SCADA Hacking | Operational Technology (OT) Attacks
Summary
TLDRThis video script delves into the vulnerabilities of operational technology, focusing on attacks targeting the Modbus TCP protocol used in industrial control systems. It explains the role of SCADA, RTUs, PLCs, and HMIs in managing infrastructure processes and highlights the risks of malicious activities, such as traffic sniffing and memory manipulation, which can lead to severe operational disruptions. The script also outlines a practical lab setup using VMware, Kali Linux, and Modbus Power, demonstrating how attackers can exploit these systems, emphasizing the critical need for robust cybersecurity measures.
Takeaways
- 🔬 Operational Technology (OT) is a combination of hardware and software that monitors and controls physical devices and industrial processes.
- 🌐 Industrial Control Systems (ICS) are a type of OT that manage infrastructure processes like oil and gas transportation, power plants, and traffic control.
- 🔩 Key components of ICS include SCADA (Supervisory Control and Data Acquisition), RTU (Remote Terminal Unit), PLC (Programmable Logic Controller), and HMI (Human-Machine Interface).
- 📡 SCADA acts as a centralized controller for RTUs and PLCs, allowing operators to monitor and control industrial systems.
- 🔌 Modbus protocol is a communication protocol used between SCADA and control devices, with two types: Modbus RTU for serial communication and Modbus TCP for TCP/IP.
- 💡 In Modbus, SCADA functions as the master device capable of performing read and write operations on slave devices, which are typically RTUs or PLCs.
- 🕵️♂️ Attackers can exploit vulnerabilities in Modbus TCP by sniffing traffic with tools like Wireshark and performing replay attacks.
- 🔍 To simulate a Modbus slave device, a tool like Modbus Power can be used, which allows for the creation and configuration of a virtual slave with registers and coils.
- 🛠️ Metasploit Framework can be used to identify and exploit Modbus vulnerabilities, with modules available for tasks such as finding unit IDs and performing read/write operations on slave devices.
- 📚 Understanding the structure and function of Modbus slaves, including their memory and registers, is crucial for both defending against and conducting attacks on industrial systems.
- ⚠️ Changes made to the values in Modbus slave devices can have serious implications for the operation of critical systems, potentially causing major problems.
Q & A
What is operational technology?
-Operational technology is a combination of hardware and software that monitors and controls physical devices and industries, such as industrial control systems (ICS).
What is an Industrial Control System (ICS)?
-An Industrial Control System (ICS) is a collection of devices, programs, and networks used to manage industrial infrastructure processes, including transportation of oil and gas, power plants, and traffic control.
What are the types of devices that can be part of an ICS?
-Some of the types of devices in an ICS include SCADA (Supervisory Control and Data Acquisition), RTU (Remote Terminal Unit), PLC (Programmable Logic Controller), and HMI (Human-Machine Interface).
How does a SCADA system interact with RTUs and PLCs?
-A SCADA system acts as a centralized controller that can read and write operations on RTUs and PLCs, which are referred to as slaves in the Modbus protocol.
What is the Modbus protocol and its two types?
-The Modbus protocol is a communication protocol used for a master device to perform read and write operations on slave devices. It has two types: Modbus RTU, which uses serial communication, and Modbus TCP, which uses TCP/IP.
On which port does the Modbus protocol operate?
-The Modbus protocol operates on port 502.
What kind of attacks can a malicious user perform on a Modbus network?
-A malicious user can perform attacks such as sniffing the traffic between the SCADA and controlling devices, performing replay attacks, and spoofing as a master device to read and write to the memory of the slave devices.
What is the purpose of the lab setup mentioned in the script?
-The lab setup is used to simulate an attack on a Modbus TCP protocol. It involves using VMware with Kali Linux as the attacker machine and Ubuntu as the target machine running a simulated slave device using Modbus Power.
How can an attacker find a target slave device in a network?
-An attacker can use a tool like Nmap to scan the subnet and look for IP addresses with port 502 open, which might indicate a target slave device.
What is Metasploit Framework and how is it used in the context of the script?
-Metasploit Framework is a tool used for developing and executing exploit code against a remote target machine. In the script, it is used to search for and utilize modules related to Modbus, such as finding unit IDs and performing read and write operations on the target slave.
What is the potential impact of an attacker changing the values in the registers of a slave device?
-Changing the values in the registers of a slave device can cause major problems on the target system, as these values perform critical tasks in the operation of the industrial infrastructure.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

