This Obscure Maths Will Revolutionize Data Privacy
Summary
TLDRThe video script discusses the potential of fully homomorphic encryption (FHE) in the context of big data and AI, highlighting its ability to enable data analysis without compromising privacy. FHE allows computations on encrypted data, with results that can only be decrypted by the data owner. Despite its theoretical existence since the 1970s, the technology is computationally intensive and has been slow to adopt. Recent developments include specialized chips from companies like Intel, Chain Reaction, and Fabric Cryptography, aiming to make FHE more practical for applications such as secure health data analysis and scientific research, potentially revolutionizing how sensitive data is handled in the face of stringent privacy regulations.
Takeaways
- 🌟 Big data laid the foundation for the current hype of artificial intelligence (AI), which has immense untapped potential.
- 🔒 Privacy concerns are a major obstacle in utilizing AI for analyzing sensitive health data and other personal information.
- 🔐 Fully homomorphic encryption (FHE) is a revolutionary technology that enables computation on encrypted data without compromising privacy.
- 🤔 FHE allows encrypted data to be processed and returns an encrypted result that only the data owner can decrypt and read.
- 📈 The concept of homomorphic encryption has been around since the 1970s, but it was only proven feasible in 2009 by Craig Gentry.
- 🚧 Despite its potential, FHE has not been widely adopted due to its high computational cost and the complexity of the encryption methods.
- 💻 Lattice cryptography is the approach used in current FHE methods, which produces very long strings that are challenging for standard CPUs and GPUs.
- 🔋 Specialized computer chips are being developed by companies like Intel, Chain Reaction, and Fabric Cryptography to support FHE more efficiently.
- 🏥 FHE could significantly benefit scientific research by enabling analysis of data currently restricted due to privacy regulations.
- 🌍 The adoption of FHE could allow companies to be trusted with sensitive data, as exemplified by the British National Health Service's collaboration with Palantir.
- 📚 Homomorphisms on algebraic rings, the mathematical basis of FHE, demonstrate the practical applications of an active area of research in modern technology.
Q & A
What is the main obstacle in harnessing the full potential of artificial intelligence due to big data?
-The main obstacle is privacy concerns, as using AI to analyze personal data like health records could save lives but requires sharing extremely personal information.
How does new encryption technology address the privacy issue in AI data analysis?
-New encryption technology, specifically fully homomorphic encryption, allows for computations on fully encrypted data and returns an encrypted result that only the data owner can decrypt, thus preserving privacy.
What is fully homomorphic encryption and how does it relate to homomorphisms in mathematics?
-Fully homomorphic encryption is a type of encryption that allows computations on encrypted data. It is related to homomorphisms, which are mathematical operations that preserve the relations of the structures they act upon.
Who is Craig Gentry and what is his contribution to the field of homomorphic encryption?
-Craig Gentry is an American computer scientist who proved the possibility of fully homomorphic encryption and developed an encryption scheme in 2009.
Why hasn't fully homomorphic encryption been widely adopted yet?
-It hasn't been widely adopted because the computational process is extremely expensive, slow, and energy-intensive due to the use of lattice cryptography and the production of very long strings.
What are some companies and institutions working on specialized chips for homomorphic encryption?
-Companies like Intel, working with DARPA, the Korean Electronics and Telecommunications Research Institute, and startups such as Chain Reaction and Fabric Cryptography are developing specialized chips for this purpose.
What is the significance of developing specialized computer chips for homomorphic encryption?
-Specialized chips can handle the complex computations required for homomorphic encryption more efficiently, making it practical for real-world applications and enabling companies to securely process encrypted data.
How could fully homomorphic encryption benefit scientific research?
-It could allow researchers to analyze data that is currently restricted due to privacy regulations, enabling new insights and discoveries without compromising individual privacy.
What is the status of the specialized chips mentioned in the script?
-Fabric Cryptography claims to have a chip ready for mass production, Intel's chip is almost ready, and the Korean ETRI states it already has a chip available.
How does the development of fully homomorphic encryption exemplify the practical use of mathematics?
-It demonstrates how abstract mathematical concepts, like homomorphisms on algebraic rings, can be applied to solve real-world problems, such as data privacy in AI and scientific research.
What is the relevance of homomorphic encryption in the context of quantum computing?
-The encryption scheme is so complex that it is considered safe from cracking even by quantum computers, which are expected to break many current encryption methods.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

