How To Become Invisible Online
Summary
TLDRDieses Video bietet umfassende Informationen, um im Internet unsichtbar zu werden. Es erklärt die notwendigen Tools und deren Funktionen, stellt drei Anonymitätslevel vor und zeigt, wie man sie implementieren kann. Es deckt alles von starken Passwörtern und mehrstufiger Authentifizierung bis hin zur Nutzung des Tor-Browsers und verschlüsselter Kommunikationstools ab. Lernen Sie, wie Sie Ihre Online-Spuren minimieren und Ihre Privatsphäre schützen, ohne auf Bequemlichkeit zu verzichten.
Takeaways
- 😎 Anonymität im Internet kann in drei Stufen erreicht werden: Schwierig zu hacken, schwer zu verfolgen und vollkommen unsichtbar.
- 🔒 Die erste Stufe der Anonymität, 'schwierig zu hacken', beinhaltet das Erstellen starker Passwörter, das Zurückhalten persönlicher Informationen und das Erstellen mehrerer E-Mail-Adressen.
- 🔑 Starkes Passwort: Verwenden Sie 25 Zeichen oder mehr und erstellen Sie ein sich erinnernbares Passwort durch die Verwendung von Sätzen oder Liedtexten, die Sie umwandeln können.
- 📬 Mehrere E-Mail-Adressen: Unterteilen Sie Ihre E-Mail-Kommunikation in verschiedene Bereiche des Lebens, um Ihre Online-Sicherheit und -Privatsphäre zu erhöhen.
- 🌐 Verwenden Sie den Tor-Browser, um Ihre IP-Adresse zu maskieren und so Ihre Online-Aktivitäten vor Trackern zu schützen.
- 🔗 VPNs können helfen, Ihre tatsächliche IP-Adresse vor Websites zu verbergen, bieten jedoch keine vollständige Anonymität.
- 🗝️ Passwort-Manager wie Dashlane oder open-source Lösungen wie KeePass können Ihnen helfen, starke Passwörter zu erstellen und zu verwalten.
- 📱 Verwenden Sie verschlüsselte Messaging-Apps wie Signal oder Chat Secure, um Ihre Kommunikation vor Überwachung zu schützen.
- 🎯 Um vollkommen unsichtbar zu sein, müssen Sie auch andere Faktoren berücksichtigen, die Ihre Identität preisgeben könnten, wie Geräteinformationen, Betriebssystem oder Internetverbindung.
- 🛡️ Um die 'Exit-Node-Problematik' von Tor zu umgehen, können Sie einen eigenen Proxy erstellen oder als Proxy fungieren, um Ihre tatsächliche IP-Adresse zu verbergen.
- 🌐 Um völlig unsichtbar zu sein, könnten Sie ein vorbereitetes Smartphone oder Modem mit Vorauszahlung verwenden, um sich über öffentliches WLAN zu verbinden, während Sie sich vor Überwachungskameras schützen.
- 🚫 Wichtig ist, dass Sie keine persönlichen Informationen preisgeben, die Sie mit Ihrer Identität in Verbindung bringen könnten, um eine vollständige Anonymität zu erreichen.
Q & A
Was ist das Hauptziel des Videos?
-Das Hauptziel des Videos ist, den Zuschauern alles zu erklären, was sie brauchen, um sich online unsichtbar zu machen, einschließlich der benötigten Tools und der drei Stufen der Anonymität.
Was bedeutet es, 'vollständig unsichtbar' zu sein?
-Vollständig unsichtbar zu sein bedeutet, dass man keine Spuren im Internet hinterlässt und für niemanden nachverfolgbar ist, was in der Regel nur erforderlich ist, wenn eine Regierungsbehörde einen aktiv sucht.
Wie viele Stufen der Anonymität gibt es und was ist der Unterschied zwischen ihnen?
-Es gibt drei Stufen der Anonymität: Schwierig zu hacken, schwierig zu verfolgen und vollständig unsichtbar. Jede Stufe erhöht die Anonymität und Sicherheit, verlangt jedoch auch mehr Anstrengung und Aufwand.
Was sind die drei Schritte, um 'schwierig zu hacken' zu werden?
-Die drei Schritte sind: Starke Passwörter erstellen, minimale persönliche Informationen preiszugeben und mehrere E-Mail-Adressen zu verwenden.
Warum sollten lange Passwörter verwendet werden?
-Lange Passwörter sind stärker, weil sie schwerer zu knacken sind, da moderne Computer kürzeren Passwörtern gegenüber schneller brechen können.
Was ist ein sichereres Verfahren, um Passwörter zu speichern, als sie in der Notes-App zu notieren?
-Ein sichereres Verfahren ist der Einsatz eines Passwortmanagers, der nicht nur zufälligere Passwörter erstellen kann, sondern sie auch sicher speichern kann.
Was ist der TOR-Browser und wie hilft er dabei, anonym im Internet zu surfen?
-Der TOR-Browser ist ein Tool, das Ihre IP-Adresse randomisiert und End-to-End-Verschlüsselung verwendet, um Ihre Identität vor Websites zu verbergen und Ihre Surfaktivitäten zu verschlüsseln.
Was sind einige der Faktoren, die verwendet werden können, um einen Benutzer im Internet zu identifizieren?
-Faktoren wie IP-Adresse, Gerät, Betriebssystem, Wi-Fi-Verbindung, Internetdienstanbieter, Bildschirmgröße und -auflösung können verwendet werden, um einen Benutzer zu identifizieren.
Was ist das 'Exit-Node-Problem' im Zusammenhang mit TOR und wie kann es behoben werden?
-Das Exit-Node-Problem bezieht sich auf das letzte Router-Element im TOR-Netzwerk, das Anfragen in Klartext sendet. Um dieses Problem zu beheben, kann man entweder einen eigenen Proxy erstellen oder einen Proxy verwenden, an dem man nicht persönlich ist.
Was sind einige der Maßnahmen, die ergriffen werden können, um eine vollständige Unsichtbarkeit zu erreichen?
-Um vollständig unsichtbar zu sein, kann man Maßnahmen wie den Einsatz eines Proxys, die Verwendung von VPNs, das Bedecken des Gesichts vor Überwachungskameras, das Kaufen von Burner-Telefonen oder 4G-Internet-Modems mit Bargeld und das Verwenden von öffentlichem WLAN ergreifen.
Welche Ressourcen werden am Ende des Videos empfohlen, um mehr über Anonymität im Internet zu lernen?
-Am Ende des Videos werden Ressourcen wie 'The Art of Invisibility' von Kevin Mitnick und Links zu den erwähnten Tools und Methoden empfohlen.
Outlines