IoT Protocols | MQTT | CoAP | OPC-UA | Modbus | LoRA | Industrial Automation IIoT
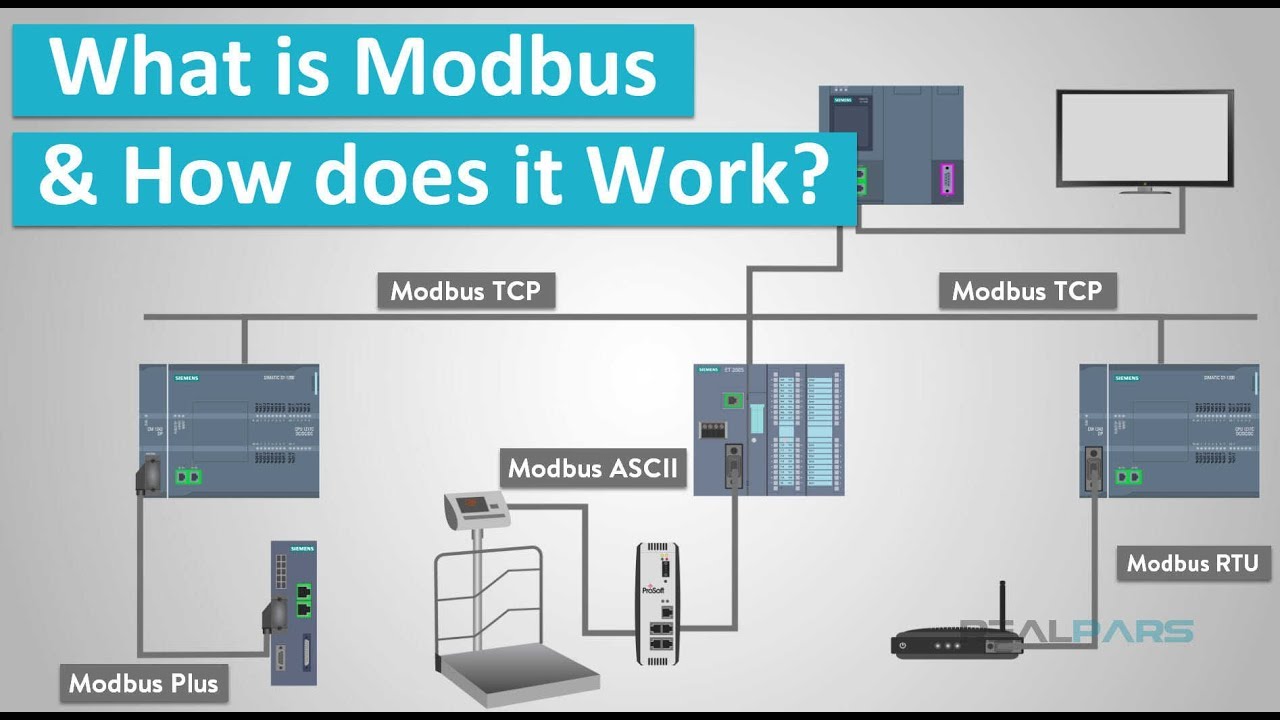
What is Modbus and How does it Work?
DISTRIBUTE CONTROL SYSTEM (DCS) SISTEM KONTROL TERDISTRIBUSI - DALAM OTOMASI INDUSTRI

Why do downloads look like waves?

5.7 - Pressure Control Valves

G500-4004 l G500/G100 Configure Network Communications v1
5.0 / 5 (0 votes)