Network Traffic Anomaly Detection Using Machine Learning
Summary
TLDRIn this presentation, Magna Kri and teammates Vijay, Wami, and Graa discuss their project on network traffic anomaly detection using machine learning. The team introduces the need for adaptive security systems in response to cyber threats. They demonstrate the use of K-means clustering and other machine learning techniques to detect anomalies in network traffic data, focusing on packet sizes and IP addresses. The presentation covers code implementation, methodology, challenges faced, results, and future work, emphasizing the need for advanced, real-time monitoring to combat evolving cyber threats effectively.
Takeaways
- 📡 The presentation focuses on network traffic anomaly detection using machine learning to enhance network security.
- 📊 Key sections of the presentation include introduction, methodology, code demonstration, results, challenges, future work, and references.
- 🔒 Cybersecurity challenges arise from evolving technologies and sophisticated cyber attacks targeting network vulnerabilities.
- 💻 Machine learning is being utilized to identify subtle network traffic anomalies, offering adaptive threat detection.
- 📈 K-means clustering is the primary algorithm used for detecting anomalies in network traffic, analyzing packet size, IP addresses, and other features.
- 🔧 The code demonstration highlights Python-based anomaly detection, employing machine learning techniques such as eigenvalues, eigenvectors, and data normalization.
- 📉 The team utilized clustering models, including K-means and DBSCAN, to categorize network traffic data and identify anomalies.
- 📉 Results show the model effectively detecting anomalies with a purity of 95%, although challenges with data quality and scalability remain.
- ⚙️ Future work includes improving data quality, adopting more advanced techniques, enabling real-time monitoring, and explaining AI decision-making.
- 🔍 The conclusion emphasizes the importance of machine learning in improving cybersecurity and detecting network anomalies, with continuous improvement necessary to keep up with evolving cyber threats.
Q & A
What is the main objective of the project discussed in the transcript?
-The main objective of the project is to develop a comprehensive network traffic anomaly detection system using state-of-the-art machine learning techniques to detect potential cyber threats by identifying anomalies in network traffic patterns.
Why are traditional security measures like firewalls insufficient for modern network security?
-Traditional security measures such as firewalls and intrusion detection systems rely on predefined rules and signatures, making them vulnerable to sophisticated attacks that use evasion tactics. Additionally, as networks grow in complexity, manually updating rules becomes more difficult.
How do machine learning techniques improve network anomaly detection?
-Machine learning algorithms learn patterns inherent in network traffic data and can detect subtle deviations from normal behavior, allowing for more adaptive and dynamic threat detection. This enables identification of potential security breaches or performance anomalies.
What machine learning technique is used in the project for anomaly detection?
-The project uses K-means clustering, an unsupervised machine learning technique that groups data points into clusters based on features such as packet size and IP address. Deviations from normal clusters are flagged as potential anomalies.
What role do eigenvalues and eigenvectors play in the project’s anomaly detection process?
-Eigenvalues and eigenvectors are used to analyze the properties of the Laplacian matrix in the network, helping identify the underlying structure of the network traffic data. This allows the system to detect important features and patterns in the data.
What are some of the challenges mentioned in detecting anomalies in network traffic?
-Challenges include dealing with messy data (e.g., missing values, outliers), handling large volumes of data in real-time, and ensuring the anomaly detection system can effectively keep up with evolving cyber threats.
What are the future improvements suggested for the project?
-Future improvements include enhancing data quality, exploring advanced machine learning techniques, implementing real-time monitoring, and focusing on explainable AI to better understand and interpret the system's decisions.
What clustering evaluation metrics were used to assess the quality of the K-means clusters?
-The evaluation metrics used include purity, recall, F1 score, and entropy. These metrics help assess the effectiveness of the clustering, with high purity indicating good clustering and low entropy reflecting less randomness.
How was the K-means algorithm implemented in the project’s code?
-The K-means algorithm was implemented by initializing centroids, assigning data points to the nearest centroid based on Euclidean distance, recalculating the centroids, and repeating this process until convergence. The model was run for different values of K (e.g., 7 and 15) to find the optimal number of clusters.
How are anomalies detected using the clustering results?
-Anomalies are detected by identifying data points that are far from the centroids of the clusters. These points are likely to represent abnormal network traffic and are flagged for further investigation to determine if they are malicious.
Outlines