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowMindmap

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowKeywords

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowHighlights

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowTranscripts

This section is available to paid users only. Please upgrade to access this part.
Upgrade NowBrowse More Related Video

🧠 Mein Second-Brain-System – Wie ich nie wieder etwas vergesse⎟Werde produktiv & organisiert

D&D Starter Set: Tipps und Tricks für angehende Spielleiter von "Die Drachen der Sturmwrack-Insel"
Frag Fred: Was sind Cookies? | Kindervideos | SRF Kids

So steigerst du SOFORT deine Google Ads Conversions

So baust DU dir ein VERMÖGEN auf in 2024. RICHTIG Investieren - in 3 Schritten, einfach erklärt!
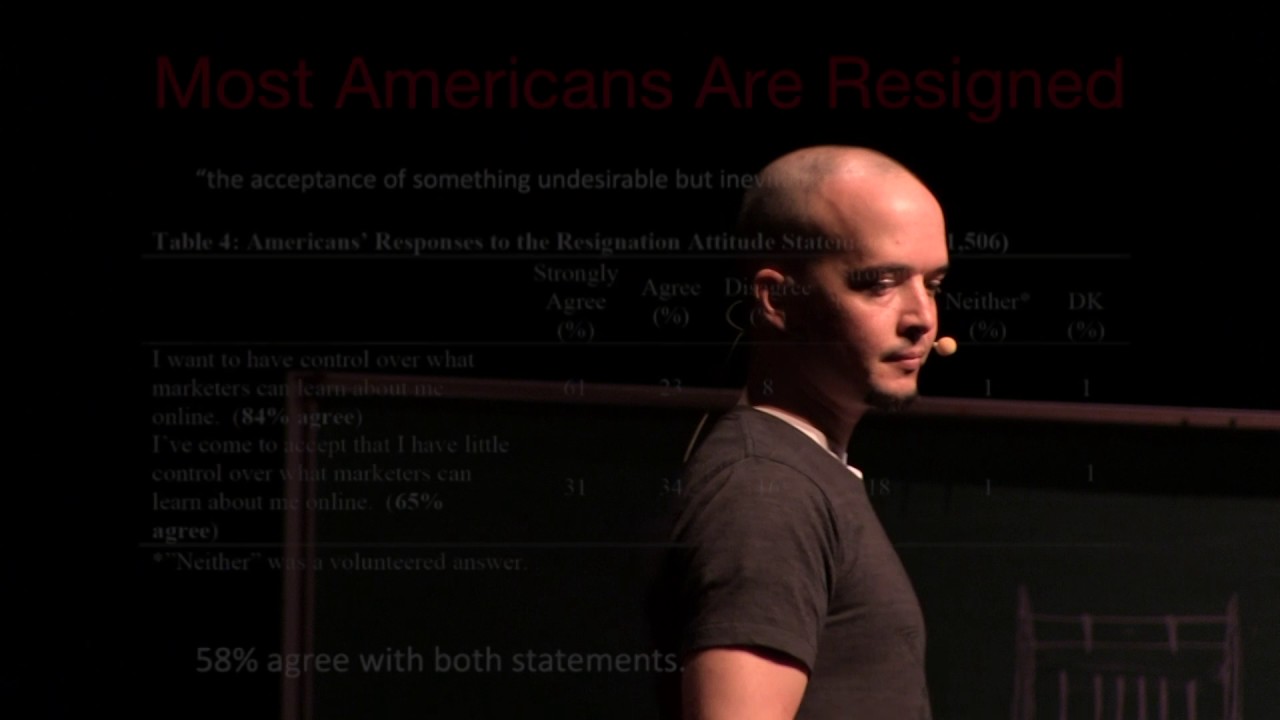
How Online Trackers Track You, and What You Can Do About It | Luke Crouch | TEDxUniversityofTulsa
5.0 / 5 (0 votes)
