Encryption Technologies - CompTIA Security+ SY0-701 - 1.4
Summary
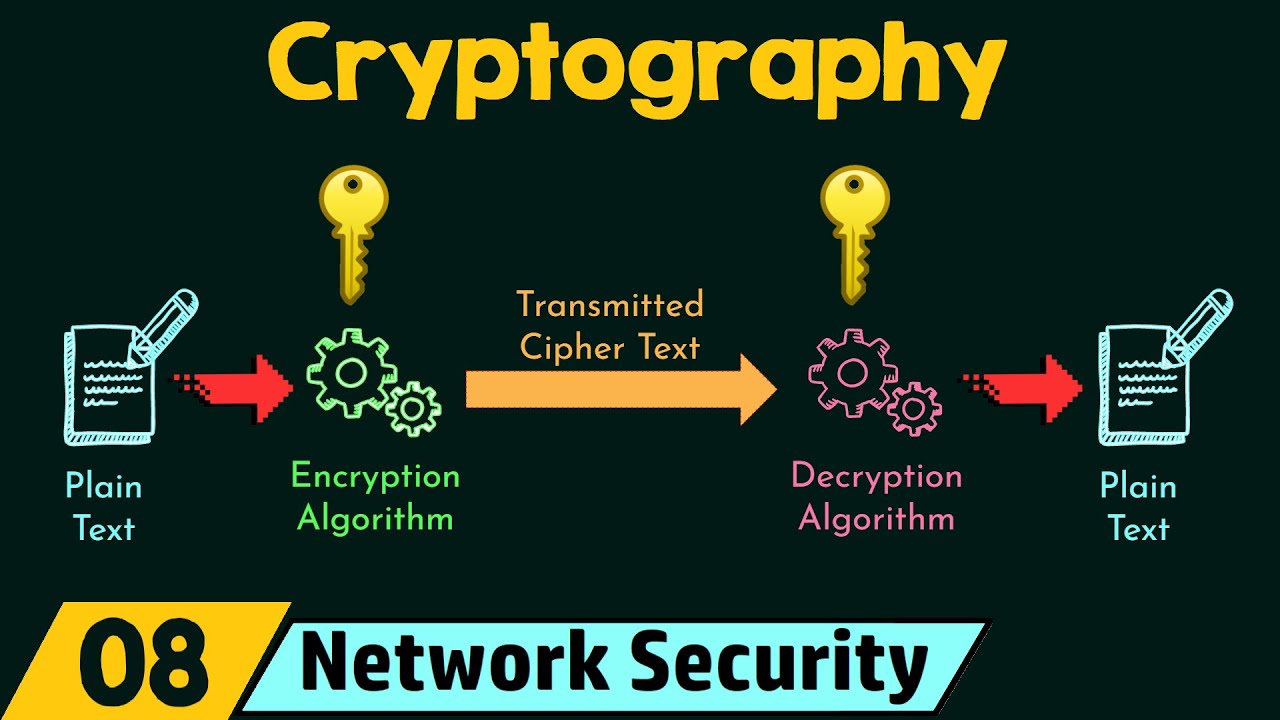
TLDRThe script delves into the world of cryptographic security, starting with the Trusted Platform Module (TPM), a hardware component for individual devices that generates and securely stores cryptographic keys. It then moves to the larger scale, discussing the use of Hardware Security Modules (HSMs) in data centers for managing encryption keys across numerous devices, highlighting their redundancy and efficiency. The importance of centralized key management systems is underscored, which allows for the oversight and rotation of keys, ensuring security and compliance. Additionally, the script touches on the challenges of maintaining data privacy across multiple systems and introduces the concept of a secure enclave, a dedicated security processor designed to protect data privacy even in compromised environments.
Takeaways
- 🛡️ A Trusted Platform Module (TPM) is a hardware component on a motherboard that provides cryptographic functions, including secure key generation and storage.
- 🔑 TPMs have persistent memory for storing unique machine-specific keys, which is beneficial for full-disk encryption and other secure key needs.
- 🔒 The keys stored in a TPM are password protected, making brute force or dictionary attacks ineffective for unauthorized access.
- 🚀 For large-scale cryptographic needs in data centers, a Hardware Security Module (HSM) is used, often in a clustered and redundant setup for high availability.
- 🔒 HSMs are designed for secure key storage and fast cryptographic functions, with separate hardware for real-time encryption and decryption in large-scale environments.
- 🔄 Centralized key management systems allow for the management of various keys from a single console, keeping keys separate from the data they protect.
- 🔄 Automatic key rotation can be set up through key management systems to ensure ongoing security by regularly changing keys.
- 📊 Key management systems provide logging, reporting, and dashboards for monitoring key usage, expiration, and other relevant details.
- 📱 Secure enclaves are security processors built into devices like mobile phones and laptops, dedicated to protecting data privacy.
- 🛡️ Secure enclaves have their own boot ROM, true random number generator, and built-in cryptographic keys for robust data protection.
- 🔐 The secure enclave's hardware-based AES encryption ensures real-time data protection as it moves in and out of memory.
Q & A
What is a Trusted Platform Module (TPM) and what is its primary function?
-A Trusted Platform Module (TPM) is a standardized hardware component on a modern motherboard designed to provide cryptographic functions for a computer, such as generating random numbers or keys, and securely storing them for use in processes like full-disk encryption.
How does TPM's persistent memory contribute to key security?
-TPM's persistent memory allows for the creation and storage of keys that are unique to the machine, providing a secure way to store cryptographic keys locally, which is particularly useful for secure key generation and encryption purposes.
What is the main difference between a TPM and a Hardware Security Module (HSM)?
-While a TPM provides encryption functions for a single device, an HSM is designed for large-scale cryptographic use in data centers, often clustered together for redundancy and high availability, and is used to securely store and manage encryption keys for hundreds or thousands of devices.
Why are Hardware Security Modules (HSMs) preferred for large-scale cryptographic functions?
-HSMs are preferred for large-scale cryptographic functions because they can perform these functions in the hardware itself, which is more efficient, and they can be equipped with separate plug-in cards or hardware designed for very fast cryptographic operations.
How does a centralized key management system help in managing different types of keys?
-A centralized key management system allows for the management of all different types of keys from a single console, keeping the keys separate from the data they protect, and enabling features like automatic key rotation, logging, and reporting.
What is the purpose of automatic key rotation in a key management system?
-Automatic key rotation is a security measure that ensures keys are constantly changing over time, reducing the risk of unauthorized access and enhancing the overall security of the system.
What information can be found on the dashboard of a key management system?
-The dashboard of a key management system provides a summary of the types of keys being used, details about certificate authorities, certificate expiration dates, license information, and more.
How does a secure enclave contribute to data privacy?
-A secure enclave is a dedicated security processor that manages and monitors system processes, especially during the boot process, and performs real-time encryption of data as it moves in and out of memory, ensuring data privacy even if the device falls into the wrong hands.
What are some of the features of a secure enclave that enhance data privacy?
-Features of a secure enclave include a separate boot ROM, a true random number generator, built-in cryptographic keys that cannot be changed, and hardware-based AES encryption.
How does the use of a secure enclave address the challenges of maintaining data privacy across multiple systems?
-A secure enclave addresses these challenges by providing a separate secure processor that ensures data privacy through real-time encryption and secure key management, regardless of where the data is stored or accessed.
What is the significance of having a true random number generator in a secure enclave?
-A true random number generator in a secure enclave is significant as it provides a source of randomness that is essential for generating secure cryptographic keys, enhancing the overall security of the system.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade Now5.0 / 5 (0 votes)