SDN, SD-WAN, & SD-Access Simplified... Seriously!
Summary
TLDRIn this informative video, Kevin delves into the realm of software-defined technologies, explaining the concepts of SDN, SD-WAN, and SD-Access. He clarifies how traditional networking devices operate and how SDN centralizes control planes with SDN controllers, enabling intent-based networking. The video explores Cisco's specific solutions like ACI and DNA Center, and how SD-WAN simplifies WAN management with an overlay network. Kevin also introduces SD-Access as an advanced policy enforcement mechanism that replaces traditional ACLs with identity-based access, enhancing security and mobility in networks.
Takeaways
- 🌐 Software-Defined Networking (SDN) centralizes control planes in a controller, allowing for centralized management and intent-based networking.
- 🔄 Traditional networking devices have three planes of operation: data, control, and management, while SDN shifts to a centralized control plane with APIs for device communication.
- 📡 SDN uses southbound interfaces (SBIs) like OpenFlow or Cisco's OpFlex for communication between the controller and network devices.
- 📚 Intent-based networking allows administrators to express their networking intent through applications, which communicate with the controller via northbound interfaces (NBIs).
- 🔍 Cisco's Application Policy Infrastructure Controller (APIC) is used for data center SDN solutions, while Cisco DNA Center is used for enterprise networks.
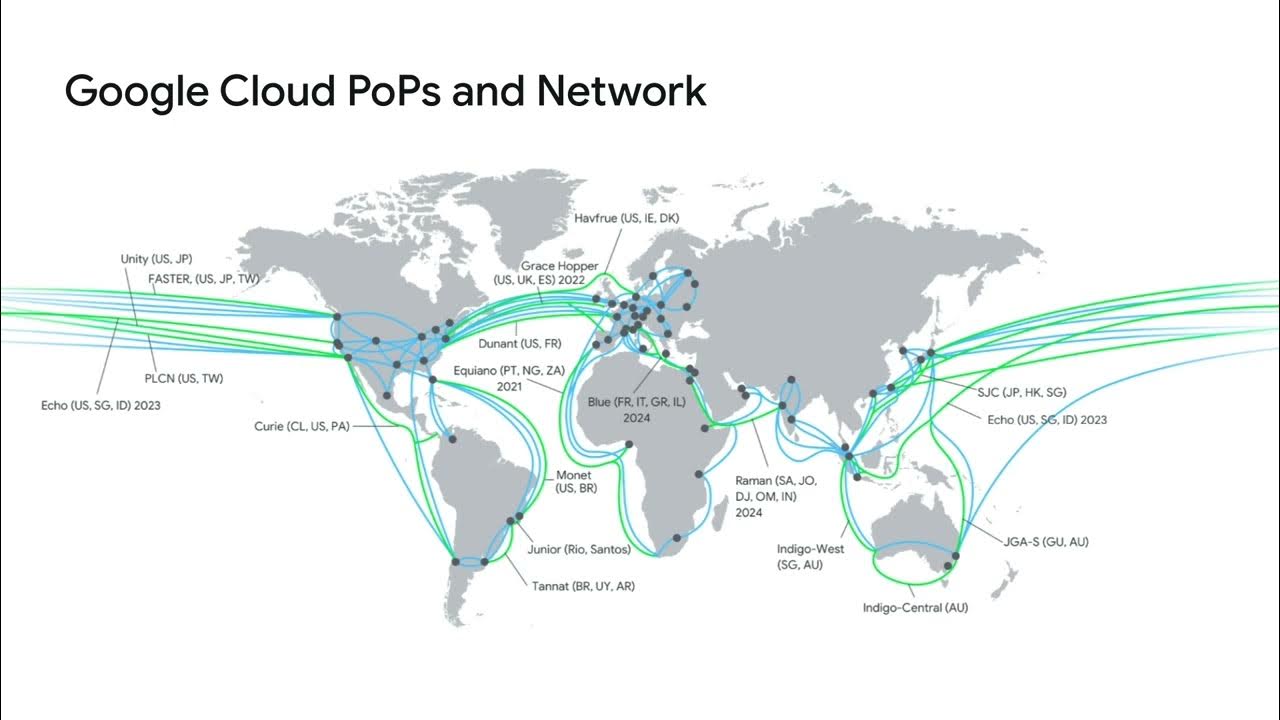
- 🌐 Software-Defined Wide Area Networks (SD-WAN) provide an overlay network on top of the physical infrastructure, simplifying the management of WAN connections.
- 🛠️ SD-WAN allows for direct internet access from remote sites without the need for backhauling to a central location, improving efficiency.
- 🔄 Cisco's SD-WAN solution is based on the Viptela technology they acquired, incorporating components like vManage, vBond, and vSmart for management and control.
- 🔒 SD-WAN supports various WAN technologies and dynamically forms IPSec tunnels for secure traffic forwarding between edge routers.
- 📝 Software-Defined Access (SD-Access) moves beyond traditional ACLs to policy enforcement based on user identity, facilitated by Cisco's Identity Services Engine (ISE).
- 🔑 SD-Access enables the creation of security group ACLs that grant access based on user identity, allowing consistent access regardless of device location within the network.
Q & A
What is meant by the term 'software-defined' in the context of networking?
-'Software-defined' refers to the concept of using software-based controllers or APIs to manage and control hardware devices, such as routers and switches. This approach allows for more flexible, efficient, and scalable network management.
What are the three planes of operation in traditional networking devices?
-The three planes of operation are the data plane, the control plane, and the management plane. The data plane handles the forwarding of packets, the control plane runs algorithms for routing and switching, and the management plane is used for device configuration and management.
How does Software-Defined Networking (SDN) change the traditional networking model?
-SDN centralizes the control plane by using an SDN controller, which runs the control plane algorithms and manages device configurations through APIs. This contrasts with the traditional distributed control plane model where each device has its own control plane.
What is a southbound interface (SBI) in SDN?
-A southbound interface (SBI) is an API used for communication from the SDN controller to the network devices it manages. Examples include OpenFlow and Cisco's proprietary OpFlex.
What is intent-based networking in the context of SDN?
-Intent-based networking allows administrators to specify high-level business goals or 'intents' (such as performance or security requirements) rather than configuring individual devices. The SDN controller translates these intents into device-specific configurations.
What is Cisco's SDN controller for data centers called?
-Cisco's SDN controller for data centers is called the Cisco APIC (Application Policy Infrastructure Controller), which is part of Cisco's ACI (Application Centric Infrastructure).
What are some features of Cisco DNA Center?
-Cisco DNA Center can design network topologies, pre-provision devices, handle day-to-day configurations, monitor network performance, and provide proactive troubleshooting with recommendations based on Cisco TAC knowledge.
What is Software-Defined WAN (SD-WAN) and what benefits does it offer?
-SD-WAN is a technology that uses software-based controllers to manage WAN connections. Benefits include improved cloud application performance, reduced need for backhauling traffic, and the ability to use a variety of WAN technologies with centralized control.
How does Cisco implement SD-WAN?
-Cisco's SD-WAN solution is based on technology from their acquisition of Viptela. It includes components such as vManage for management, vBond for orchestration, and vSmart for control, with edge routers forming secure tunnels for data transport.
What is Software-Defined Access (SD-Access) and how does it enhance traditional access control?
-SD-Access uses identity-based security group ACLs instead of traditional IP-based ACLs. This allows for consistent access policies regardless of device location. It relies on Cisco ISE (Identity Services Engine) for defining identities and policies.
Outlines

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифMindmap

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифKeywords

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифHighlights

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифTranscripts

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифПосмотреть больше похожих видео
5.0 / 5 (0 votes)