Impacket GetUserSPNs & Kerberoasting Explained
Summary
TLDRThis video tutorial delves into the Kerberos Silver Ticket attack technique, demonstrating how to exploit user accounts with Service Principal Names (SPNs) in an Active Directory domain. Using the 'get_userSPNs' script and hashcat, the attacker can capture and decrypt encrypted data to obtain user passwords, all without needing admin rights. The script's process is explained, highlighting the importance of SPNs and the potential risks of setting services to run under user accounts. The tutorial also touches on best practices like using Managed Service Accounts to mitigate such vulnerabilities.
Takeaways
- 😀 The video demonstrates a technique called Kerberos Silver Ticket attack, which exploits user accounts with Service Principal Names (SPNs).
- 🔒 The attack requires initial domain credentials but does not need special permissions like admin rights.
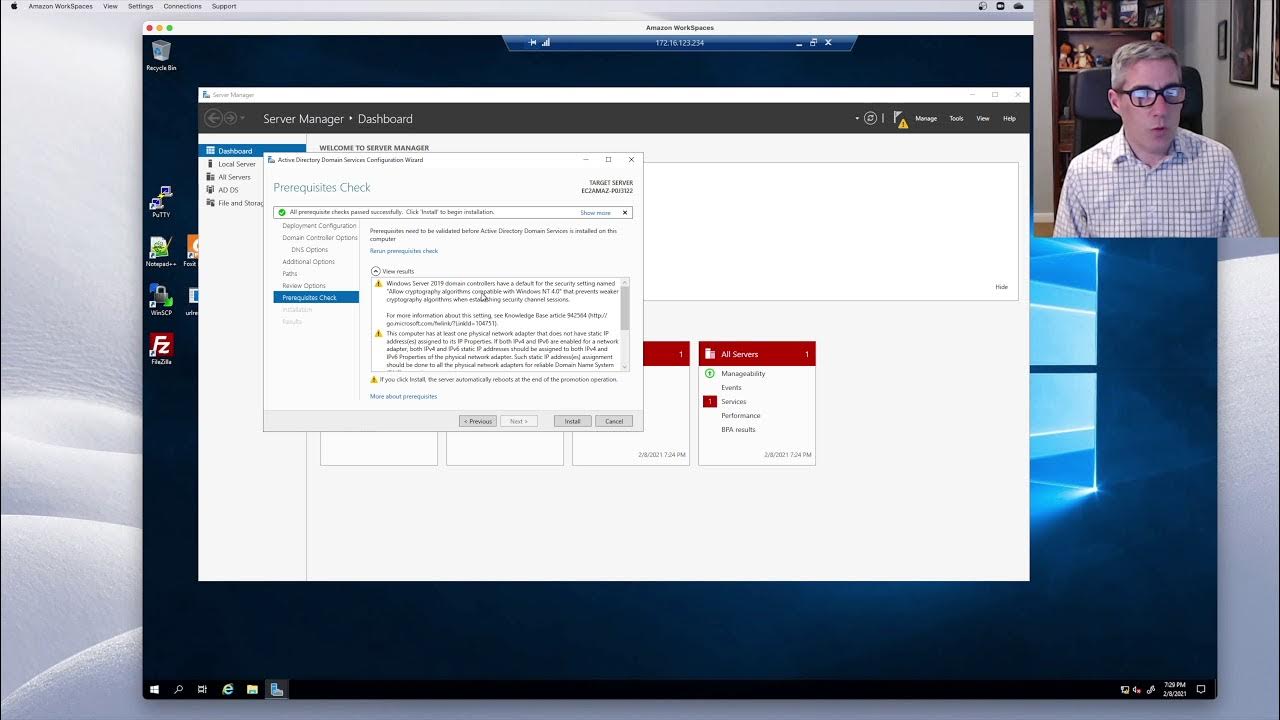
- 🖥️ The setup involves two virtual machines: one acting as a domain controller with Active Directory and the other as an attacker machine separate from the domain.
- 🔎 The 'get_userSPNs' script from Impacket is used to identify user accounts with SPNs, which are then targeted for the attack.
- 🔑 The attack relies on the fact that user accounts often have weaker passwords than computer accounts, making them more susceptible to cracking.
- 🔄 The process includes using Kerberos authentication to request a Ticket-Granting Service (TGS) ticket, which is encrypted with the user's password.
- 📈 The TGS ticket, once cracked using hashcat, reveals the user's password, granting the attacker access to the service the account is running.
- 🛠️ The video mentions the use of managed service accounts or group managed service accounts as a more secure alternative to running services under user accounts.
- 🔗 The script performs an LDAP search to find user accounts with SPNs, which is a crucial step in identifying potential targets for the attack.
- 📚 The video script serves as an educational guide, explaining the technical aspects of the Kerberos Silver Ticket attack in detail.
- 🔮 The video promises a follow-up on Kerberos Silver Tickets, indicating a deeper exploration of the attack technique in subsequent content.
Q & A
What is the Kerberos Silver Ticket attack?
-The Kerberos Silver Ticket attack is a technique where an attacker uses a user's account password to forge a Ticket-Granting Service (TGS) ticket, which can then be used to gain unauthorized access to services within a domain that authenticate using Kerberos.
What is the purpose of using the 'get user SPNs' script in the attack?
-The 'get user SPNs' script is used to identify user accounts that have Service Principal Names (SPNs) assigned to them. These accounts are vulnerable to the attack because they have services that authenticate with Kerberos.
Why is it necessary to have DNS server settings pointing to the domain controller during the attack?
