Preparing the System Security Plan
Summary
TLDRThis video script provides a comprehensive overview of information security planning and governance. It covers critical aspects such as strategic, operational, and continuity planning, emphasizing the importance of aligning security with business objectives. The script highlights the role of information security governance, risk management, and the development of security policies. It also discusses incident response, disaster recovery, and business continuity planning, offering insights into effective security architecture and design. Additionally, the script stresses the value of security awareness, training, and policy management to safeguard organizational assets and ensure preparedness against various threats.
Takeaways
- 😀 Information security governance aligns security efforts with organizational goals, involving both strategic and operational planning.
- 😀 The CISO plays a crucial role in shifting an organization from a reactive to a proactive cybersecurity approach.
- 😀 Information security governance is a high-level responsibility carried out by the board and executive management, not just IT management.
- 😀 Risk management focuses on taking necessary steps to mitigate risks to information assets and ensuring resources are effectively utilized.
- 😀 Policies such as the Enterprise Information Security Policy define the scope, responsibilities, and acceptable use of organizational resources.
- 😀 Policy management systems help ensure policies are accessible, enforceable, and regularly reviewed to mitigate risks.
- 😀 Security architecture involves implementing controls to protect the confidentiality, integrity, and availability of data across systems.
- 😀 The defense-in-depth strategy uses multiple layers of security to ensure protection even if one layer is compromised.
- 😀 Incident response planning includes identifying threats, containing damage, and recovering from security breaches, with detailed documentation of the process.
- 😀 Disaster Recovery Plans (DRPs) and Business Continuity Plans (BCPs) ensure that essential operations continue during unforeseen disruptions.
- 😀 Regular reviews and updates of security policies and procedures are necessary to stay compliant with evolving regulations and technologies.
Q & A
What are the four major categories of information security planning?
-The four major categories of information security planning are strategic, practical organization, operational, and continuity planning.
What is the role of a CISO in cybersecurity strategy?
-The CISO (Chief Information Security Officer) plays a critical role in shifting an organization from reactive to proactive security, ensuring the company is prepared to respond to various threats.
What is the difference between IT security governance and IT security management?
-IT security governance is a strategic responsibility for setting direction and ensuring alignment with business goals, while IT security management focuses on the practical aspects of implementing security controls.
Why is risk management crucial in information security governance?
-Risk management is crucial because it involves taking necessary steps to identify, manage, and mitigate hazards to information assets, ensuring the security and integrity of the organization’s data.
What is an Enterprise Information Security Policy?
-An Enterprise Information Security Policy defines a company's philosophy on security, setting the scope, direction, and tone for all security efforts within the organization.
What does security architecture focus on?
-Security architecture focuses on how information security controls and safeguards are implemented in IT systems to protect the confidentiality, integrity, and availability of data.
What is the purpose of a defense-in-depth strategy?
-The purpose of a defense-in-depth strategy is to protect an organization's assets by using multiple layers of security, ensuring that if one layer is compromised, additional measures are in place to stop further threats.
How does security training and awareness help reduce security risks?
-Security training educates employees and stakeholders on security best practices, while security awareness ensures they remain vigilant against threats, significantly reducing the risk of security breaches due to human error.
What are the key components of an Incident Response Plan?
-An Incident Response Plan includes detection, reaction, containment, recovery, and damage assessment to manage and mitigate the impact of network security incidents and breaches.
How does a Disaster Recovery Plan (DRP) differ from a Business Continuity Plan (BCP)?
-A Disaster Recovery Plan (DRP) focuses on how an organization can resume operations after a disaster, while a Business Continuity Plan (BCP) ensures that essential functions continue during and after an unplanned event.
Outlines

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифMindmap

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифKeywords

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифHighlights

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифTranscripts

Этот раздел доступен только подписчикам платных тарифов. Пожалуйста, перейдите на платный тариф для доступа.
Перейти на платный тарифПосмотреть больше похожих видео

LATIHAN SOAL CPNS PPPK 2024 PENGELOLA LAYANAN OPERASIONAL KOMPETENSI TEKNIS/BIDANG/SKB PART 1
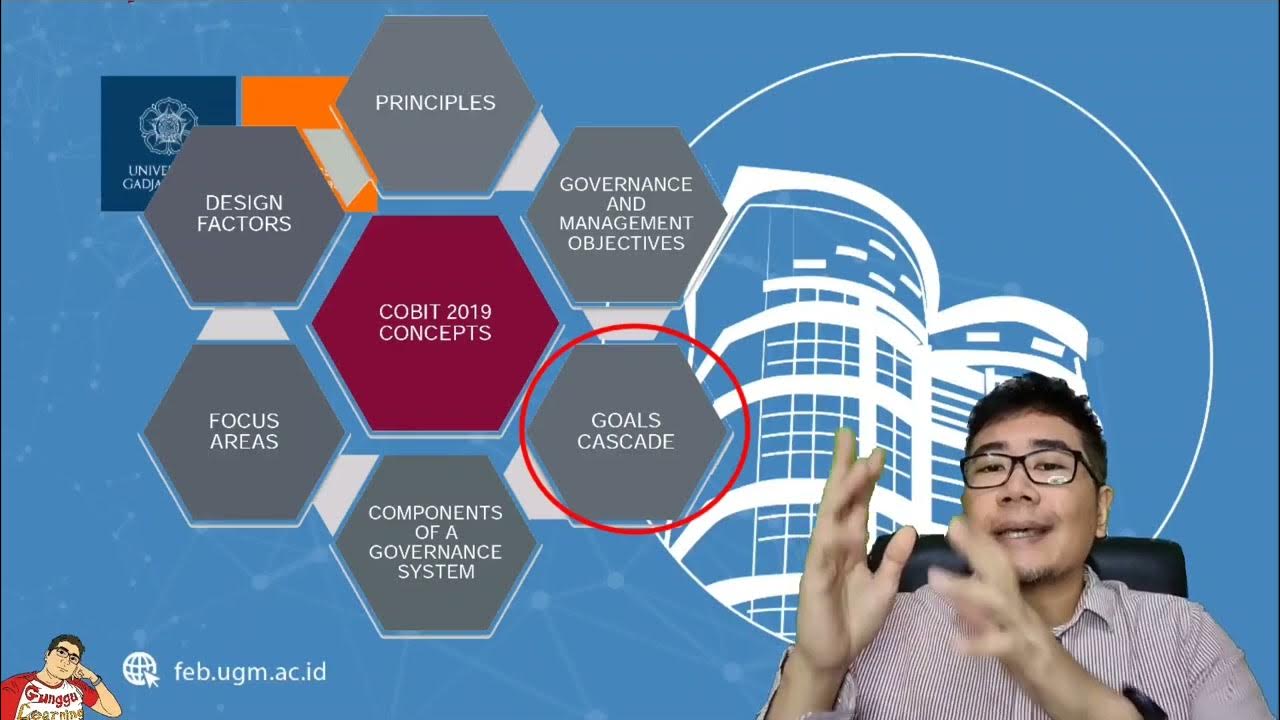
Information Systems Auditing 3b - Information Technology Governance Control (COBIT Framework)

ISO 27001 Risk Assessment: The Ultimate Guide

The Many Areas Of Information Security | Information Security Management Fundamentals Course
AUDIT TI - CONTOH STUDI KASUS DAN ANALISA

Introduction To CyberCrime | Types of Cyber Crime | How To Prevent Cyber Crime | Intellipaat
5.0 / 5 (0 votes)
