado con spyware?
-Si se sospecha que un smartphone está infectado con spyware, se recomienda hacer un restablecimiento de fábrica y comenzar de nuevo.
¿Por qué es importante hacer copias de seguridad de los datos del smartphone y cómo protegerlas?
-Es importante hacer copias de seguridad de los datos en un disco duro cifrado y no depender solo de almacenamiento en la nube, ya que estos pueden ser fácilmente accedidos por hackers.
¿Qué estrategia se sugiere para manejar contraseñas de cuentas en línea y por qué?
-Se sugiere no usar la misma contraseña en todas las cuentas y usar un administrador de contraseñas como Bitwarden para generar y guardar contraseñas únicas para cada cuenta, asegurando que estén almacenadas en una base de datos cifrada.
¿Qué es la autenticación de dos factores y por qué es esencial habilitarla en las cuentas en línea?
-La autenticación de dos factores (2FA) es una capa adicional de seguridad que requiere más que solo una contraseña para acceder a una cuenta. Es esencial habilitarla para proteger las cuentas en línea contra intentos de acceso no autorizados.
¿Cómo ayuda a proteger la privacidad y la seguridad digital ajustando la configuración de privacidad en las redes sociales?
-Ajustar la configuración de privacidad en las redes sociales limita la exposición de información personal, lo que reduce el riesgo de inteligencia abierta y ataques de ingeniería social.
Outlines

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنMindmap

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنKeywords

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنHighlights

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنTranscripts

هذا القسم متوفر فقط للمشتركين. يرجى الترقية للوصول إلى هذه الميزة.
قم بالترقية الآنتصفح المزيد من مقاطع الفيديو ذات الصلة
5.0 / 5 (0 votes)