此内容仅限付费用户访问。 请升级后访问。
立即升级Mindmap

此内容仅限付费用户访问。 请升级后访问。
立即升级Keywords

此内容仅限付费用户访问。 请升级后访问。
立即升级Highlights

此内容仅限付费用户访问。 请升级后访问。
立即升级Transcripts

此内容仅限付费用户访问。 请升级后访问。
立即升级浏览更多相关视频
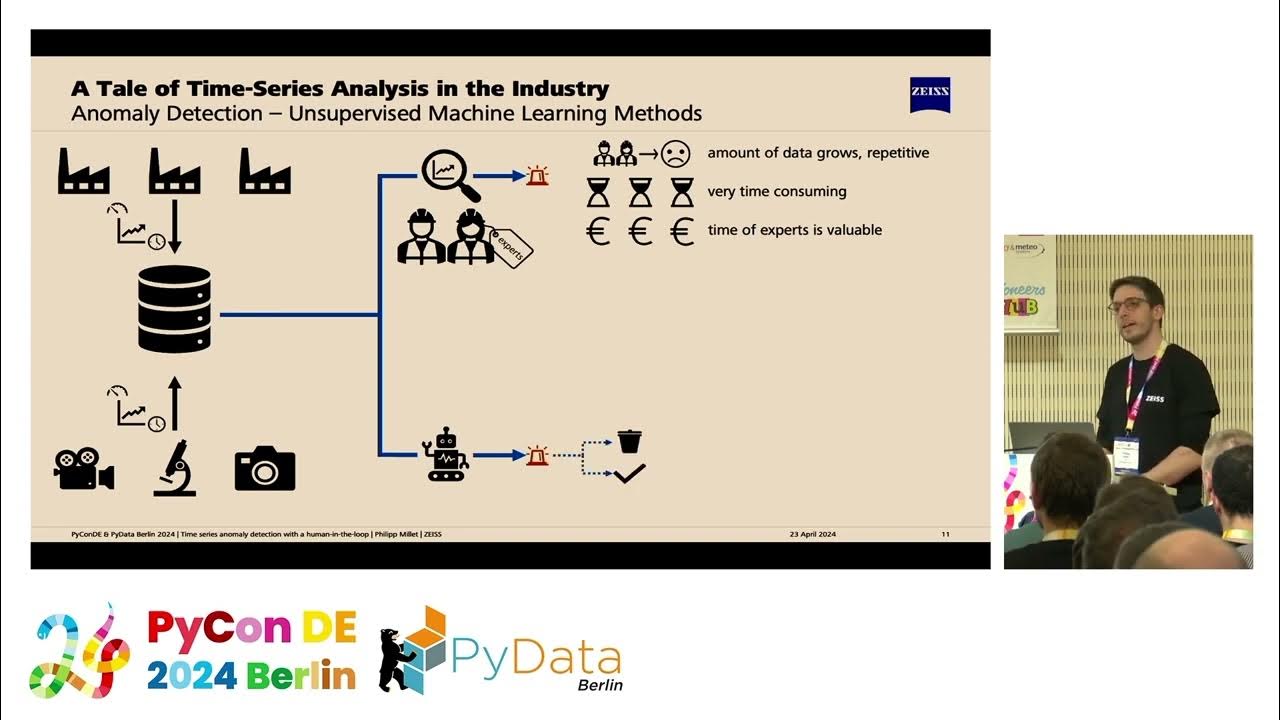
Time series anomaly detection with a human-in-the-loop [PyCon DE & PyData Berlin 2024]

#7 Machine Learning Specialization [Course 1, Week 1, Lesson 2]

Lecture 06: Exploring Unsupervised Learning: From Clustering to Anomaly Detection

Introduction to Embedded Machine Learning 2.4.1 - Anomaly Detection

NanoEdge AI Studio V3 - Anomaly Detection demo

Full Stack Network Intrusion Detection System Using Machine Learning With Code and Documents
5.0 / 5 (0 votes)
