Cloud-native authorization standards
Summary
TLDROmary Gazit, CEO of Certo, delves into fine-grained authorization, contrasting it with authentication. He highlights the lack of standards in authorization, leading to security vulnerabilities, and emphasizes the need for centralized, fine-grained access control. Gazit discusses the evolution from coarse-grained roles to attribute and relationship-based models, advocating for policy-based access management. He introduces tools like Open Policy Agent and Topaz, promoting real-time, local authorization integrated with centralized policy management. Gazit concludes with the 'Five Laws of Authorization' for building robust systems, offering open-source projects and Certo's commercial solutions for streamlined implementation.
Takeaways
- 😀 Omary Gazit, the co-founder and CEO of Certo, has over three decades of experience in software development, with a focus on cloud platforms, identity, and access.
- 🔐 Authentication and authorization are distinct processes; authentication verifies identity, while authorization determines what an authenticated user can do within an application.
- 🛠 The authentication ecosystem is mature with established standards like SAML and OAuth, whereas authorization lacks such standards and often results in inconsistent implementations.
- 🚨 Broken access control is a significant security issue, ranking top on the OWASP Top 10 list, with 94% of tested applications having vulnerabilities.
- 📈 Modern best practices for authorization include centralizing it through purpose-built services, implementing fine-grained access control, and separating authorization logic from application code.
- 🔗 Relationship-based access control (RBAC) and attribute-based access control (ABAC) are evolving models that provide more nuanced permission settings compared to traditional access control lists (ACLs).
- 📝 Policy-based access management involves externalizing authorization logic into a domain-specific language, allowing for better management and versioning of access control policies.
- 🌐 Real-time access control is crucial for performance and availability, necessitating a local call to an authorization service for every access request.
- 🔄 The 'Five Laws of Authorization' include being fine-grained, policy-based, real-time, centrally managed, and having aggregated decision logs for compliance and forensics.
- 💡 Certo offers commercial solutions for authorization, and Gazit encourages exploring open-source projects like OPA and Topaz for building robust authorization systems.
Q & A
What is the main difference between authentication and authorization?
-Authentication is about proving that you are who you say you are, often using methods like emails, passwords, biometrics, or two-factor authentication. Authorization, on the other hand, is about determining what a logged-in user is allowed to do within an application, specifically whether a user has certain permissions on a particular resource.
Why is fine-grained authorization important?
-Fine-grained authorization is crucial for security because it adheres to the principle of least privilege, limiting user permissions to the minimum necessary for their tasks. This minimizes the damage potential from compromised identities and helps maintain a secure and consistent authorization surface area across applications.
What is the significance of the OAuth and OpenID Connect standards in authentication?
-OAuth and OpenID Connect are significant standards in authentication because they provide a mature ecosystem for implementing single sign-on and access delegation. They have been around for almost 20 years, with OpenID Connect being around for about nine years, and they are widely used to enable login without the need for developers to write their own authentication code.
What are the common issues with current authorization implementations?
-Current authorization implementations often suffer from a lack of consistency, leading to security vulnerabilities, such as broken access control, which is the number one issue on the OWASP Top 10 list. Additionally, the lack of standards results in each microservice implementing permissions differently, creating a complex and hard-to-manage authorization landscape.
What is the role of centralization in authorization?
-Centralization in authorization involves creating a single, consistent implementation that can be used across all microservices, reducing the risk of security vulnerabilities and making it easier to manage and reason about the authorization surface area of an application.
How does the principle of least privilege relate to authorization?
-The principle of least privilege in authorization means giving users only the permissions they need to perform their tasks, and no more. This minimizes the potential damage from a compromised identity and is a key reason for implementing fine-grained access control.
What is the difference between 'authorization spaghetti code' and extracting authorization logic?
-Authorization spaghetti code refers to the practice of having numerous if and switch statements scattered throughout microservices, making it difficult to manage and reason about. Extracting authorization logic involves separating this logic from the application code and storing it in a centralized manner, which aligns with the security principle of separation of duties.
Why is real-time access control important in authorization?
-Real-time access control is important because it allows for dynamic decision-making based on the most current data, which is crucial for security. It enables permissions to be checked right before granting access to a protected resource, ensuring that the decision is based on up-to-date information.
What are the 'Five Laws of Authorization' mentioned in the script?
-The 'Five Laws of Authorization' include: 1) Be fine-grained and flexible, 2) Be policy-based, 3) Ensure real-time local authorization, 4) Centrally manage policies and data, and 5) Aggregate and centralize decision logs for compliance and forensics.
How does the Topaz project relate to the concepts discussed in the script?
-The Topaz project is an open-source solution that combines the decision engine from the Open Policy Agent (OPA) with a Zanzibar-like directory model. It aims to offer a fast, flexible, and easy-to-use authorization system that supports various access control models and is designed to be used in any cloud environment.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video
Secure Your Microservices with Keycloak | OAuth2 & JWT | Spring Cloud Gateway