Sistem Keamanan Cerdas - Pertemuan 14 1

ZeeStar: Private Smart Contracts by Homomorphic Encryption and Zero-knowledge Proofs

How Federated Learning works? Clearly Explained|

How to use Live Context with Pieces Copilot+ in Obsidian

The Future Of Health Insurance - The Medical Futurist
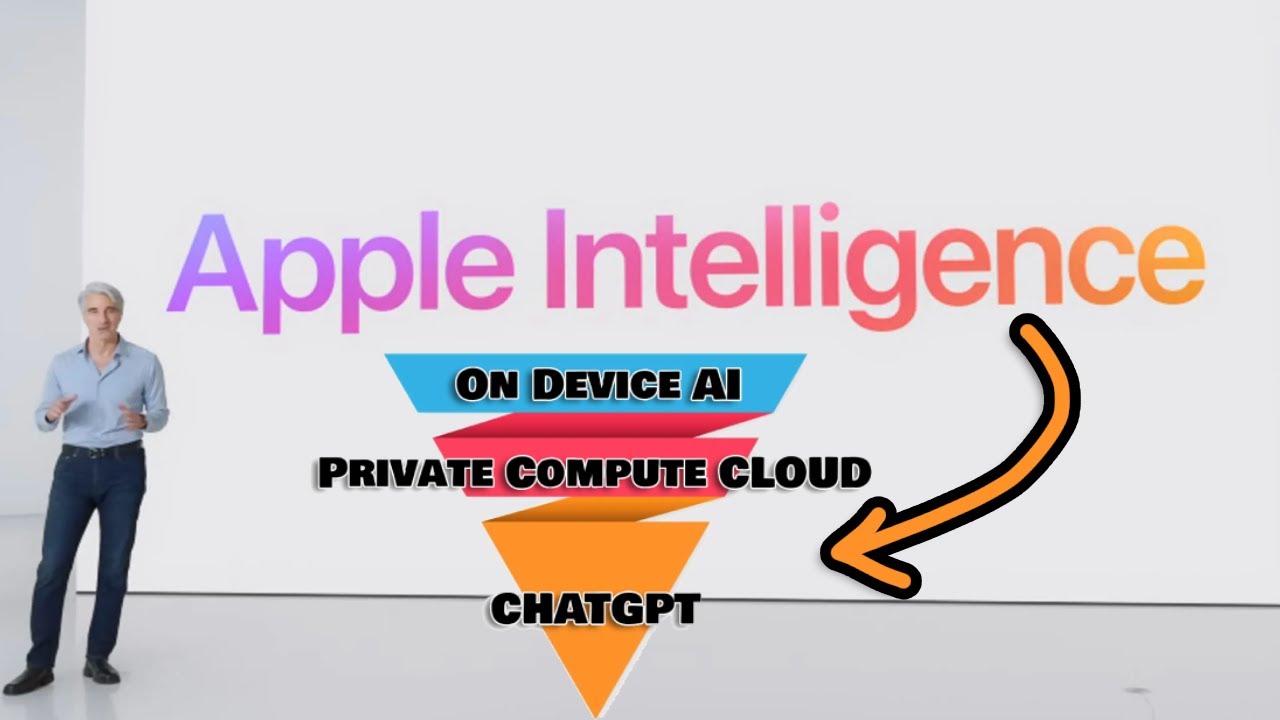
Apple's Surprise "AI" Punch!
5.0 / 5 (0 votes)