34. OCR GCSE (J277) 1.3 The concept of layers
Summary
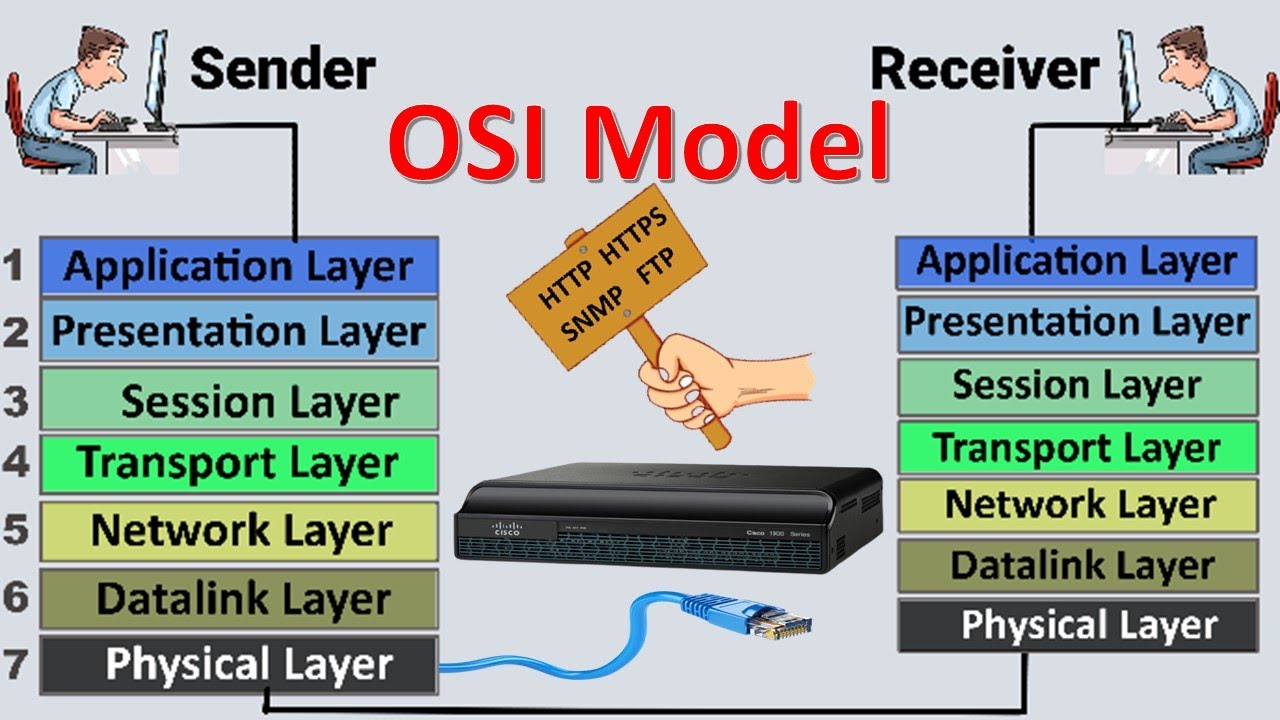
TLDRThis video delves into the intricacies of networking layers, simplifying the complex process of data transfer. It explains how tasks like web browsing, email, and file transfer are managed through different layers, ensuring security and efficiency. The script uses the TCP/IP protocol stack as a framework, illustrating data's journey from source to destination, detailing how each layer—application, transport, network, and link—adds necessary headers and addresses for successful communication, ultimately making the internet work seamlessly.
Takeaways
- 🌐 Networking involves complex operations including applications, security, user authentication, and data transfer.
- 🔐 Security is a key aspect, involving encryption and ensuring data integrity during transfer.
- 🌐 Connectivity involves remote servers, load balancing, and maintaining open connections.
- 💻 Networking methods include peer-to-peer and client-server, each with its own advantages and use cases.
- 📦 Data is often split into packets and frames for efficient transmission and error checking.
- 🛤 Different types of cables (fibre, twisted pair, coaxial) and wireless technologies are used for data transmission.
- 📶 Duplex communication can be simplex, half-duplex, or full-duplex, affecting how data is sent.
- 🔑 The concept of layers simplifies networking by breaking down complex problems into manageable sub-problems.
- 🤝 Layered networking allows devices from different vendors to work together seamlessly.
- 🌐 The TCP/IP protocol stack is crucial for modern networking, enabling communication across networks and the internet.
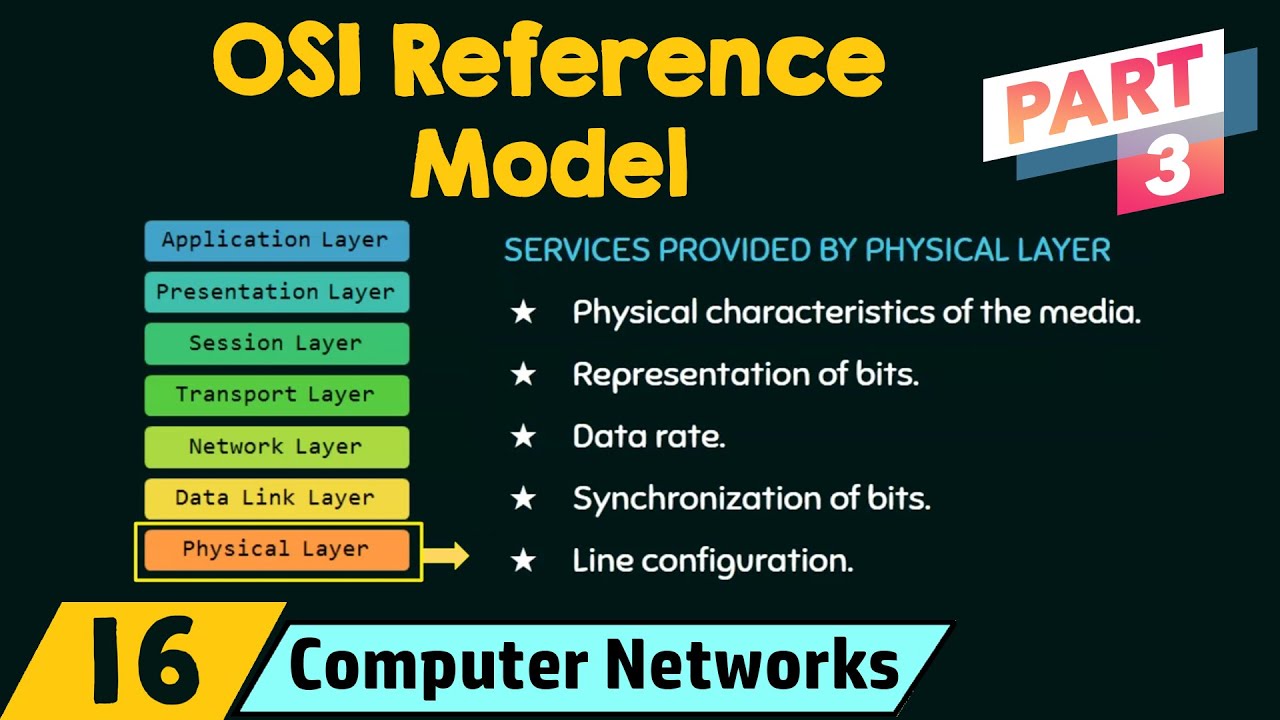
- 📈 Each layer in the TCP/IP stack has a specific role, from application-specific protocols to physical connections.
Q & A
What is the primary purpose of dividing networking into layers?
-The primary purpose of dividing networking into layers is to simplify the complexity of transferring data between two points by breaking down the problem into smaller, more manageable sub-problems.
How does layering help with the interoperability of different devices?
-Layering helps with interoperability by allowing devices to operate at a specific layer without needing to understand the details of other layers, enabling products from different vendors to work together seamlessly.
What are the different methods mentioned for data transfer in the script?
-The script mentions peer-to-peer and client-server methods as different approaches for data transfer.
