Password Security - CompTIA Security+ SY0-701 - 4.6
Summary
TLDRThe video script emphasizes the importance of creating strong passwords with high entropy to prevent guessing and attacks like brute force. It suggests using a mix of upper and lower case letters, numbers, and special characters, and recommends a minimum length of eight characters. Passwords should be unique per account and changed regularly, with expirations enforced by systems. Password managers can securely store and generate these passwords, while passwordless authentication methods are gaining popularity for added security. The script also touches on just-in-time permissions for temporary administrative access, enhancing security in IT environments.
Takeaways
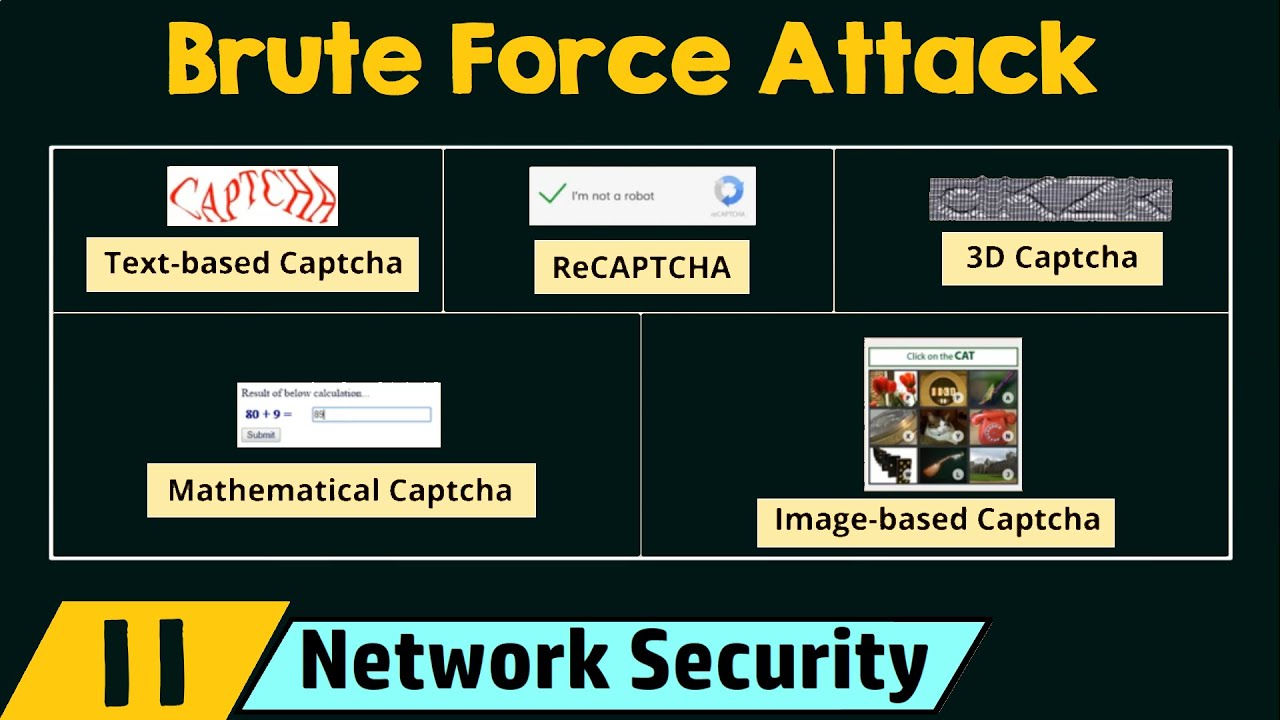
- 🔒 Creating a password with high entropy is crucial for security against guessing and brute force attacks.
- 🔡 A strong password should include a mix of uppercase and lowercase letters, numbers, and special characters.
- 📏 Passwords are often recommended to be at least eight characters long, with some systems requiring even longer for enhanced security.
- ⏳ Passwords have an expiration age, after which they must be changed to maintain security.
- 🔔 Users are typically notified before their password expires, prompting them to update it to maintain access.
- 🚫 Systems may prevent the reuse of old passwords to enhance security.
- 🔑 Using a different password for each account can prevent a single breach from compromising multiple accounts.
- 🗝️ Password managers can securely store multiple passwords, requiring strong access credentials to use them.
- 🛡️ Password managers often offer features to generate strong, unique passwords automatically.
- 🕊️ Some systems are moving towards passwordless authentication methods to eliminate the risks associated with password reuse.
- 🌐 In enterprise environments, just-in-time permissions can provide temporary administrative access based on security policies, reducing the risk of constant high-level access.
- 🛡️ Central clearinghouses or password vaults manage primary credentials and issue temporary, controlled access to systems.
Q & A
Why is it important to create a password that is difficult to guess?
-Creating a difficult-to-guess password helps prevent attackers from using password spraying or brute force attacks, thereby increasing the security of the account.
What does entropy mean in the context of passwords?
-Entropy in passwords refers to the measure of unpredictability of the password, indicating how hard it is to guess or crack.
What are the recommended components for a strong password?
-A strong password should include a mix of uppercase and lowercase letters, numbers, and special characters to increase its complexity and security.
What is the minimum recommended length for a password?
-The minimum recommended length for a password is at least eight characters, although requirements are increasing as systems become more efficient.
Why might systems encourage the use of a phrase for a password?
-Using a phrase or set of words can result in a longer password, which tends to be more secure and easier to remember than a random string of characters.
What is the purpose of password expiration policies?
-Password expiration policies are in place to force users to change their passwords periodically, reducing the risk of password reuse and increasing account security.
What is the consequence of not changing an expired password?
-If a password is not changed after it expires, the user will be unable to log in to the account, as many systems enforce password changes for security reasons.
Why is it advised to use a different password for each account?
-Using a different password for each account prevents an attacker from gaining access to multiple accounts if one password is compromised.
What is a password manager and how does it help with password security?
-A password manager is a tool that securely stores all of a user's passwords in one encrypted database, simplifying the process of managing multiple unique passwords and enhancing security.
What is the advantage of using a password manager for generating new passwords?
-Password managers can automatically generate new, random, and unique passwords for each site, reducing the risk of password reuse and making it easier for users to maintain strong security practices.
What is passwordless authentication and how does it differ from traditional password use?
-Passwordless authentication is a method of logging into a system without using a password, often employing biometrics or personal identification numbers. It eliminates the risk of password reuse and the need to remember multiple passwords.
What is just-in-time permissions and how does it enhance security in IT environments?
-Just-in-time permissions is a security practice where users receive temporary administrative access for a limited time using a set of temporary credentials. This reduces the risk of unauthorized access and potential breaches.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード5.0 / 5 (0 votes)