Authentication, Authorization, and Accounting - CompTIA Security+ SY0-701 - 1.2
Oauth2 JWT Interview Questions and Answers | Grant types, Scope, Access Token, Claims | Code Decode
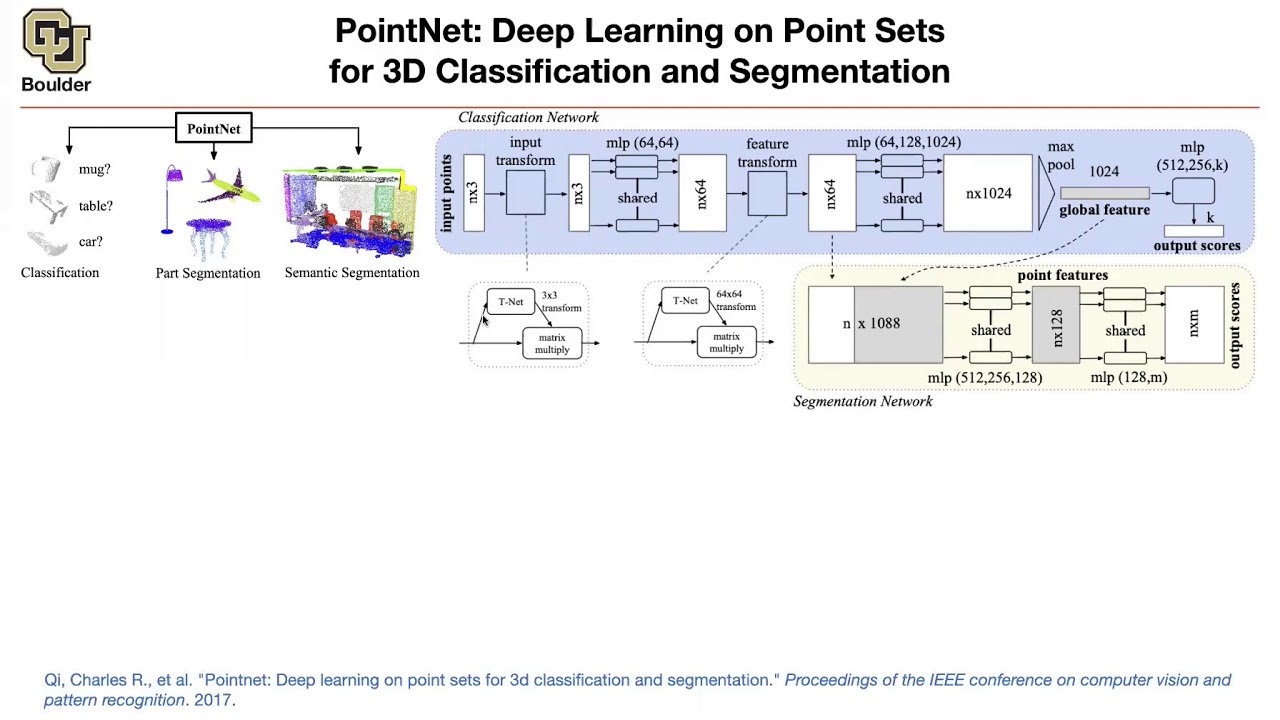
PointNet | Lecture 43 (Part 1) | Applied Deep Learning

4 - AAA (Authentication - Authorization - Accounting) Security+ SY0-701 - عربي

KEAMANAN JARINGAN | 3.4 Memahami Fungsi dan Cara Kerja Server Autentikasi
5.0 / 5 (0 votes)