What is the significance of packet sequencing in networking?
-Packet sequencing is significant because it allows the receiving computer to reassemble packets in the correct order, even if they arrive out of sequence during transmission.
What is the role of the transport layer in the TCP/IP protocol stack?
-The transport layer is responsible for establishing an end-to-end connection and splitting the data into packets, adding packet numbers and port numbers to ensure correct reassembly at the destination.
Why is the network layer sometimes referred to as the internet layer?
-The network layer is sometimes referred to as the internet layer because it uses the IP part of the TCP/IP protocol to route packets from one node to another across the internet.
What does the link layer add to each packet before sending it out on the network?
-The link layer adds the MAC address, including both the source and destination MAC addresses, to each packet before sending it out on the network.
How does the concept of 'duplex' relate to data transmission as mentioned in the script?
-Duplex refers to the ability to transmit data in both directions simultaneously (full duplex), in one direction at a time (half duplex), or only in one direction (simplex).
What is the function of the application layer in the context of sending a web page over the internet?
-The application layer uses an appropriate protocol related to the application being used, such as HTTP or HTTPS, to prepare the data for transmission and add headers to indicate the application needed to process the data at the receiving end.
Why is error-checking important in the process of sending data over a network?
-Error-checking is important to ensure data integrity. If errors are detected, the receiving device can request that the data be resent, ensuring that the data received is accurate and complete.
How does the router play a role in the process of data transmission as described in the script?
-Routers play a crucial role by receiving packets, stripping off the outer layer, and passing them up to the network layer to determine the next hop. They then repackage the packets with their own MAC address and the destination MAC address, and forward them towards their final destination.
Outlines

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードMindmap

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードKeywords

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードHighlights

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレードTranscripts

このセクションは有料ユーザー限定です。 アクセスするには、アップグレードをお願いします。
今すぐアップグレード5.0 / 5 (0 votes)