-DNS server settings need to point to the domain controller because Kerberos authentication requires the use of fully qualified domain names (FQDNs). Correct DNS settings ensure that the attacker can resolve the domain controller's FQDN and perform the attack correctly.
What is the significance of the user account having a service principle name (SPN)?
-A user account with an SPN is significant because it indicates that the account is associated with a service that authenticates with Kerberos. This makes the account a potential target for the Kerberos Silver Ticket attack.
What is the role of hashcat in the Kerberos Silver Ticket attack?
-Hashcat is a password cracking tool used in the attack to decrypt the encrypted data obtained from the Kerberos TGS request. Once decrypted, the user's password can be revealed, allowing the attacker to forge tickets.
Why are computer accounts not targeted in the Kerberos Silver Ticket attack?
-Computer accounts are not targeted because they have very long and complex passwords that are automatically changed by the system every 30 days. Cracking these passwords is impractical due to their length and complexity.
How does the attacker use the cracked user account password in the context of the attack?
-Once the user account password is cracked, the attacker can use it to forge a TGS ticket, pretending to be that user and gaining access to services that the user account has access to within the domain.
What is the difference between using a user account and a managed service account to run a service?
-A user account may have a simple password and can be used to run a service with Kerberos authentication. A managed service account, on the other hand, has a long, complex password that is automatically changed, making it more secure and less susceptible to attacks like the Kerberos Silver Ticket attack.
Why might an administrator set a service to run as a user account?
-An administrator might set a service to run as a user account to grant specific permissions to access resources across the network. This allows for more granular control compared to running the service as a local system or network service account.
What is the next step or related attack after successfully performing a Kerberos Silver Ticket attack?
-After successfully performing a Kerberos Silver Ticket attack, the next step or related attack could be a Pass-the-Hash attack or escalating privileges within the domain using the compromised user account.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード関連動画をさらに表示

HackTheBox - Forest (Active Directory) | Noob To OSCP Episode #25

GetNPUsers & Kerberos Pre-Auth Explained

🛡️ Deep Dive: BadSuccessor – Full Active Directory Compromise
Active Directory: Episode1 - Installing a first Domain Controller in Server 2019

Troubleshooting the most common Active Directory account issues | Real World IT Tickets

Securing Active Directory
5.0 / 5 (0 votes)
